Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Artemis Diana via Alamy The passwordless technology known as passkeys remains esoteric, far from widespread adoption, and...
Month: January 2024
Juniper warns of critical RCE bug in its firewalls and switches – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Juniper Networks has released security updates to fix a critical pre-auth remote code execution (RCE) vulnerability in its SRX Series...
Ivanti Connect Secure zero-days exploited to deploy custom malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Hackers have been exploiting the two zero-day vulnerabilities in Ivanti Connect Secure disclosed this week since early December to deploy multiple...
Major T-Mobile outage takes down account access, mobile app – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Updates added below. A major T-Mobile outage is preventing customers from logging into their accounts and using the company’s mobile app....
The Art of Risk Management
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
6 Best Anonymous (No-Log) VPNs for 2024 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares NordVPN: Best for all-around security Mullvad VPN: Best for overall privacy ExpressVPN: Best for security audits ProtonVPN: Best against government...
Cryptominers Targeting Misconfigured Apache Hadoop and Flink with Rootkit in New Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 12, 2024NewsroomCryptocurrency / Malware Cybersecurity researchers have identified a new attack that exploits misconfigurations in Apache Hadoop and Flink to...
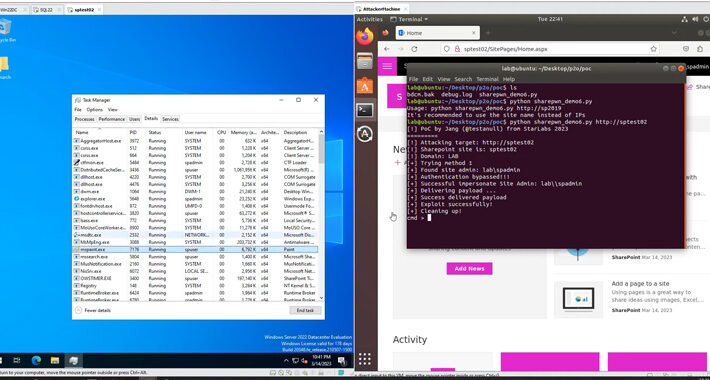
Act Now: CISA Flags Active Exploitation of Microsoft SharePoint Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 12, 2024NewsroomCyber Attack / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical security vulnerability impacting...
The art of Linux persistence
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Insights You Need from Harvard Business Review
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SUPPLY CHAINCYBER SECURITY.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Pharmacies Giving Patient Records to Police without Warrants – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Clive Robinson • January 11, 2024 8:58 AM @ ALL, Like the slow drip drip of the Chinese...
SMART CONTRACT SECURITY AUDIT
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
HUMANIZING AI
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Playbooks Version 2.0
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Application Security Testing (AST) Explained – Source: securityboulevard.com
Source: securityboulevard.com – Author: Julie Peterson The typical global enterprise has over 12,000 web-based applications, including APIs, SaaS applications, servers, and databases. While these applications play...
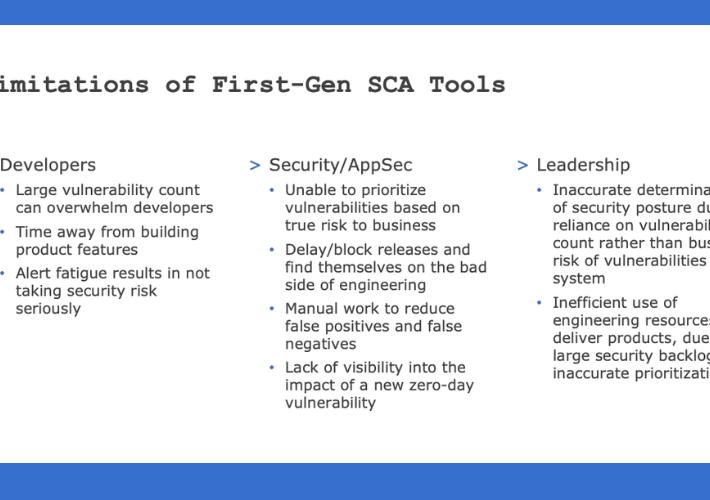
Prioritize Risk and Eliminate SCA Alert Fatigue with SCA 2.0 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dilan Krishnamurthy Countless data breaches are exposed daily, and finding the vulnerabilities that are leading to these breaches is extremely important. Businesses...
USENIX Security ’23 – Wenjun Zhu, Xiaoyu Ji, Yushi Cheng, Shibo Zhang, Wenyuan Xu ‘TPatch: A Triggered Physical Adversarial Patch’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Thursday, January 11, 2024 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Three ways to manage cybersecurity tool sprawl in your software supply chain – Source: securityboulevard.com
Source: securityboulevard.com – Author: William Penfield Sprawl happens Software development organizations evolve. Teams grow. The number of projects increases. Tech stacks change. Technology and management decisions...
Netskope Report Surfaces Raft of Cybersecurity Challenges – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard A report published by Netskope today revealed that, on average, 29 out of every 10,000 enterprise users clicked on a...
Cybercriminal Whistleblowers will Get Smarter – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joe Breen If you see something, say something and get paid by the SEC Under the SEC’s whistleblower program, “eligible whistleblowers are...
5 Ways MSPs Can Resolve a Hack – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kevin Smith If you are a managed service provider (MSP) handling small and medium-sized businesses (SMB) clients, there are some sobering stats...
Shopify DMARC Record Setup: Meet Google and Yahoo’s Sender Requirements – Source: securityboulevard.com
Source: securityboulevard.com – Author: EasyDmarc In response to evolving email authentication standards set by tech giants Google and Yahoo, third-party Email Service Providers (ESPs) like Shopify...
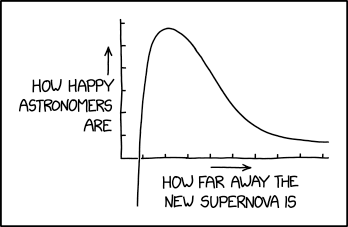
Randall Munroe’s XKCD ‘Supernova’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2024/01/randall-munroes-xkcd-supernova/ Category & Tags: Humor,Security Bloggers Network,Randall Munroe,Sarcasm,satire,XKCD...
Security firm Mandiant says it didn’t have 2FA enabled on its hacked Twitter account – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Anyone who works in computer security knows that they should have two-factor authentication (2FA) enabled on their accounts. 2FA provides...
Twitter says it’s not its fault the SEC’s account got hacked – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley The safety team at Twitter (I refuse to call the site X because that’s the completely daft kind of name...
Smashing Security podcast #354: Chuck Norris and the fake CEO, artificial KYC, and an Airbnb scam – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Chuck Norris gives a helping hand to a mysterious cryptocurrency CEO who may have separated investors from over a billion...
CISA adds Ivanti and Microsoft SharePoint bugs to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini CISA adds Ivanti and Microsoft SharePoint bugs to its Known Exploited Vulnerabilities catalog U.S. Cybersecurity and Infrastructure Security Agency (CISA)...
Two zero-day bugs in Ivanti Connect Secure actively exploited – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Two zero-day bugs in Ivanti Connect Secure actively exploited Ivanti revealed that two threat actors are exploiting two zero-day vulnerabilities...
X Account of leading cybersecurity firm Mandiant was hacked because not adequately protected – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini X Account of leading cybersecurity firm Mandiant was hacked because not adequately protected The X account of cybersecurity firm Mandiant...