The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Year: 2023
Perspectives on Security for the Board by Cybersecurity Action Team – Google Cloud – April 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ULTIMATE DEVSECOPS LIBRARY – Tools, Resources & methodologies by sottlmarek
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Communicating the value of cybersecurity to boards and leadership – Seven strategies for life sciences and health care organizations.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Chief Information Security Officers – CISOs – Challenges & Priorities Survey Analysys Report by European Cyber Security Org (ECS)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity in the C-suite and Boardroom by Jon Oltsik – Enterprise Strategy Group (ESG)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Business Case for Security by CISA – Understand Your Security Posture
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Threat Hunting Playbooks for MITRE Tactics – Starting your first threat hunting today by PRASANNAKUMAR B MUNDAS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OSINT – The Most Complete Open Source Intelligence Overview by Joas Antonio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
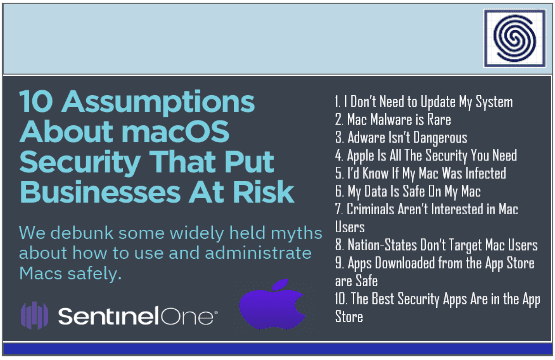
Be careful: 10 Assumptions About macOS Security that put Businesses At Risk by SentinelOne
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Zero Trust Matutity Model by CISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Hack the Cybersecurity Interview – A complete Interview Preparation Guide for jumpstarting your cybersecurity career by Ken Underhill – Christophe Fulon – Tia Hopkins – Packt
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Real Cyber War – The Political Economy of Internet Freedom by Shawn Powers & Michael Jablonski
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity for Dummies by Lawrence C. Miller
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
0-days Detected in-the-Wild in 2022 – Year in Review – Maddie Stone – Zer0Con 2023 – Google
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Classic Intrusion Analysis Frameworks for AWS Environments: Application and Enhancement by AWS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Practical Guide for CSIRTs by OAS – A Sustainable Business Model.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Executive Guide to Cyber Crisis Management 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NEW TO DFIR – FIELD MANUAL – The Ultimate Guide Getting Started in Forensics & Incident Response (DFIR) by SANS DFIR
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Boards Are Having the Wrong Conversations About Cybersecurity – Board interactions with the CISO are lacking – by Lucia Millica and Keri Pearlson – Harvard Business Review
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DevSecOps Guides – Comprehensive resource for integrating security into the software development by HADESS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Data Leakage for Dummies by Lawrence C. Miller
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
4 Steps to Building a Master Blue Team Home Lab by Logan Simpson
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DEFENCE-IN-DEPTH – Security Myths, Popular Pursuits, Reality & Concealed Vulnerabilities by The Security Institute Fellow
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Awareness for dummies series by Ira Winkler
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
So You Want To Be a Hacker – A story guide by Logan Simpson
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of the CISO – a global report on priorities , pain points, and security gaps 2023 by SALT
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Personal Cyber Security First Steps by Australian Government – ACSC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SANS Offensive Operations – ChatGPT for Offensive Security – What is ChatGPT and how can it be used in offensive security ?
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...