The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Month: February 2024
HR Top Priorities for 2024
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Guide to Technical and Organisational Data Protection
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Global Internal Audit Standards 2024
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Global Cyber Security Trends
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Generative AI The Data Protection Implications
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybervergent Cybersecurity Annual Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Career Roadmap
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Security in Supplier Relationships Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TRAINING PROGRAM {CAPTURE THE FLAG}
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Code of Best Practices of Corporate Governance
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cloud & Compromise Gamifying of Cloud Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
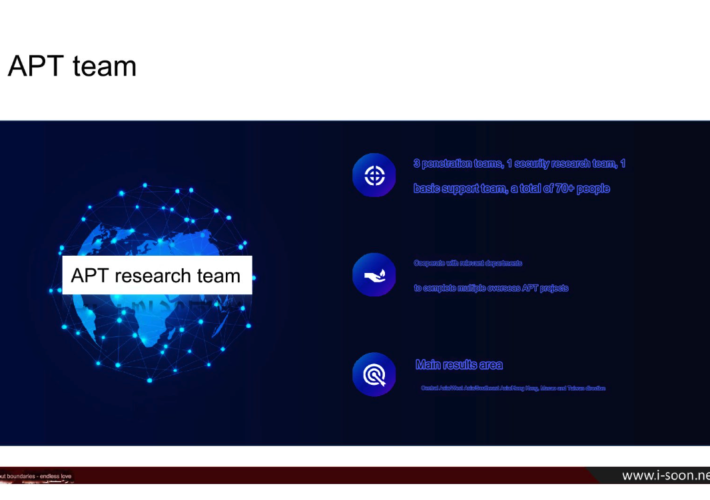
New Leak Shows Business Side of China’s APT Menace – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs A new data leak that appears to have come from one of China’s top private cybersecurity firms provides a rare glimpse...
SMBs at Risk From SendGrid-Focused Phishing Tactics – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity experts at Kaspersky have uncovered a new phishing campaign that specifically targets small and medium-sized businesses (SMBs). The attack method...
Change Healthcare Cyber-Attack Leads to Prescription Delays – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Health tech firm Change Healthcare, part of Optum, has been hit by a cyber-attack, leading to delays in prescriptions being issued...
Russian-Aligned Network Doppelgänger Targets German Elections – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A joint effort by SentinelLabs and ClearSky Cyber Security has uncovered a significant propaganda and disinformation campaign, possibly orchestrated by the...
OWASP Releases Security Checklist for Generative AI Deployment – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Written by Chief information security officers now have a new tool at their disposal to get started with AI securely. The...
Cyber Pros Embrace AI, Over 80% Believe It Will Enhance Jobs – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Most cybersecurity professionals believe that AI will have a positive impact on their jobs, helping alleviate pressures caused by the cyber...
Chinese Duo Found Guilty of $3m Apple Fraud Plot – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Two Chinese nationals have been found guilty of running a sophisticated fraud scheme in which they attempted to con Apple out...
Ransomware Warning as CVSS 10.0 ScreenConnect Bug is Exploited – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 IT admins have been urged to patch any on-premises ScreenConnect servers immediately, after reports that a recently published maximum severity vulnerability...
Businesses Increase Cybersecurity as Budgets Surge in 2024 – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity is a top concern for businesses in 2024, with over two-thirds of IT decision-makers reporting increased budgets. This positive trend...
6 Best Open Source IAM Tools in 2024 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Franklin Okeke We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
New Image/Video Prompt Injection Attacks – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog New Image/Video Prompt Injection Attacks Simon Willison has been playing with the video processing capabilities of the new Gemini...
‘Lucifer’ Botnet Turns Up the Heat on Apache Hadoop Servers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Cultura Creative Ltd via Alamy Stock Photo A threat actor is targeting organizations running Apache Hadoop and...
‘VoltSchemer’ Hack Allows Wireless Charger Takeovers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Fusssergei via Adobe Stock Researchers from the University of Florida, alongside CertiK, have come up with a theoretical...
Critical ConnectWise RMM Bug Poised for Exploitation Avalanche – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: RGB Ventures/SuperStock via Alamy Stock Photo Users of the ConnectWise ScreenConnect remote desktop management...
El Al Flight Crew Suffers Midflight Communication Disruption – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Markus Mainka via Alamy Stock Photo “Hostile elements” last week reportedly tried to take over communications on an...
DoT, White House Tackle the Chinese Threat to US Port Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Jack Sullivan via Alamy Stock Photo The Department of Transportation (DoT) issued a warning today about the...
Smashing Security podcast #360: Lockbit locked out, and funeral Facebook scams – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Heaven’s above! Scammers are exploiting online funerals, and Lockbit – the “Walmart of Ransomware” – is dismantled in style by...
Cloud-Native Data Security Posture Management Deployments on AWS with Symmetry Systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: claude.mandy This blog originally appeared here: https://aws.amazon.com/blogs/apn/cloud-native-data-security-posture-management-deployments-on-aws-with-symmetry-systems/ With Amazon Web Services (AWS), you can manage the privacy of your data, control how it’s...