Goodbye “Kill Chains”, Hello “Attack Sequences”A few years ago at the RSA Conference I co-presented on the top cloud attack “kill chains”. Shawn Harris @infotechwarrior and...
Year: 2022
Cybercriminals Developing BugDrop Malware to Bypass Android Security Features
Cybercriminals Developing BugDrop Malware to Bypass Android Security FeaturesIn a sign that malicious actors continue to find ways to work around Google Play Store security protections,...
Hackers Using Bumblebee Loader to Compromise Active Directory Services
Hackers Using Bumblebee Loader to Compromise Active Directory ServicesThe malware loader known as Bumblebee is being increasingly co-opted by threat actors associated with BazarLoader, TrickBot, and...
Chrome browser gets 11 security fixes with 1 zero-day – update now!
Chrome browser gets 11 security fixes with 1 zero-day – update now!Don't delay - patch today.Leer másNaked SecurityDon't delay - patch today.
Researchers Detail Evasive DarkTortilla Crypter Used to Deliver Malware
Researchers Detail Evasive DarkTortilla Crypter Used to Deliver MalwareA .NET-based evasive crypter named DarkTortilla has been used by threat actors to distribute a broad array of commodity malware...
US offers reward “up to $10 million” for information about the Conti gang
US offers reward “up to $10 million” for information about the Conti gangWanted - Reward Offered - Five unknown individuals (plus a man with a weird...
China-backed APT41 Hackers Targeted 13 Organisations Worldwide Last Year
China-backed APT41 Hackers Targeted 13 Organisations Worldwide Last YearThe Chinese advanced persistent threat (APT) actor tracked as Winnti has targeted at least 13 organizations geographically spanning...
Cybercrime Group TA558 Targeting Hospitality, Hotel, and Travel Organizations
Cybercrime Group TA558 Targeting Hospitality, Hotel, and Travel OrganizationsA financially motivated cybercrime group has been linked to an ongoing wave of attacks aimed at hospitality, hotel,...
Apple patches double zero-day in browser and kernel – update now!
Apple patches double zero-day in browser and kernel – update now!Double 0-day exploits - one in WebKit (to break in) and the other in the kernel...
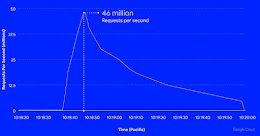
Google Cloud Blocks Record DDoS attack of 46 Million Requests Per Second
Google Cloud Blocks Record DDoS attack of 46 Million Requests Per SecondGoogle's cloud division on Thursday disclosed it mitigated a series of HTTPS distributed denial-of-service (DDoS)...
S3 Ep96: Zoom 0-day, AEPIC leak, Conti reward, healthcare security [Audio + Text]
S3 Ep96: Zoom 0-day, AEPIC leak, Conti reward, healthcare security [Audio + Text]Latest episode - listen now (or read if you prefer!)Leer másNaked SecurityLatest episode -...
DoNot Team Hackers Updated its Malware Toolkit with Improved Capabilities
DoNot Team Hackers Updated its Malware Toolkit with Improved CapabilitiesThe Donot Team threat actor has updated its Jaca Windows malware toolkit with improved capabilities, including a...
FORTINET Global Threat Landscape Report 2022 – A Semiannual Report by FortiGuard Labs
Another half-year through unprecedented times has passed. But as unique as these times may feel, we continue to see familiar exploits, names, and attacks taking up...
#DEFCON: Electrovolt Exploits Against Electron Desktop Apps Exposed
#DEFCON: Electrovolt Exploits Against Electron Desktop Apps ExposedElectron-based desktop application including Discord, Microsoft Teams and VScode were at risk from a series of vulnerabilitiesLeer másElectron-based desktop...
New Attack Weaponizes PLCs to Hack Enterprise and OT Networks
New Attack Weaponizes PLCs to Hack Enterprise and OT NetworksThe research resulted in proof-of-concept exploits against seven market-leading automation firmsLeer másThe research resulted in proof-of-concept exploits...
Healthcare Provider Issues Warning After Tracking Pixels Leak Patient Data
Healthcare Provider Issues Warning After Tracking Pixels Leak Patient DataThe leak was caused by incorrect configurations of an online tracking tool from MetaLeer másThe leak was...
Two Additional Malicious Python Libraries Found on PyPI Repository
Two Additional Malicious Python Libraries Found on PyPI RepositoryThe new packages were masquerading as one of the most popular open-source packages on PyPILeer másThe new packages...
Bug Bounty Giant Slams Quality of Vendor Patching
Bug Bounty Giant Slams Quality of Vendor PatchingZero Day Initiative says incomplete or faulty patches now commonplaceLeer másZero Day Initiative says incomplete or faulty patches now...
USBs Still a Major OT Infection Vector
USBs Still a Major OT Infection VectorManufacturing was most exposed to OT threats in 2021Leer másManufacturing was most exposed to OT threats in 2021
Identity Scams Soar to Make 2021 a Record Year
Identity Scams Soar to Make 2021 a Record YearNon-profit says Google Voice scams were the most reported threatLeer másNon-profit says Google Voice scams were the most...
