Source: www.securityweek.com – Author: Eduard Kovacs Dutch infrastructure-as-a-service and cloud solutions provider Leaseweb shut down some critical systems last week due to a cyberattack. The company...
Day: August 28, 2023
Ohio History Organization Says Personal Information Stolen in Ransomware Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Ohio History Connection (OHC) has confirmed that personal information of thousands of individuals was stolen in a July ransomware attack...
3 Cryptocurrency Firms Suffer Data Breach After Kroll SIM Swapping Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Three bankrupt cryptocurrency companies — FTX, BlockFi and Genesis — have suffered data breaches following a SIM swapping attack that...
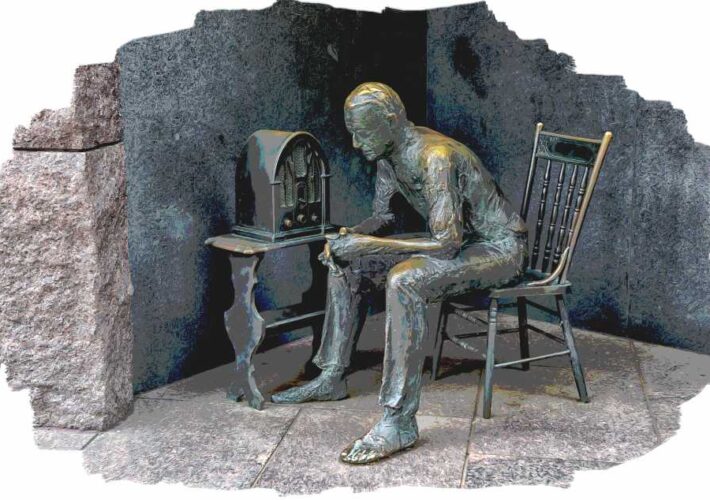
Remotely Stopping Polish Trains – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Turns out that it’s easy to broadcast radio commands that force Polish trains to stop: …the saboteurs appear to have...
Exploit released for Juniper firewall bugs allowing RCE attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Proof-of-concept exploit code has been publicly released for vulnerabilities in Juniper SRX firewalls that, when chained, can allow unauthenticated attackers...
Mom’s Meals discloses data breach impacting 1.2 million people – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas PurFoods, which conducts business in the U.S. as ‘Mom’s Meals,’ is warning of a data breach after the personal information...
Four common password mistakes hackers love to exploit – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sponsored by Specops Software Our brains are incredibly good at pattern completion – it’s why we see animals in the clouds and...
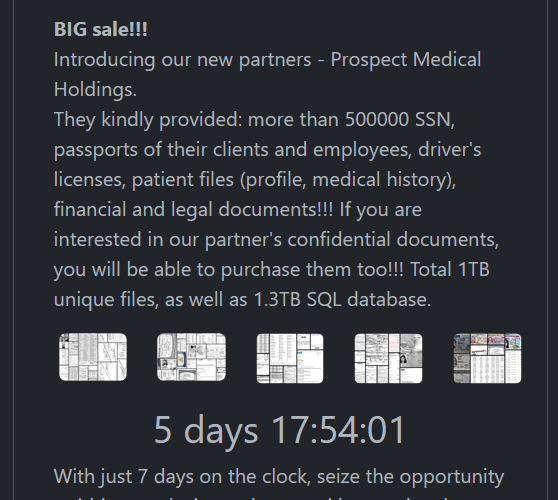
Rhysida claims ransomware attack on Prospect Medical, threatens to sell data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The Rhysida ransomware gang has claimed responsibility for the massive cyberattack on Prospect Medical Holdings, claiming to have stolen 500,000...
Microsoft wants you to learn more about new features in Windows 11 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Microsoft is experimenting with different approaches to introduce new users to Windows 11’s features as soon as they complete the...
ICO calls on social media firms to protect user’s data from scraping – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas UK’s Information Commissioner’s Office (ICO), together with eleven data protection and privacy authorities from around the world, have published a...
Black Hat Fireside Chat: How to achieve API security — as AI-boosted attacks intensify – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido API security has arisen as a cornerstone of securing massively interconnected cloud applications. At Black Hat USA...
Rhysida ransomware group claims the hack of Prospect Medical – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Rhysida ransomware group claims the hack of Prospect Medical The Rhysida ransomware group claimed to have hacked Prospect Medical Holdings...
