Source: – Author: 1 How content creators and subscribers can embrace the social media platform without (overly) exposing themselves to the potentially toxic brew of NSFW...
Month: July 2023
Pig butchering scams: The anatomy of a fast-growing threat – Source:
Source: – Author: 1 How fraudsters groom their marks and move in for the kill using tricks from the playbooks of romance and investment scammers Original...
ESET Research Podcast: A year of fighting rockets, soldiers, and wipers in Ukraine – Source:
Source: – Author: 1 ESET experts share their insights on the cyber-elements of the first year of the war in Ukraine and how a growing number...
World Backup Day: Avoiding a data disaster is a forever topic – Source:
Source: – Author: 1 By failing to prepare you are preparing to fail. Make sure you’re able to bounce back if, or when, a data disaster...
Spring into action and tidy up your digital life like a pro – Source:
Source: – Author: 1 Spring is in the air and as the leaves start growing again, why not breathe some new life into the devices you...
Not-so-private messaging: Trojanized WhatsApp and Telegram apps go after cryptocurrency wallets – Source:
Source: – Author: 1 ESET researchers analyzed Android and Windows clippers that can tamper with instant messages and use OCR to steal cryptocurrency funds Original Post...
Why you should spring clean your home network and audit your backups – Source:
Source: – Author: 1 Do you know how many devices are connected to your home network? You don’t? This is precisely why it’s time for a...
Cleaning up your social media and passwords: What to trash and what to treasure – Source:
Source: – Author: 1 Give your social media presence a good spring scrubbing, audit your passwords and other easy ways to bring order to your digital...
Multiple DDoS botnets were observed targeting Zyxel devices – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers warn of several DDoS botnets exploiting a critical flaw tracked as CVE-2023-28771 in Zyxel devices. Fortinet FortiGuard Labs researchers...
Couple Charged in Laundering Bitfinex Heist to Plead Guilty – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cryptocurrency Fraud , Finance & Banking , Fraud Management & Cybercrime Russian Entrepreneur, Would-Be Rapper to Seal Plea Deal in NY...
Windows 11 23H2 to give you greater control over power consumption – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Microsoft is making it easier to see how much energy your apps use in Windows 11 over a given period...
Over 15K Citrix servers likely vulnerable to CVE-2023-3519 attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Thousands of Citrix Netscaler ADC and Gateway servers exposed online are likely vulnerable against a critical remote code execution (RCE)...
Stolen Microsoft key offered widespread access to Microsoft cloud services – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The Microsoft consumer signing key stolen by Storm-0558 Chinese hackers provided them with access far beyond the Exchange Online and...
BSides Sofia 2023 – Victor Bonev – Secure Distroless OCI Images Via YAML – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Review: Can We Trust the Waterfox Browser? (Updated 2023) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avoid The Hack! Waterfox came into the browser scene in 2011, coming right out the box with official x64 support (a rarity...
2023 OWASP Top-10 Series: Introduction – Source: securityboulevard.com
Source: securityboulevard.com – Author: wlrmblog In early June 2023, OWASP released the final version of the OWASP API Security Top-10 list update. At that time we...
Few Fortune 100 Firms List Security Pros in Their Executive Ranks – Source: securityboulevard.com
Source: securityboulevard.com – Author: BrianKrebs Many things have changed since 2018, such as the names of the companies in the Fortune 100 list. But one aspect...
How to use Repository Health Check 2.0 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Sonatype Hot Topics GitHub Developers Targeted by North Korea’s Lazarus Group Few Fortune 100 Firms List Security Pros in Their Executive Ranks...
Couple Charged in Laundering Bitfinex Heist to Plead Guilty – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cryptocurrency Fraud , Finance & Banking , Fraud Management & Cybercrime Russian Entrepreneur, Would-Be Rapper to Seal Plea Deal in NY...
Google Categorizes 6 Real-World AI Attacks to Prepare for Now – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Google researchers have identified six specific attacks that can occur against real-world AI systems, finding that these common attack vectors...
Hacker-Turned-Security-Researcher Kevin Mitnick Dies Aged 59 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Noted hacker and security researcher Kevin Mitnick has died at the age of 59, following a 14-month...
HyperSense Fraud Management Now Available on Google Cloud – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 BENGALURU, India, July 18, 2023 /PRNewswire/ — Subex, a trusted leader in fraud management for nearly three decades, announces the general availability of its Fraud Management solution on...
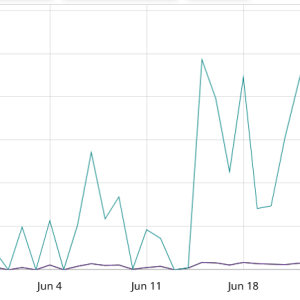
Study: Africa Cybersecurity Improves but Lacks Cross-Border Frameworks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading While cybersecurity expenditures in Africa are projected to grow to $3.7 billion by 2025 (up nearly...
SophosEncrypt Ransomware Fools Security Researchers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The SophosEncrypt ransomware-as-a-service (RaaS) threat has emerged, after flying under the radar by impersonating cybersecurity vendor Sophos. The...
5 Major Takeaways From Microsoft’s July Patch Tuesday – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Keep up with the latest cybersecurity threats, newly-discovered vulnerabilities, data breach information, and emerging trends....
AWS Cloud Credential Stealing Campaign Spreads to Azure, Google Cloud – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A sophisticated cloud-credential stealing and cryptomining campaign targeting Amazon Web Services (AWS) environments for the past...
UAE and South African Hospitals Fail on DMARC Implementation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Around three-quarters of hospitals in the United Arab Emirates and South Africa have not adopted the...
If George Washington Had a TikTok, What Would His Password Be? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Gil Cohen, Head of Application Security and Secure-SDLC, CYE Have you ever thought of what George Washington’s hypothetical TikTok password might be?...
Insider Risk Management Starts With SaaS Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Insider risk management (IRM) plays an important role in cybersecurity. It addresses potential threats posed by individuals within an organization who...
Scammers are targeting college kids with fake bioscience job offers – Source: www.proofpoint.com
Source: www.proofpoint.com – Author: 1 Cybercriminals are targeting college students with fake job offers in the bioscience and health industries with the hope of extracting fees...