Source: www.darkreading.com – Author: Alex Haynes Alex Haynes, Chief Information Security Officer, IBS Software March 15, 2024 5 Min Read Source: Blackboard via Alamy Stock Photo...
Month: March 2024
6 CISO Takeaways From the NSA’s Zero-Trust Guidance – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Olivier Le Moal via Shutterstock The reality of cybersecurity for companies is that adversaries compromise systems and...
Red Canary Announces Full Coverage of All Major Cloud Providers – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE DENVER, March 5, 2024 – Red Canary today announced full coverage of its detection and response capabilities to include all...
Expel Releases Updated Toolkit in Response to NIST 2.0 – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE HERNDON, Va., March 13, 2024 — (BUSINESS WIRE) — Expel, the leading managed detection and response (MDR) provider, today unveiled...
Nozomi Networks Secures $100M Investment to Defend Critical Infrastructure – Source: www.darkreading.com
Source: www.darkreading.com – Author: SAN FRANCISCO, March 13, 2024 — Nozomi Networks Inc. today announced a $100 million Series E funding round to help accelerate innovative...
FCC Approves Voluntary Cyber Trust Labels for Consumer IoT Products – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: 1800 JIRAROJ PRADITCHAROENKUL via Alamy Stock Photo The Federal Communications Commission (FCC) will be rolling out a...
Fortinet Warns of Yet Another Critical RCE Flaw – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer 3 Min Read Source: Postmodern Studio via Shutterstock Fortinet has patched a critical remote code execution (RCE) vulnerability...
Alabama Under DDoS Cyberattack by Russian-Backed Hacktivists – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff 1 Min Read Source: Illustrated History via Alamy Stock Photo Alabama has been grappling with network disruptions, following cyber...
StopCrypt: Most widely distributed ransomware now evades detection – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new variant of StopCrypt ransomware (aka STOP) was spotted in the wild, employing a multi-stage execution process that involves...
SIM swappers hijacking phone numbers in eSIM attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas SIM swappers have adapted their attacks to steal a target’s phone number by porting it into a new eSIM card,...
Tech support firms Restoro, Reimage fined $26 million for scare tactics – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Tech support companies Restoro and Reimage will pay $26 million to settle charges that they used scare tactics to trick...
Google Chrome gets real-time phishing protection later this month – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Google will roll out a Safe Browsing update later this month that will provide real-time malware and phishing protection to...
French unemployment agency data breach impacts 43 million people – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas France Travail, formerly known as Pôle Emploi, is warning that hackers breached its systems and may leak or exploit personal...
Nissan confirms ransomware attack exposed data of 100,000 people – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Nissan Oceania is warning of a data breach impacting 100,000 people after suffering a cyberattack in December 2023 that was...
Windows 11 gets single Teams app for work and personal accounts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft will soon provide a single Teams Windows and macOS app for all account types, allowing users to switch between...
Hackers exploit Windows SmartScreen flaw to drop DarkGate malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new wave of attacks by the DarkGate malware operation exploits a now-fixed Windows Defender SmartScreen vulnerability to bypass security...
US govt probes if ransomware gang stole Change Healthcare data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The U.S. Department of Health and Human Services is investigating whether protected health information was stolen in a ransomware attack...
Fortinet warns of critical RCE bug in endpoint management software – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Fortinet patched a critical vulnerability in its FortiClient Enterprise Management Server (EMS) software that can allow attackers to gain remote...
How Autonomous Vehicles are Revolutionizing the Last-Mile Logistics Industry – Source: www.cyberdefensemagazine.com
Source: www.cyberdefensemagazine.com – Author: News team Cybersecurity will be one of the key concerns as last-mile logistics companies look to enhance efficiency with autonomous vehicles. By...
5M WordPress Websites At Risk Amid LiteSpeed Plugin Flaw – Source: securityboulevard.com
Source: securityboulevard.com – Author: Wajahat Raja A highly sensitive flaw has been identified in the LiteSpeed plugin of WordPress, which has put as many as 5...
Edgeless Systems Brings Confidential Computing to AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Edgeless Systems today launched a Continuum platform that applies confidential computing to artificial intelligence (AI) workloads to better secure them....
HHS to Investigate Change’s Security in Wake of Crippling Cyberattack – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The U.S. Department of Health and Human Services (HHS) is opening an investigation into UnitedHealth and its Change Healthcare subsidiary...
Guarding Your Business: A Guide to Employee Training for Cybersecurity Vigilance – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ainsley Lawrence Protecting your business from scams and cybersecurity threats not only bolsters your business’s practices but also maintains your client’s trust....
USENIX Security ’23 – Guangke Chen, Yedi Zhang, Zhe Zhao, Fu Song – QFA2SR: Query-Free Adversarial Transfer Attacks to Speaker Recognition Systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX Security ’23 – Guangke Chen, Yedi Zhang, Zhe Zhao, Fu...
Envisioning a mobile-powered government workforce – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jacob Hughes ATARC’s Future of Secure Work Working Group, of which Privoro’s Heather McMahon is a member, recently published a white paper...
Microsoft’s February 2024 Patch Tuesday Addresses 2 Zero-Days and 73 Vulnerabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire Microsoft’s Patch Tuesday for March 2024 has once again highlighted the importance of regular updates in maintaining the security of...
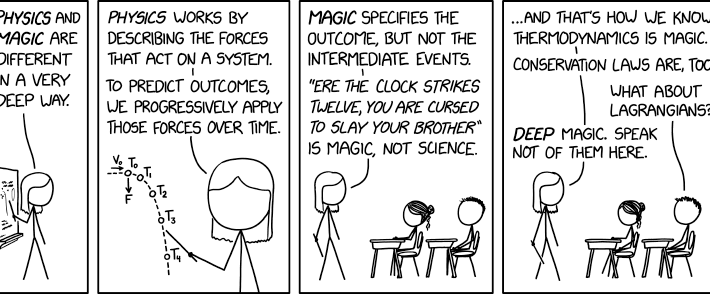
Randall Munroe’s XKCD ‘Physics vs. Magic’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe, creator of XKCD Permalink *** This is a Security Bloggers...
Google Splashes the Cash in Bug Bounty Bonanza: $59 Million to Date – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Last year, $GOOG paid $10 million to ethical hackers for finding vulnerabilities. Google announced its 2023 payout tally for the Vulnerability...
Feds Launch Investigation into Change Healthcare Attack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , HIPAA/HITECH , Industry Specific HHS OCR Tells UnitedHealth Group it Will Scrutinize Co.’s HIPAA Compliance Marianne Kolbasuk McGee (HealthInfoSec)...
The Critical Role of Effective Onboarding – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Leadership & Executive Communication , Recruitment & Reskilling Strategy , Training & Security Leadership How Your Onboarding Process Can Help Improve...