Source: grahamcluley.com – Author: Graham Cluley Your smartphone may be toast – if you use a hacked wireless charger, we take a closer look at the...
Day: February 28, 2024
How to interpret the MITRE Engenuity ATT&CK® Evaluations: Enterprise – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Graham Cluley Security News is sponsored this week by the folks at Cynet. Thanks to the great team there for...
Matthew Perry’s Twitter account hacked by cryptocurrency scammers – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Matthew Perry’s official Twitter account was hijacked by scammers this week who attempted to solicit donations from well-meaning fans of...
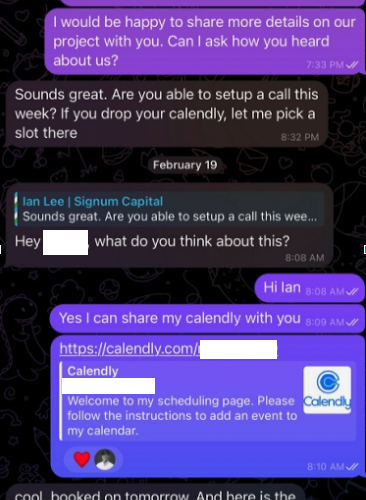
Calendar Meeting Links Used to Spread Mac Malware – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Malicious hackers are targeting people in the cryptocurrency space in attacks that start with a link added to the target’s calendar...
‘Illusive’ Iranian Hacking Group Ensnares Israeli, UAE Aerospace and Defense Firms – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Zoonar GmbH via Alamy Stock Photo An Iranian Revolutionary Guard Corps (IGRC)-linked threat group is staging political...
Kaspersky Finds Attacks on Mobile Devices Significantly Increased in 2023 – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Woburn, MA – February 26, 2024 — In 2023, Kaspersky observed a steady increase in the number of attacks on mobile devices, reaching almost...
U-Haul Reports 67K Customers Impacted by Data Breach – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: LH Images via Alamy Stock Photo U-Haul — a truck, trailer, and self-storage rental company based in Arizona...
Russia’s ‘Midnight Blizzard’ Targets Service Accounts for Initial Cloud Access – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: PopTika via Shutterstock “Midnight Blizzard,” the threat group affiliated with Russian intelligence services (SVR) and the entity...
Apple, Signal Debut Quantum-Resistant Encryption, but Challenges Loom – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Production Perig via Shutterstock Apple’s new PQ3 post-quantum cryptographic (PQC) protocol introduced last week is the latest...
Mexico’s ‘Timbre Stealer’ Campaign Targets Manufacturing – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Tom King via Alamy Stock Photo Cybercriminals are spreading a new infostealer across Mexico by catching targets...
UAC-0184 Targets Ukrainian Entity in Finland With Remcos RAT – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: David Chapman via Alamy Stock Photo The threat actor tracked as UAC-0184 has been using steganography techniques...
NIST Releases Cybersecurity Framework 2.0 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Borka Kiss via Alamy Stock Photo After several years of deliberation, the National Institute for Standards and Technology...
The Next Gen of Cybersecurity Could Be Hiding in Big Tech – Source: www.darkreading.com
Source: www.darkreading.com – Author: Yaniv Vardi Source: Federico Caputo via Alamy Stock Photo COMMENTARY The world is facing an unprecedented number of cyber threats and historic...
A Cyber Insurance Backstop – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier In the first week of January, the pharmaceutical giant Merck quietly settled its years-long lawsuit over whether or not its...
China Surveillance Company Hacked – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog China Surveillance Company Hacked Last week, someone posted something like 570 files, images and chat logs from a Chinese...
New Vulnerabilities in ConnectWise ScreenConnect Massively Exploited by Attackers – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cedric Pernet Two new vulnerabilities impact ConnectWise ScreenConnect, remote desktop and access software used for support: CVE-2024-1709 and CVE-2024-1708, with the former...
Synopsys Report Exposes Extent of Open Source Software Security Risks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard A report published today by Synopsys finds nearly three-quarters (74%) of the 1,067 commercial codebases scanned contain open source components...
Survey on 2024 IoT Security Crisis – Source: securityboulevard.com
Source: securityboulevard.com – Author: John Gallagher Surveys play an important role in setting strategy and choosing how to address a difficult situation. Organizations today are urgently...
Why School Districts Should Consider a Team of First Responders for Cyber Threats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kevin Smith Most school districts are equipped to deal with an emergency—whether it’s a disgruntled parent lobbying for change, an environmental disaster,...
USENIX Security ’23 – ClepsydraCache – Preventing Cache Attacks with Time-Based Evictions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Jan Philipp Thoma, Christian Niesler, Dominic Funke, Gregor Leander, Pierre Mayr, Nils Pohl, Lucas Davi, Tim Güneysu Many thanks...
News alert: ThreatHunter.ai stops hundreds of ransomware attacks, nation-state threats in 48 hours – Source: securityboulevard.com
Source: securityboulevard.com – Author: cyberwire Brea, Calif. Feb. 27, 2024 — The current large surge in cyber threats has left many organizations grappling for security so...
US Will Fight Russian Disinformation — Hacks and Leaks and Deepfakes, Oh My! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings State Dept. Global Engagement Centre chief James Rubin (pictured) follows the yellow brick road. The U.S. State Department wants to fight election...
Major Cyberattack on UnitedHealth’s Optum Causes Widespread Healthcare Billing Disruption – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire UnitedHealth Group, the largest healthcare company in the world by revenue, has confirmed its subsidiary Optum recently experienced a significant...
Azure Password Self-Service Management Solutions: Which is Best? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lee Painter It goes without saying that password management is essential to online security, whether for a personal social media account or...
Password Fatigue: How To Avoid It – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lee Painter Many employees at all kinds of businesses can suffer from password fatigue. It is a very real problem, which can...
Response to CISA Advisory (AA24-057A): SVR Cyber Actors Adapt Tactics for Initial Cloud Access – Source: securityboulevard.com
Source: securityboulevard.com – Author: Francis Guibernau On February 26, 2024, the Cybersecurity & Infrastructure Security Agency (CISA) released a Cybersecurity Advisory (CSA) detailing recent Tactics, Techniques,...
EU to Analyze Partnership Between Microsoft and Mistral AI – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Microsoft Announces $16.3 Million Investment in French AI Firm Akshaya...
Report Says Iranian Hackers Targeting Israeli Defense Sector – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development Hackers Are Leveraging Israel-Hamas War to...
Moscow Military Hackers Used Microsoft Outlook Vulnerability – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Endpoint Security , Fraud Management & Cybercrime APT28 Used Hacked Ubiquiti Routers for Hashed Password Relay...
What Goes Around Comes Back Around, With Chatbots Too – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Study Shows Correlation Between Polite Language, Culture and LLM Output...