Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Anucha Cheechang via Shutterstock Cybercriminals collectively leaked some 50 million records containing sensitive personal information in the...
Day: January 2, 2024
Google Settles Lawsuit Over Tracking ‘Incognito Mode’ Chrome Users – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Tim Walton via Alamy Stock Photo Google is settling a class-action lawsuit over how it tracks data...
Cyberattackers Target Nuclear Waste Company via LinkedIn – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff Source: Alekesey Zotov via Alamy Stock Photo Last week, a group of hackers targeted Radioactive Waste Management (RWM), a...
Israel Battles Spike in Wartime Hacktivist, OT Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Source: Birgit Korber via Alamy Stock Photo For Israel, 2023 will be remembered as the beginning...
CISO Planning for 2024 May Struggle When It Comes to AI – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joan Goodchild, Contributing Writer Source: Robert Hyrons via Alamy Stock Photo Just about every CISO knows how this scenario goes: Called in...
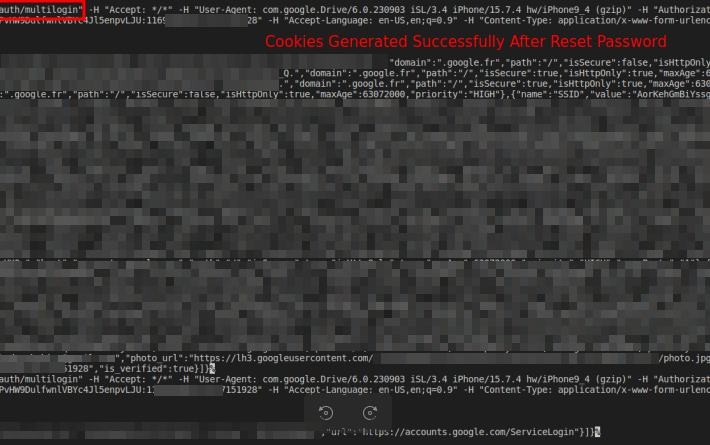
Attackers Abuse Google OAuth Endpoint to Hijack User Sessions – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: imageBROKER via Alamy Stock Photo Attackers have been exploiting an undocumented Google OAuth endpoint to hijack user...
Startups Scramble to Build Immediate AI Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Paul Shomo Source: Andrii Yalanskyi via Alamy Stock Photo COMMENTARY At the start of 2003, nobody knew the industry would be handed...
10 Years After Yahoo Breach, What’s Changed? (Not Much) – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: PhotoEdit via Alamy Stock Photo In September 2016, Yahoo copped to a breach of 500 million user...
Over $80m in Crypto Stolen in Cyber-Attack on Orbit Chain – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Over $80m worth of cryptocurrency has been stolen following a cyber-attack on cross-chain bridge project Orbit Chain. The blockchain revealed the...
Australian Court Service Hacked, Hearing Recordings at Risk – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Court cases and tribunals in Australia have been impacted by a cybersecurity incident, with attackers potentially accessing recordings of hearings, according...
Teen Found Alive After “Cyber-Kidnapping” Incident – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A Chinese foreign exchange student has been found alive and well by Utah police after being caught up in what authorities...
Black Basta Ransomware Decryptor Published – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have published a new suite of tools designed to help victims of the prolific Black Basta ransomware recover their...
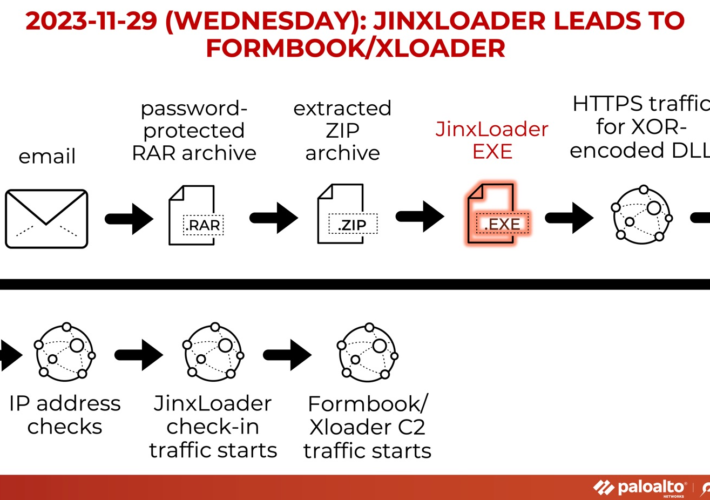
Experts warn of JinxLoader loader used to spread Formbook and XLoader – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn of JinxLoader loader used to spread Formbook and XLoader JinxLoader is a new Go-based loader that was spotted...
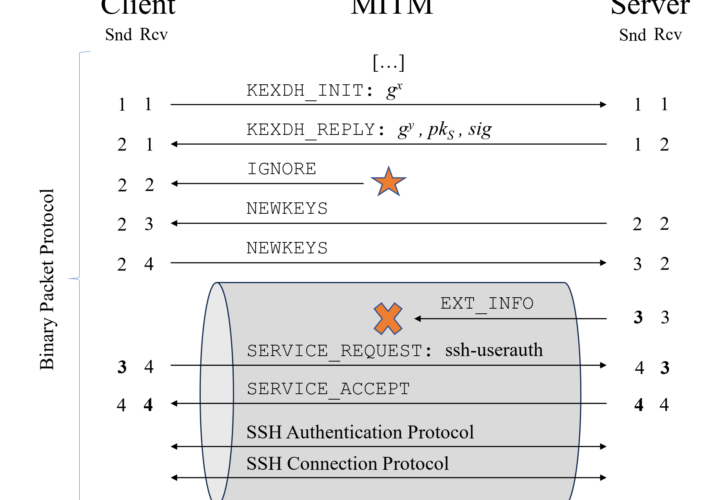
Terrapin attack allows to downgrade SSH protocol security – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Terrapin attack allows to downgrade SSH protocol security Researchers discovered an SSH vulnerability, called Terrapin, that could allow an attacker...
