Source: www.infosecurity-magazine.com – Author: 1 Investigations have begun into a massive ransomware attack that has affected Sri Lanka’s government cloud system, Lanka Government Cloud (LGC). The...
Month: September 2023
IT Systems Encrypted After UK School Hit By Ransomware – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A spate of cyber-attacks against UK schools has claimed its latest victim after a Maidstone secondary school suffered a serious security...
AP Stylebook Breach May Have Hit Hundreds of Journalists – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Associated Press (AP) has warned that users of a popular writing style guide have been hit by phishing attacks after...
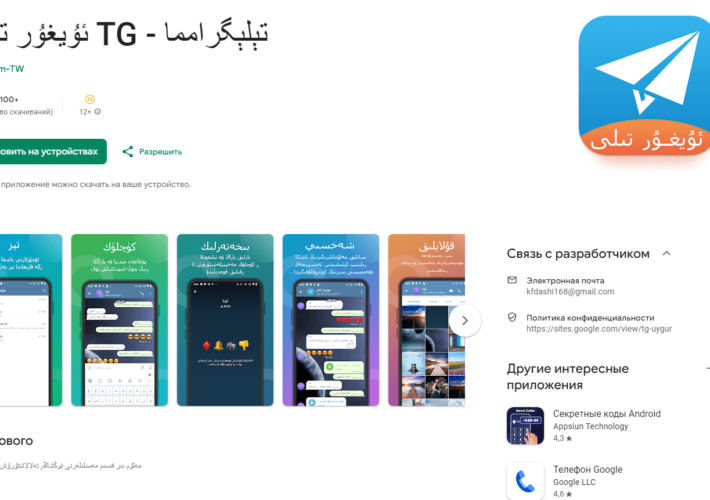
Evil Telegram Mods Removed From Google Play – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have revealed a number of lookalike Telegram apps on the official Play store which were modified to contain spyware....
GOOGLE FIXED THE FOURTH CHROME ZERO-DAY OF 2023 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini GOOGLE FIXED THE FOURTH CHROME ZERO-DAY OF 2023 Pierluigi Paganini September 11, 2023 Google rolled out emergency security updates to...
CISA adds recently discovered Apple zero-days to Known Exploited Vulnerabilities Catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini CISA adds recently discovered Apple zero-days to Known Exploited Vulnerabilities Catalog Pierluigi Paganini September 11, 2023 U.S. CISA adds vulnerabilities...
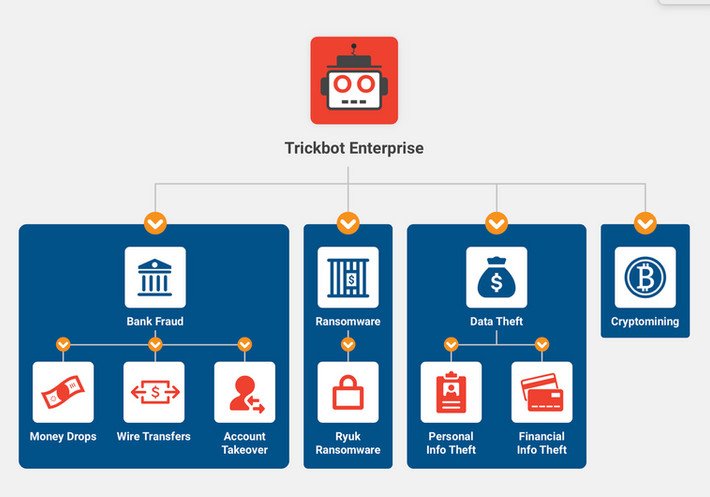
UK and US sanctioned 11 members of the Russia-based TrickBot gang – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini UK and US sanctioned 11 members of the Russia-based TrickBot gang Pierluigi Paganini September 11, 2023 The U.K. and U.S....
New HijackLoader malware is rapidly growing in popularity in the cybercrime community – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini New HijackLoader malware is rapidly growing in popularity in the cybercrime community Pierluigi Paganini September 11, 2023 Zscaler ThreatLabz detailed...
Some of TOP universities wouldn’t pass cybersecurity exam: left websites vulnerable – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Some of TOP universities wouldn’t pass cybersecurity exam: left websites vulnerable Pierluigi Paganini September 11, 2023 CyberNews researchers discovered that...
Evil Telegram campaign: Trojanized Telegram apps found on Google Play – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Evil Telegram campaign: Trojanized Telegram apps found on Google Play Pierluigi Paganini September 11, 2023 Evil Telegram: a Trojanized version...
Building Compliance from Scratch with a Culture of Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Natalie Anderson For managed service providers (MSPs), building a compliance program from the ground up for an organization is a welcome challenge....
Why Cyber Risk Quantification Needs a Trust Makeover? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anuj Magazine With this blog, we begin the series dedicated to exploring the nuances of cyber risk quantification. In the fast-evolving world...
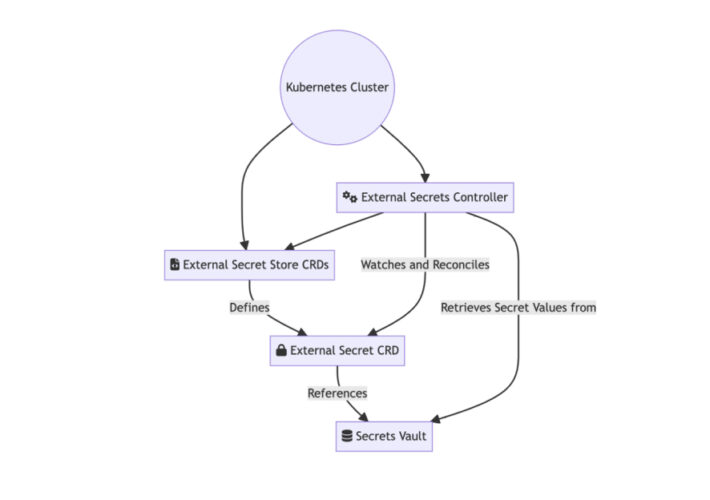
Best Practices of Secrets Management with Kubernetes – Source: securityboulevard.com
Source: securityboulevard.com – Author: Itzik Alvas. Co-founder & CEO, Entro Unlock the potential of your Kubernetes deployments by mastering the best practices for managing secrets, as...
