Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: You’ve invested in cyber prevention and defense tools; next-gen firewalls, endpoint detection and response, SIEM, and more. However, despite...
Day: March 29, 2024
Is your outdated WAN putting the brakes on your business? What to watch for – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Peter Elmer, Check Point Office of the CTO and Mor Ahuvia, Check Point Office of the CTO. By 2026, 70% of...
Victim of cyber crime? 7 crucial steps your business should take – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: For a business, falling victim to cyber crime is a disquieting and stressful experience. In the immediate aftermath, there...
GUEST ESSAY: NIST’s Cybersecurity Framework update extends best practices to supply chain, AI – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Jeremy Swenson The National Institute of Standards and Technology (NIST) has updated their widely used Cybersecurity Framework (CSF) — a...
LW ROUNDTABLE: Will the U.S. Senate keep citizens safe, vote to force China to divest TikTok? – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido Congressional bi-partisanship these day seems nigh impossible. Related: Rising tensions spell need for tighter cybersecurity Yet by...
Author Q&A: A patient’s perspective of advanced medical technology and rising privacy risks – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido A close friend of mine, Jay Morrow, has just authored a book titled “Hospital Survival.” Related: Ransomware...
GUEST ESSAY: A DIY guide to recognizing – and derailing – Generative AI voice scams – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Alexander Konovalov Americans lost a record $10 billion to scams last year — and scams are getting more sophisticated. Related: Google battles...
News alert: Badge expands availability of ‘Enroll Once and Authenticate on Any Device’ software – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cyberwire San Francisco, Calif., Mar. 7, 2024 — Badge Inc., the award-winning privacy company enabling Identity without Secrets™, today launched a new Partner...
GUEST ESSAY: Essential cyber hygiene practices all charities must embrace to protect their donors – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Zac Amos Charities and nonprofits are particularly vulnerable to cybersecurity threats, primarily because they maintain personal and financial data, which...
News alert: Silence Laboratories raises $4.1M for new privacy-preserving cryptography platform – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido SINGAPORE – Feb. 29, 2024. In the modern age, large companies are wrestling to leverage their customers’ data to provide ever-better...
News alert: Chiral announces $3.8m funding round to advance nanomaterial chip manufacturing – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Zurich, Switzerland, Feb. 27, 2024 — Chipmaking has become one of the world’s most critical technologies in the last two decades....
News alert: ThreatHunter.ai stops hundreds of ransomware attacks, nation-state threats in 48 hours – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: cyberwire Brea, Calif. Feb. 27, 2024 — The current large surge in cyber threats has left many organizations grappling for security so...
SHARED INTEL: Poll shows companies pursuing ‘Digital Trust’ reap benefits as laggards fall behind – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido Achieving “digital trust” is not going terribly well globally. Related: How decentralized IoT boosts decarbonization Yet, more...
LockBit Hacker Sentenced To 4 Years Jail Plus Fined $860K – Source: securityboulevard.com
Source: securityboulevard.com – Author: Wajahat Raja Recent reports about legal proceedings, a 34-year-old Russian-Canadian national, Mikhail Vasiliev, has been handed a sentence of almost four years...
Symmetry Systems Ramps Up Hybrid-Cloud Data Security with $15 Million Series A Funding – Source: securityboulevard.com
Source: securityboulevard.com – Author: wpengine ForgePoint Capital and Prefix Capital Double-Down on Data Store and Object Security as Lead Investors Symmetry Systems, provider of cutting-edge Data...
What is Threat Management? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Pushpendra Mishra Threat management is a process that is used by cybersecurity analysts, incident responders and threat hunters to prevent cyberattacks, detect...
Building Strong Defences: The Intricacies of Effective Bot Mitigation – Part 1 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nick Rieniets Welcome to the first installment of our blog series dedicated to shedding light on the intricacies of bot mitigation. In...
The Importance of User Roles and Permissions in Cybersecurity Software – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kevin Smith How many people would you trust with your house keys? Chances are, you have a handful of trusted friends and...
Tax scams: Scams to be aware of this tax season – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ryan Healey-Ogden However, a government organization would never offer you money through a text message. Most likely, benefits will be given directly...
Apple OTP FAIL: ‘MFA Bomb’ Warning — Locks Accounts, Wipes iPhones – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings First, fatigue frightened users with multiple modal nighttime notifications. Next, call and pretend to be Apple support. Apple is under fire...
AI Apps: A New Game of Cybersecurity Whac-a-Mole | Grip – Source: securityboulevard.com
Source: securityboulevard.com – Author: Grip Security Blog Cybersecurity is much like a relentless game of “whac-a-mole”–the advent of new technologies invariably draws out threats that security...
From Despair to Disruption: Zafran Takes on Cyber Mitigation – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Fraud Management & Cybercrime , Governance & Risk Management Amid COVID-19 Ransomware Woes, Sanaz Yashar’s...
Live Webinar | Secure Your SAP Transformation: An Identity Security Perspective – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Jody Paterson Senior Director of Product, SailPoint The co-founder, CEO and Chairman of ERP Maestro, inc (The first cloud based SAP...
Turning to a Career in Cybersecurity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Training & Security Leadership Cyberthreats Are Rampant, Expertise Is Needed, and the Rewards Are Great Steve King • March 27, 2024...
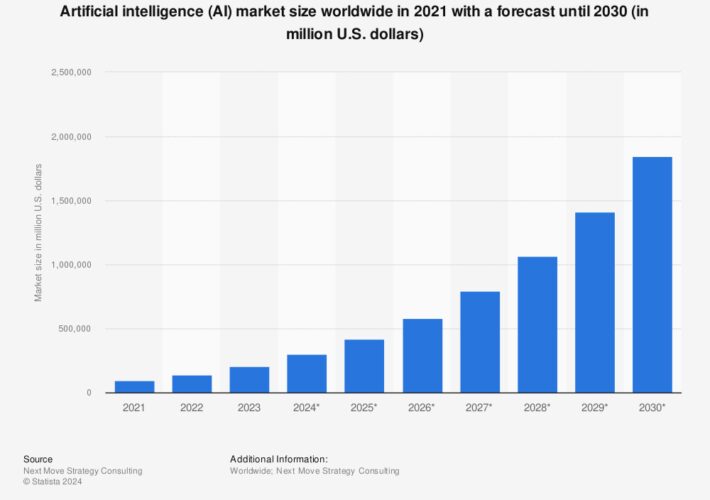
How AI Is Shaping an Inclusive and Diverse Future – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific AI’s Transformative Impact and Challenges in Developing Regions AmitKumar Shrivastava •...
Feds Seek Secure-by-Design Armageddon for SQL Injection Bugs – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management Hackers Continue to Abuse Easily Preventable Vulnerability to Cause Massive Damage Mathew J. Schwartz (euroinfosec) • March...
How Okta and AWS Customers Integrate with their Tech Stack of Choice – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Federal Elections Commission Considers Regulating AI – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific FEC Commissioner Says Group Is Exploring How to Regulate Campaign Deepfakes...
Bolstering Australia’s Security Posture with Accelerated ZTNA – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
OnDemand | 1 in 3 Breaches Go Undetected: Strengthen Your Defense Against Identity Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Digital Identity , Identity & Access Management , Security Operations Insights from recent cyberattacks where weak authentication measures were circumvented March...