Source: www.bleepingcomputer.com – Author: Lawrence Abrams A new sextortion scam is making the rounds that pretends to be an email from the adult site YouPorn, warning...
Month: September 2023
Yes, there’s an npm package called @(-.-)/env and some others like it – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Strangely named npm packages like -, @!-!/-, @(-.-)/env, and –hepl continue to exist on the internet’s largest software registry. While not all of...
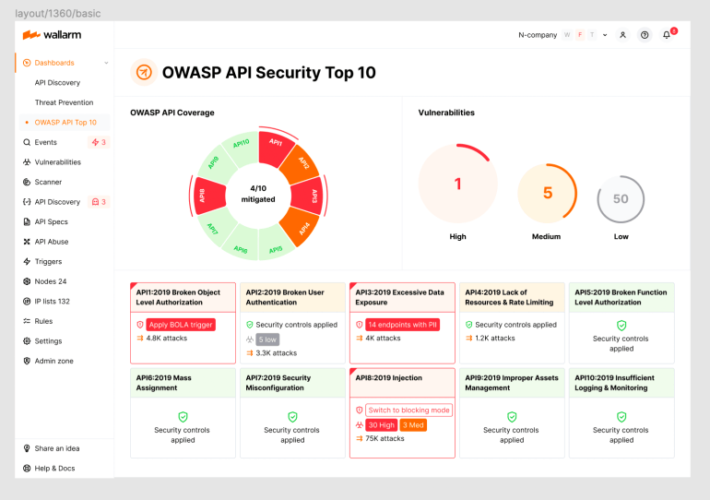
2023 OWASP Top-10 Series: API6:2023 Unrestricted Access to Sensitive Business Flows – Source: securityboulevard.com
Source: securityboulevard.com – Author: wlrmblog Welcome to the 7th post in our weekly series on the new 2023 OWASP API Security Top-10 list, with a particular...
MSP Vs MSSP is there a distinction anymore? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Amy Luby MSP v MSSP – is there a distinction anymore? Well, yes and no. Yes there’s a distinction because if you...
Happy United States Labor Day 2023 / Feliz Día del Trabajo de Estados Unidos 2023 / Bonne Fête du Travail aux États-Unis 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/happy-united-states-labor-day-2023-feliz-dia-del-trabajo-de-estados-unidos-2023-bonne-fete-du-travail-aux-etats-unis-2023/ Category & Tags: Security Bloggers Network,Día del...
Harnessing Generative AI for Building the Human Firewall Against AI-Driven Identity Scams – Source: securityboulevard.com
Source: securityboulevard.com – Author: Keon Ramzani In response to the growing concerns surrounding AI-driven threats, Constella is not only taking steps to understand and reproduce these...
Frontine VM Receives the Texas Risk and Authorization Management Program (TXRAMP) Certification – Source: securityboulevard.com
Source: securityboulevard.com – Author: Digital Defense by HelpSystems San Antonio, TX – August 1, 2023 – Fortra’s Digital Defense, leading provider of information security governance, risk...
Two brothers on a journey: Unleashing AI to defeat $200B chargeback problem – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Ariel and Avia Chen, Israeli-American entrepreneurs, have been on a remarkable journey that led them from their passion for technology –...
Autonomous vehicles pros and cons: A comprehensive analysis – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: While 70% of Americans are afraid of self-driving cars, it’s worth noting that a staggering 94% of all traffic...
Cyberattackers Swarm OpenFire Cloud Servers With Takeover Barrage – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading The Kinsing cybercrime group is back with a new attack vector: Pummeling a previously disclosed path traversal flaw...
A Brief History of ICS-Tailored Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Oleg Brodt, R&D Director of Deutsche Telekom Innovation Labs, Israel, and Chief Innovation Officer for Cyber@Ben-Gurion University It’s relatively hard for malware...
Adversaries Ride RocketMQ Bug to DreamBus Bot Resurgence – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Since the disclosure in May that RocketMQ servers had a remote code execution (RCE) bug, multiple threat...
Social engineering attacks target Okta customers to achieve a highly privileged role – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Social engineering attacks target Okta customers to achieve a highly privileged role Pierluigi Paganini September 02, 2023 Identity services provider...
