Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Social Media Treasury Department Sanctions Heads of Russian ‘Influence-for-Hire’ Firms Chris Riotta (@chrisriotta) • March 20,...
Month: March 2024
Webinar | Hackers’ Holy Grail: Insights into the Compromised Credentials Crisis – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 James Condon Director of Security Research, Lacework James Condon is Director of Security Research at Lacework, where he leads the Lacework...
Live Webinar | Attack Surface Management: Actionable Insights Against New, Known and Unknown Threats – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Chris Poulin Director of Technology and Strategy and Deputy CTO, Bitsight Chris Poulin has over 35 years of experience in information...
US CISA Urges Preventative Actions Against Volt Typhoon – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Make Sure You Have Logs, Five Eyes Alliance Says Mihir Bagwe (MihirBagwe)...
Email Bomb Attacks: Filling Up Inboxes and Servers Near You – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 DDoS Protection , Email Security & Protection , Fraud Management & Cybercrime HHS: Bot-Driven Attacks Can Overwhelm Email Servers, Networks and...
‘Fluffy Wolf’ Spreads Meta Stealer in Corporate Phishing Campaign – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Marco Arduino via Alamy Stock Photo An emerging and unsophisticated threat actor is spreading various types of...
Understanding Your Attack Surface: AI or bust – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aravind Iyengar Creating an accurate inventory of an organization’s assets and applications while ensuring no duplicates or omissions is essential for any...
Quantum Computing: A New Dawn for Encryption Vulnerabilities – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Encryption & Key Management , Fraud Management & Cybercrime Expert Perspectives on Protecting Data and Developing Quantum-Safe Cryptography Michael...
Live Webinar | Identity Security in 2024: The Key to Compliance in Today’s Regulatory Landscape – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Jeff Purrington Advisory Strategist, SailPoint Jeff is an Identity Strategist with SailPoint with experience in Identity Security, as well as many...
AI Infused with XDR, SIEM, and Threat Intelligence Set to Reshape Cybersecurity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Microsoft Security Copilot , Next-Generation Technologies & Secure Development Information Security Media Group • March 18, 2024 Today’s security...
Ransomware Groups: Trust Us. Uh, Don’t. – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware Review of Attacks Finds Inconsistent Data Leaks and Victim Naming, Broken Promises Mathew J. Schwartz...
A Career in Combating Cryptocurrency Scams – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cryptocurrency Fraud , Fraud Management & Cybercrime , Fraud Risk Management We Need Cryptocurrency Forensics Now More Than Ever Before Steve...
Planning for Healthcare IT Resiliency on a Regional Basis – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 It’s critical for hospitals and other firms to not only prepare for how they will respond to a cyberattack, but also...
Properly Vetting AI Before It’s Deployed in Healthcare – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , AI-Based Attacks , Artificial Intelligence & Machine Learning Attorney Lee Kim of HIMSS Discusses Evolving Tech...
Protecting Medical Devices Against Future Cyberthreats – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare organizations and makers of medical devices need to think about how to safeguard their critical medical gear against future cyberthreats,...
Transforming a Cyber Program in the Aftermath of an Attack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 CISO Trainings , Incident & Breach Response , Next-Generation Technologies & Secure Development Mark Johnson, CISO of Hackensack Meridian Health, Describes...
Webinar | Compromised Credentials in 2024: What to Know about the World’s #1 Attack Vector – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 James Condon Director of Security Research, Lacework James Condon is Director of Security Research at Lacework, where he leads the Lacework...
5 Ways CISOs Can Navigate Their New Business Role – Source: www.darkreading.com
Source: www.darkreading.com – Author: David Strom Source: Jerome via Alamy Stock Photo Today’s CISOs are under attack from numerous quarters, both within and outside their organizations....
Name That Toon: Bridge the Gap – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist 1 Min Read That bridge you said you’d cross when you’d come to it? Well, time’s up! Come up...
New Regulations Make D&O Insurance a Must for CISOs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Source: designer491 via Alamy Stock Photo Chief information security officers (CISOs) face a number of daily challenges, including...
‘PhantomBlu’ Cyberattackers Backdoor Microsoft Office Users via OLE – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: David Chapman via Alamy Stock Photo A malicious email campaign is targeting hundreds of Microsoft Office users...
The New CISO: Rethinking the Role – Source: www.darkreading.com
Source: www.darkreading.com – Author: James Doggett 5 Min Read Source: Kjetil Kolbjørnsrud via Alamy Stock Photo COMMENTARY Companies recognize the importance of cybersecurity and increasingly incorporate...
‘Conversation Overflow’ Cyberattacks Bypass AI Security to Target Execs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: Blackboard via Alamy Stock Photo A novel cyberattack method dubbed “Conversation Overflow” has surfaced, attempting to get...
Patch Now: Kubernetes RCE Flaw Allows Full Takeover of Windows Nodes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Dennizn via Alamy Stock Photo A security bug in the widely used Kubernetes container-management system allows attackers...
Why You Need to Know Your AI’s Ancestry – Source: www.darkreading.com
Source: www.darkreading.com – Author: Leo Scott Leo Scott, Chief Innovation Officer, DataTribe March 13, 2024 5 Min Read Source: marcos alvarado via Alamy Stock Photo COMMENTARY...
Critical ChatGPT Plug-in Vulnerabilities Expose Sensitive Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: Mopic via Alamy Stock Photo Three security vulnerabilities unearthed in the extension functions ChatGPT employs open the...
‘PixPirate’ RAT Invisibly Triggers Wire Transfers From Android Devices – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Tithi Luadthong via Alamy Stock Photo A sophisticated Brazilian banking Trojan is using a novel method for...
Fujitsu hack raises questions, after firm confirms customer data breach – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Fujitsu has warned that cybercriminals may have stolen files with personal and customer data after it discovering malware on its...
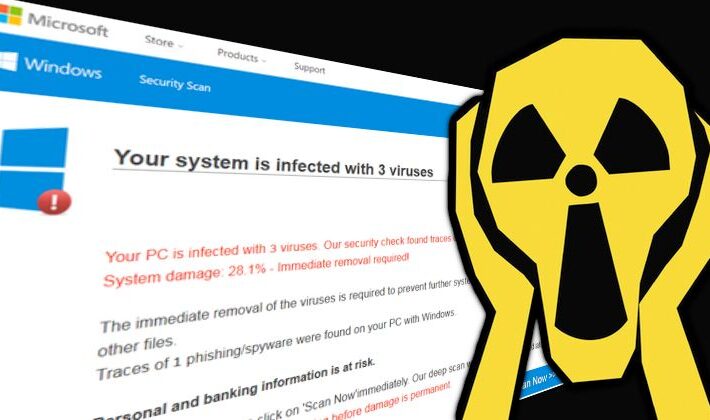
Scareware scam: Restoro and Reimage fined $26 million by FTC – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Two firms have been fined $26 million by the US Federal Trade Commission (FTC) for scaring consumers into believing their...
LockBit affiliate jailed for almost four years after guilty plea – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley An affiliate of the LockBit ransomware gang has been sentenced to almost four years in jail after earlier pleading guilty...