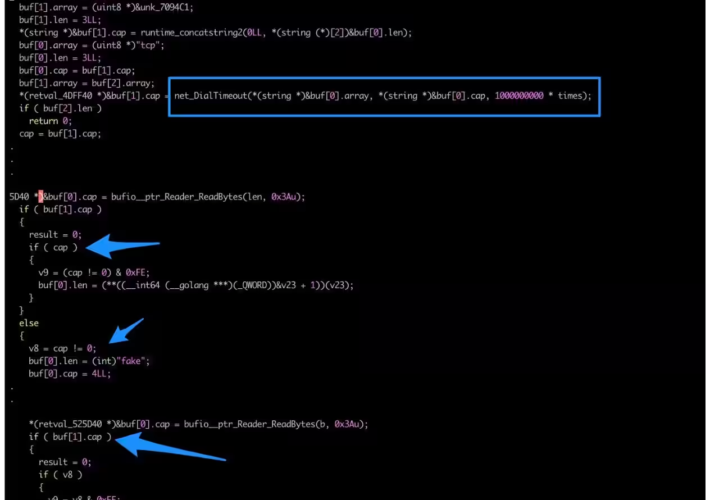
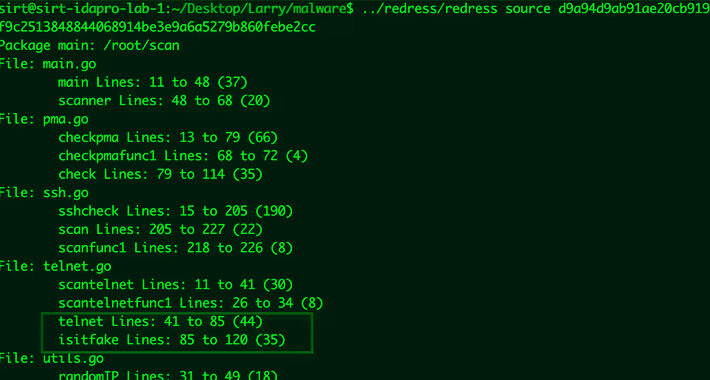
Updated Kmsdx botnet targets IoT devices – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Updated Kmsdx botnet targets IoT devices Researchers spotted an updated version of the KmsdBot botnet that is now targeting Internet of...
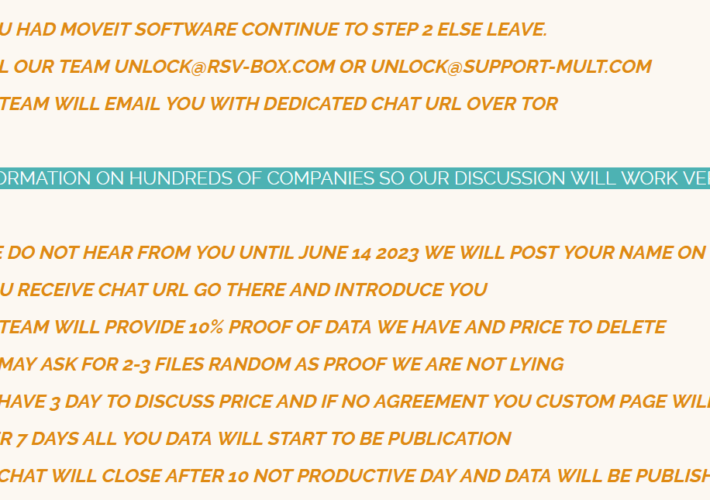
Massive MOVEit campaign already impacted at least 1,000 organizations and 60 million individuals – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Massive MOVEit campaign already impacted at least 1,000 organizations and 60 million individuals The recent wave of MOVEit attacks conducted by the...
Poland’s authorities investigate a hacking attack on country’s railways – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Poland’s authorities investigate a hacking attack on country’s railways The Polish domestic security agency is investigating a hacking attack on...
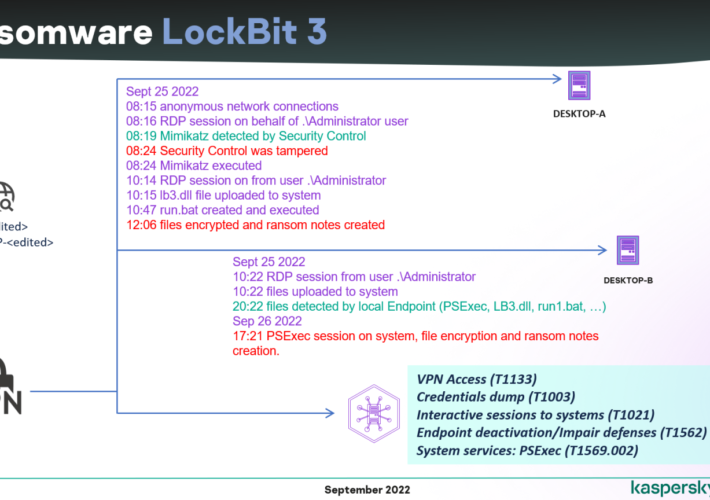
Leaked LockBit 3.0 ransomware builder used by multiple threat actors – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Leaked LockBit 3.0 ransomware builder used by multiple threat actors The leak of the source code of the LockBit 3.0 ransomware builder...
Security Affairs newsletter Round 434 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
Malware Unleashed: Public Sector Hit in Sudden Surge, Reveals New Research – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Report unmasks recent cybersecurity challenges for governments, healthcare, financial services, and vital infrastructure. Ismael Valenzuela, Vice President of Threat Research &...
KmsdBot Malware Gets an Upgrade: Now Targets IoT Devices with Enhanced Capabilities – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 28, 2023THNInternet of Things / Malware An updated version of a botnet malware called KmsdBot is now targeting Internet of...
Cloud Repatriation: The Unforeseen Reversal in Cloud Computing Trends – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rajan Sodhi As cloud computing continues to evolve, an intriguing new trend is emerging – cloud repatriation. This concept, also known as...
BSides Cheltenham 2023 – Simon Gurney – Making Your Own Cool Conference Badges! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Yes, we have specific objectives for uptime and recovery Yes, we talk about resilience, but don’t have specific objectives It’s...
What’s New in the NIST Cybersecurity Framework 2.0 Draft? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity NIST has released a draft version 2.0 of the Cybersecurity Framework. Here’s what you need to know and how...
SmokeLoader Trojan Deploys Location-Tracking Malware – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Customer Identity & Access Management (CIAM) , Cybercrime , Fraud Management & Cybercrime ‘Whiffy Recon’ Uses WiFi Access Points, Google API...