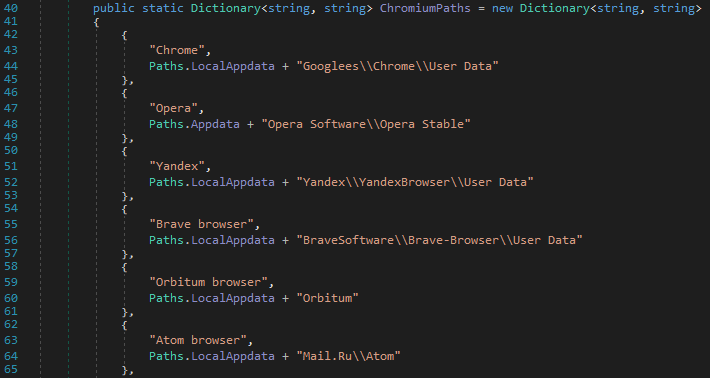
Talos wars of customizations of the open-source info stealer SapphireStealer – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Talos wars of customizations of the open-source info stealer SapphireStealer Pierluigi Paganini September 01, 2023 Cisco reported that multiple threat...
UK Cyber Agency Warns of Prompt Injection Attacks in AI – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Hackers Can Deploy Prompt Injection Attacks to Gain Access to...
Threat Modeling Essentials for Generative AI in Healthcare – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 It’s critical for healthcare sector entities that are considering – or are already – deploying generative AI applications to create an...
Tech Companies on Precipice of UK Online Safety Bill – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Geo Focus: The United Kingdom , Geo-Specific , Legislation & Litigation Bill ‘Poses a serious threat’ to end-to-end encryption, Apple Says...
‘Earth Estries’ APT Hackers Are Cyberespionage Pros – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Trend Micro Calls the Group Well-Resourced and Sophisticated Prajeet Nair (@prajeetspeaks) • September 1, 2023 Image: Shutterstock A cyberespionage...
ISMG Editors: Identity Security Special – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Digital Identity , Video Identity Security Expert Jeremy Grant on AI and Digital Identity Risks Anna Delaney (annamadeline) • September 1,...
Exploit Code Published for Critical-Severity VMware Security Defect – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Just days after shipping a major security update to correct vulnerabilities in its Aria Operations for Networks product line, VMWare...
Why is .US Being Used to Phish So Many of Us? – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Domain names ending in “.US” — the top-level domain for the United States — are among the most prevalent in phishing...
Okta Warns of Social Engineering Attacks Targeting Super Administrator Privileges – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 02, 2023THNCyber Attack / Social Engineering Identity services provider Okta on Friday warned of social engineering attacks orchestrated by threat...
Microsoft is killing WordPad in Windows after 28 years – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft announced today that it will deprecate WordPad with a future Windows update as it’s no longer under active development,...
Exploit released for critical VMware SSH auth bypass vulnerability – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Proof-of-concept exploit code has been released for a critical SSH authentication bypass vulnerability in VMware’s Aria Operations for Networks analysis...
Microsoft reminds of Windows 11 21H2 forced updates before end of service – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has reminded customers that systems running Windows 11 21H2 will be force-updated before the end of servicing next month....
Microsoft retires Visual Studio for Mac, support ends in a year – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Microsoft has announced it is retiring Visual Studio for Mac and that support for the latest version, 17.6, will continue for another...
Lazarus hackers deploy fake VMware PyPI packages in VMConnect attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas North Korean state-sponsored hackers have uploaded malicious packages to the PyPI (Python Package Index) repository, camouflaging one of them as...
Fake Signal and Telegram apps – Week in security with Tony Anscombe – Source:
Source: – Author: 1 ESET research uncovers active campaigns targeting Android users and spreading espionage code through the Google Play store, Samsung Galaxy Store and dedicated...
What you need to know about iCloud Private Relay – Source:
Source: – Author: 1 If you want to try to enter the world of VPNs with a small dip, then iCloud Private Relay is your friend...
BadBazaar espionage tool targets Android users via trojanized Signal and Telegram apps – Source:
Source: – Author: 1 ESET researchers have discovered active campaigns linked to the China-aligned APT group known as GREF, distributing espionage code that has previously targeted...