Source: www.darkreading.com – Author: 1 Security is a top priority for all customers on Google Cloud, whether beginner, intermediate, or advanced users. Through our partnership with...
Month: September 2023
Cloudflare Announces Unified Data Protection Suite to Address Risks of Modern Coding and Increased AI Use – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 San Francisco, CA, September 7, 2023 – Cloudflare, Inc. (NYSE: NET), the security, performance, and reliability company helping to build a better Internet, today...
Iran’s Charming Kitten Pounces on Israeli Exchange Servers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading In the last two years, an Iranian state-backed threat actor has breached 32 Israeli organizations running...
Being Flexible Can Improve Your Security Posture – Source: www.darkreading.com
Source: www.darkreading.com – Author: Joshua Goldfarb, Security and Fraud Architect, F5 Recently, I was working on a specific task. About an hour into the task, I...
‘Steal-It’ Campaign Uses OnlyFans Models as Lures – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A sophisticated cyber campaign is using images of OnlyFans models and geofencing to target specific victims across...
Cars Have Terrible Data Privacy – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Cars Have Terrible Data Privacy A new Mozilla Foundation report concludes that cars, all of them, have terrible data...
On Robots Killing People – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier The robot revolution began long ago, and so did the killing. One day in 1979, a robot at a Ford...
7 Steps to Kickstart Your SaaS Security Program – Source:thehackernews.com
Source: thehackernews.com – Author: . SaaS applications are the backbone of modern businesses, constituting a staggering 70% of total software usage. Applications like Box, Google Workplace,...
Chinese Redfly Group Compromised a Nation’s Critical Grid in 6-Month ShadowPad Campaign – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 12, 2023THNCritical Infrastructure Security A threat actor called Redfly has been linked to a compromise of a national grid located...
Sophisticated Phishing Campaign Deploying Agent Tesla, OriginBotnet, and RedLine Clipper – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 12, 2023THNEndpoint Security / Malware A sophisticated phishing campaign is using a Microsoft Word document lure to distribute a trifecta...
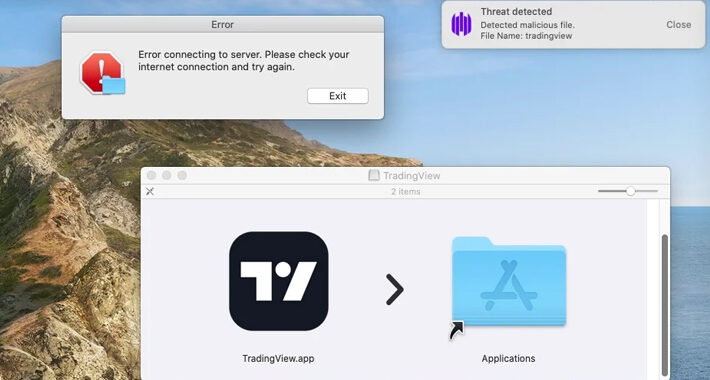
Beware: MetaStealer Malware Targets Apple macOS in Recent Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 12, 2023THNEndpoint Security / Data Security A new information stealer malware called MetaStealer has set its sights on Apple macOS,...
Google Rushes to Patch Critical Chrome Vulnerability Exploited in the Wild – Update Now – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 12, 2023THNBrowser Security / Zero Day Google on Monday rolled out out-of-band security patches to address a critical security flaw...
Ransomware: It Takes A Village, Says NCSC – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Ransomware UK Crime and Cybersecurity Agencies Urge ‘Holistic’ View of Ransomware Ecosystem Akshaya Asokan (asokan_akshaya) •...
Root Admin User: When Do Common Usernames Pose a Threat? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Access Management Honeypot Hits Reinforce Need for Strong Passwords and Multifactor Authentication Mathew J. Schwartz (euroinfosec) • September 11, 2023 ...
Judge Gives Green Light to Meta Pixel Web Tracker Lawsuit – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Healthcare Judge Dismisses Some Plaintiff Claims But Allows Proposed Class Action...
DarkGate Malware Operators on a Phishing Spree – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Social Engineering Vectors Includes Teams Phishing and Malvertising Mihir Bagwe (MihirBagwe) • September 11, 2023 ...
MGM Resorts Confirms ‘Cybersecurity Issue’, Shuts Down Systems – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Hospitality and entertainment giant MGM Resorts on Monday said a “cybersecurity issue” forced the shutdown of certain computer systems, including...
US Marks 22 Years Since 9/11 Terrorist Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News On Monday, Americans commemorated the 22nd anniversary of the 9/11 attacks through solemn silences, emotional reflections, and calls to educate...
After Microsoft and X, Hackers Launch DDoS Attack on Telegram – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The hacker group Anonymous Sudan has launched a distributed denial-of-service (DDoS) attack against Telegram in retaliation to the messaging platform’s...
Bookstore Chain Dymocks Discloses Data Breach Possibly Impacting 800k Customers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Bookstore chain Dymocks Booksellers is informing hundreds of thousands of individuals that their personal information might have been stolen in...
Associated Press Stylebook Users Targeted in Phishing Attack Following Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The Associated Press is informing some AP Stylebook customers that their information has been compromised as a result of a...
FBI Blames North Korean Hackers for $41 Million Stake.com Heist – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The FBI says that the North Korea-linked hacking group Lazarus is responsible for the theft of $41 million in cryptocurrency...
Spies, Hackers, Informants: How China Snoops on the West – Source: www.securityweek.com
Source: www.securityweek.com – Author: AFP British authorities have arrested a man who reportedly spied for China at the heart of the government in London, sparking fresh fears over...
A 10-point checklist: Owning your cloud security assessment – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Nearly 90% of businesses have taken a multi-cloud approach, and 97% of IT leaders intend to expand cloud systems....
Vulnerabilities Allow Hackers to Hijack, Disrupt Socomec UPS Devices – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Some uninterruptible power supply (UPS) products made by Socomec are affected by several vulnerabilities that can be exploited to hijack...
News Alert: Traceable AI report exposes true scale of API-related data breaches, top challenges – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido San Francisco, Calif. —Traceable AI, the industry’s leading API security company, today released its comprehensive research report – the 2023 State of API...
Cuba Ransomware Group Unleashes Undetectable Malware – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers at Kaspersky have unveiled research into the activities of the notorious ransomware group known as Cuba. According to a...
Lazarus Group Targets macOS in Supply Chain Assault – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity firm ESET has detected a significant supply chain attack targeting macOS devices. The Lazarus Group, known for its advanced cyber...
Pentagon Urges Collaboration in Cyber Defense – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 In a discussion at the FedTalks event in Washington last Thursday, Leslie A. Beavers, principal deputy chief information officer at the...
Board Members Struggling to Understand Cyber Risks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Board members frequently struggle to understand cyber risks, putting businesses at higher risk of attacks, a new report from cybersecurity consultancy...