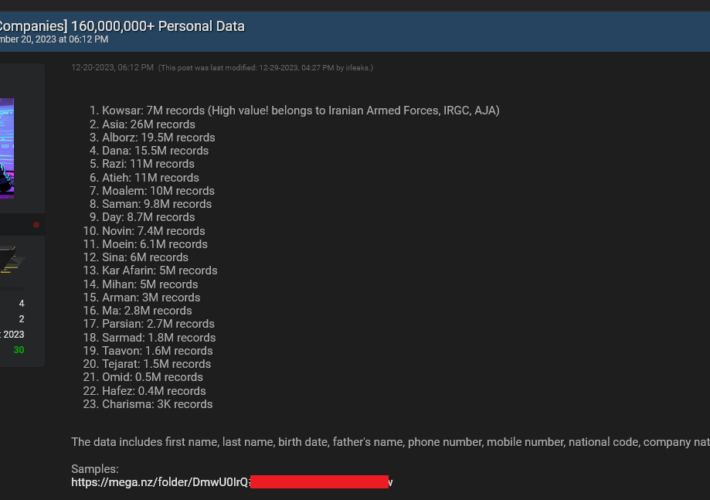
Multiple organizations in Iran were breached by a mysterious hacker – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Multiple organizations in Iran were breached by a mysterious hacker Hudson Researchers reported that a mysterious hacker launched a series...
Top 2023 Security Affairs cybersecurity stories – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Top 2023 Security Affairs cybersecurity stories These are the Top 2023 Security Affairs cybersecurity stories … enjoy it. CYBERCRIMINALS LAUNCHED...
Malware exploits undocumented Google OAuth endpoint to regenerate Google cookies – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Malware exploits undocumented Google OAuth endpoint to regenerate Google cookies CloudSEK researchers analyzed a zero-day exploit that can allow the...
The Definitive Enterprise Browser Buyer’s Guide – Source:thehackernews.com
Source: thehackernews.com – Author: . Security stakeholders have come to realize that the prominent role the browser has in the modern corporate environment requires a re-evaluation...
Google Settles $5 Billion Privacy Lawsuit Over Tracking Users in ‘Incognito Mode’ – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 02, 2024NewsroomData Privacy / Online Tracking Google has agreed to settle a lawsuit filed in June 2020 that alleged that...
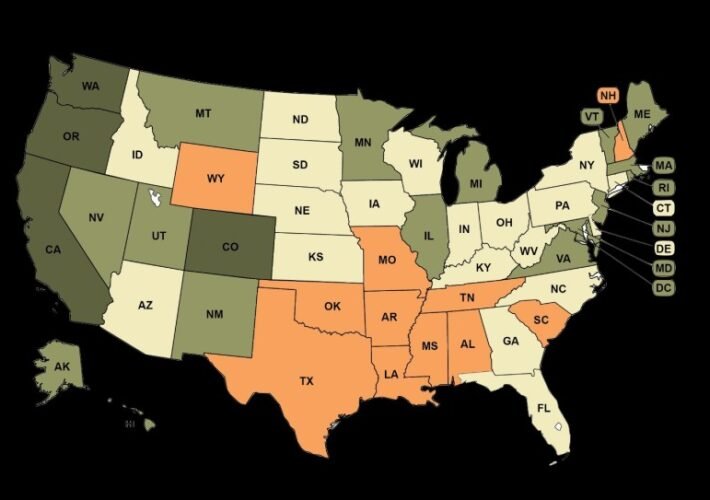
Welcome To 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: hrbrmstr Hey folks, This is likely our last shot at preserving liberal democracy in the U.S., or at least avoiding 20–40 years...
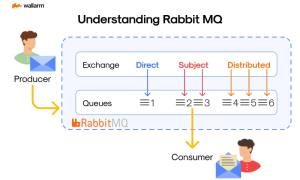
What is RabbitMQ? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ivan Novikov Grasping the Basics: What is RabbitMQ? Take a step into the realm of software development, where efficient and smooth interaction...
The Benefits of Employing AI in GRC – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michelle Ofir Geveye The narrative of technology surpassing human intelligence and altering the course of humanity is a recurring theme in science...
Insights from CISA HPH Sector Risk and Vulnerability Assessment – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rohan Timalsina In an ever-evolving digital landscape, the healthcare and public health (HPH) sector faces increasing cybersecurity challenges. The United States Cybersecurity...
8 Essential Steps to Recover a Hacked Website – Source: securityboulevard.com
Source: securityboulevard.com – Author: TuxCare Team When you find out your website is hacked, it’s understandable that you’d begin to panic. But it’s much better to...
Happy New Year 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
MS Excel Vulnerability Exploited To Distribute Agent Tesla – Source: securityboulevard.com
Source: securityboulevard.com – Author: Wajahat Raja Threat actors with malicious intent have now been exploiting an old MS Excel vulnerability as part of their phishing campaign....
The Three Keys to Success in Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tom Eston In this episode, host Tom Eston shares the three key lessons he’s learned over his 18-year career in cybersecurity: effective...
Cybersecurity Trends to Watch in 2024 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , AI-Based Attacks , API Security Expert Panelists Debate Impact of AI, Geopolitics and New Tactics in...