Do you really need to tell FedEx your Social Security number? How to avoid package-delivery scams – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avast Blog Do you order cartons of strawberries, flat-screen TVs, running shoes, and light bulbs online? You’re far from alone. Oberlo reported...
Designed to Be Breached – Automated Document Consumption – Source: securityboulevard.com
Source: securityboulevard.com – Author: Votiro Team By David Neuman, Senior Analyst, TAG Cyber The use of automated document consumption and data extraction processes presents the opportunity...
Insights from Attack and Defense Drills: Strategies and Resilience – Source: securityboulevard.com
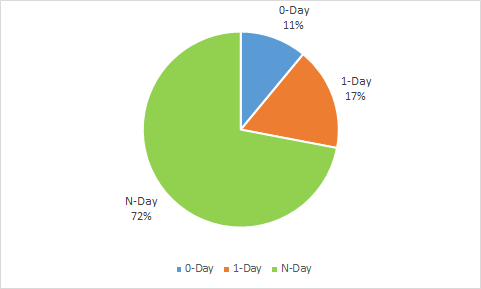
Source: securityboulevard.com – Author: NSFOCUS Recently, NSFOCUS SOC team summarized the findings from attack and defense drills in the first half of 2023. In these smokeless...
Ekran System to Exhibit at it-sa Expo&Congress 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: yana.storchak@apriorit.com Ekran System will participate in the upcoming it-sa Expo&Congress 2023 in Nuremberg, Germany. The event takes place October 10–12, 2023, at...
A Comprehensive Guide to User Access Review: Best Practices and Pitfalls – Source: securityboulevard.com
Source: securityboulevard.com – Author: Wesley Van Zyl, Senior Compliance Success Manager, Scytale We say it all the time; your employees are your first line of defense;...
Data Breach of AP Stylebook Leads to Phishing Attacks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Users of the AP Stylebook have been targeted in phishing campaigns by bad actors using personal information stolen in a...
Ransomware: It Takes A Village, Says NCSC – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware UK Crime and Cybersecurity Agencies Urge ‘Holistic’ View of Ransomware Ecosystem Akshaya Asokan (asokan_akshaya) •...
Root Admin User: When Do Common Usernames Pose a Threat? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Access Management Honeypot Hits Reinforce Need for Strong Passwords and Multifactor Authentication Mathew J. Schwartz (euroinfosec) • September 11, 2023 ...
Judge Gives Green Light to Meta Pixel Web Tracker Lawsuit – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Healthcare Judge Dismisses Some Plaintiff Claims But Allows Proposed Class Action...
DarkGate Malware Operators on a Phishing Spree – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Social Engineering Vectors Includes Teams Phishing and Malvertising Mihir Bagwe (MihirBagwe) • September 11, 2023 ...
Navigating PAM Implementation Risks: A Comprehensive Guide for CISOs – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Mihaela Popa Chief Information Security Officers (CISOs) bear the responsibility of safeguarding their organizations against an ever-evolving array of cyber threats. Among...
What Is Token-Based Authentication? – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Antonia Din Secured authentication to databases and systems is essential to enterprise cybersecurity management. According to the 2023 Data Breach Investigations Report,...
OneTrust Data Governance Review (2023): Features & Pricing – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Ray Fernandez OneTrust: Fast facts Pricing: OneTrust does not offer transparent pricing details on its website. Those interested can test its 14-day...
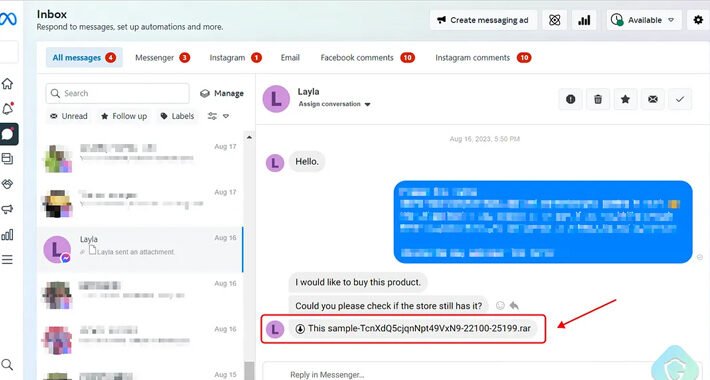
Vietnamese Hackers Deploy Python-Based Stealer via Facebook Messenger – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 11, 2023THNMalware / Social Media A new phishing attack is leveraging Facebook Messenger to propagate messages with malicious attachments from...
Charming Kitten’s New Backdoor ‘Sponsor’ Targets Brazil, Israel, and U.A.E. – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 11, 2023THNCyber Espionage / Malware The Iranian threat actor known as Charming Kitten has been linked to a new wave...
How to Prevent API Breaches: A Guide to Robust Security – Source:thehackernews.com
Source: thehackernews.com – Author: . With the growing reliance on web applications and digital platforms, the use of application programming interfaces (APIs) has become increasingly popular....