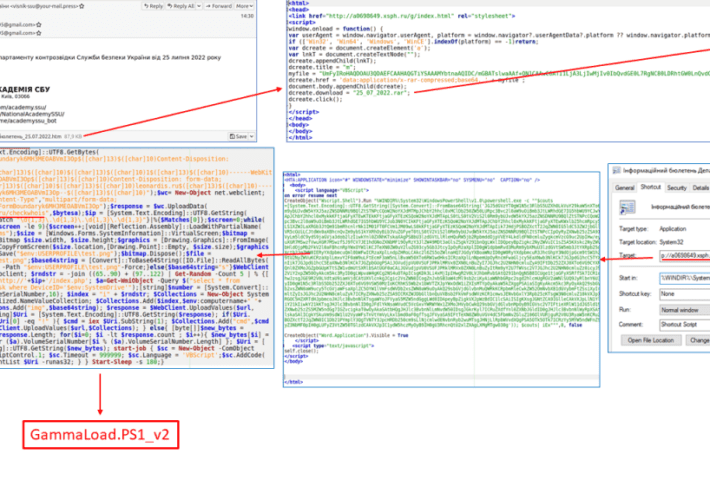
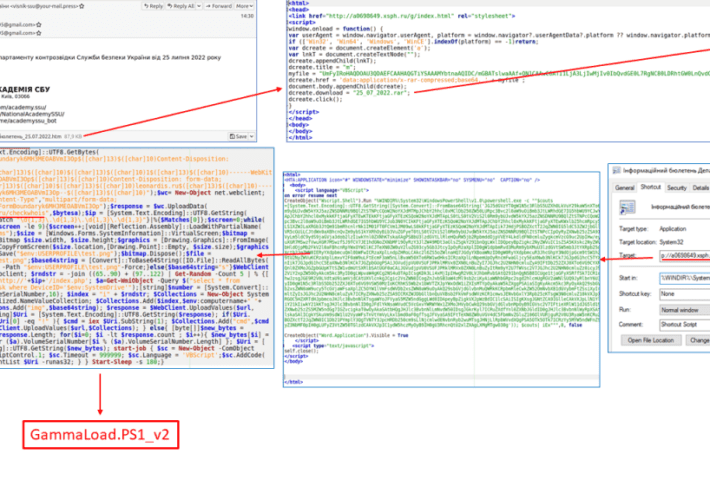
Russia-linked Gamaredon APT continues to target Ukraine
Russia-linked Gamaredon APT continues to target UkraineRussia-linked Gamaredon APT group targets Ukrainian entities with PowerShell info-stealer malware dubbed GammaLoad. Russia-linked Gamaredon APT group (aka Shuckworm, Actinium, Armageddon, Primitive...
Russia-linked Gamaredon APT continues to target Ukraine
Russia-linked Gamaredon APT continues to target UkraineRussia-linked Gamaredon APT group targets Ukrainian entities with PowerShell info-stealer malware dubbed GammaLoad. Russia-linked Gamaredon APT group (aka Shuckworm, Actinium, Armageddon, Primitive...
Organizations Struggle to Fend Off Cloud and Web Attacks
Organizations Struggle to Fend Off Cloud and Web AttacksThe study queries more than 950 IT and security professionals across the Americas, EMEA and APACLeer másThe study...
RubyGems Mandates MFA for Top-100 Package Maintainers
RubyGems Mandates MFA for Top-100 Package MaintainersThe package manager started enforcing MFA on owners of gems with over 180 million total downloadsLeer másThe package manager started...
New Deep Instinct partner program targets MSSPs fighting ransomware
New Deep Instinct partner program targets MSSPs fighting ransomwareCybersecurity firm Deep Instinct has rolled out a new partner program to provide its endpoint and application protection...
How a spoofed email passed the SPF check and landed in my inbox
How a spoofed email passed the SPF check and landed in my inboxThe Sender Policy Framework can’t help prevent spam and phishing if you allow billions...
APT Lazarus Targets Engineers with macOS Malware
APT Lazarus Targets Engineers with macOS MalwareThe North Korean APT is using a fake job posting for Coinbase in a cyberespionage campaign targeting users of both...
Clop gang targeted UK drinking water supplier South Staffordshire Water
Clop gang targeted UK drinking water supplier South Staffordshire WaterA cyber attack disrupted the IT operations of South Staffordshire Water, a company supplying drinking water to...
Zoom fixed two flaws in macOS App that were disclosed at DEF CON
Zoom fixed two flaws in macOS App that were disclosed at DEF CONZoom addressed two high-severity vulnerabilities in its macOS app that were disclosed at the...
Clop gang targeted UK drinking water supplier South Staffordshire Water
Clop gang targeted UK drinking water supplier South Staffordshire WaterA cyber attack disrupted the IT operations of South Staffordshire Water, a company supplying drinking water to...