Source: www.techrepublic.com - Author: Cedric Pernet A new variant of malware called XLoader is targeting macOS...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security TechRepublic
Source: www.techrepublic.com - Author: Cedric Pernet This QR code phishing campaign is targeting multiple industries and...
Source: www.techrepublic.com - Author: Karl Greenberg Image: Urupong/Adobe Stock At a Google Cloud press event on...
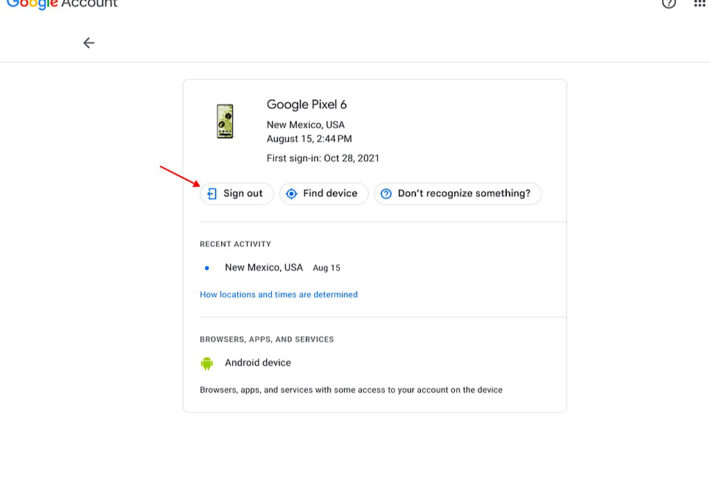
Source: www.techrepublic.com - Author: Andy Wolber on August 24, 2023, 9:48 AM EDT How to Remove...
Source: www.techrepublic.com - Author: Karl Greenberg on August 24, 2023, 9:12 AM EDT Critical Insight Reports...
Source: www.techrepublic.com - Author: Karl Greenberg Image: PB Studio Photo/Adobe Stock Generative AI was — not...
Source: www.techrepublic.com - Author: This policy provides guidelines for the appropriate use of electronic communications. It...
Source: www.techrepublic.com - Author: Megan Crouse Explore enterprise applications and infrastructure, AI, tools for the remote...
Source: www.techrepublic.com - Author: Phil Hajjar on August 22, 2023, 10:23 AM EDT How to Quickly...
Source: www.techrepublic.com - Author: Smart spaces bring together universal connectivity, security, and intelligence to modernize the...
Source: www.techrepublic.com - Author: Did you know that about 99% of surveillance video goes unviewed? What...
Source: www.techrepublic.com - Author: Karl Greenberg Image: Adobe Stock/Jimon Akamai’s ransomware report released at Black Hat...
Source: www.techrepublic.com - Author: Franklin Okeke This is a comprehensive ExpressVPN Review, covering features, pricing, and...
Source: www.techrepublic.com - Author: Cedric Pernet on August 18, 2023, 3:26 PM EDT About 2000 Citrix...
Source: www.techrepublic.com - Author: Jonathan Kalibbala Unitrends Backup and Recovery: Best for AI-based backups and disaster...
Source: www.techrepublic.com - Author: Jesus Vigo on August 17, 2023, 9:51 AM EDT 7 Ways to...
Source: www.techrepublic.com - Author: Andy Wolber on August 17, 2023, 8:58 AM EDT How to Retrieve...
Source: www.techrepublic.com - Author: Stories of virus and malware infections, data loss, system compromises and unauthorized...
Source: www.techrepublic.com - Author: Cybersecurity attacks are inevitable for modern businesses. Therefore, it is vital that...
Source: www.techrepublic.com - Author: TechRepublic Academy on August 16, 2023, 5:21 AM EDT Get Norton 360...
Source: www.techrepublic.com - Author: In many ways, data has become the primary currency of modern organizations....
Source: www.techrepublic.com - Author: Mary Branscombe Image: monticellllo/Adobe Stock Almost 90% of enterprises use more than...
Source: www.techrepublic.com - Author: Megan Crouse Image: AVC Photo Studio/Adobe Stock OpenAI, Google, Meta and more...
Source: www.techrepublic.com - Author: Unmanned aircraft systems, more commonly known as drones, have quite literally taken...
Source: www.techrepublic.com - Author: Karl Greenberg Image: Adobe Stock/Scanrail At a restaurant where the waiters, chefs...
Source: www.techrepublic.com - Author: Erik Eckel The temptation to use your personal Mac to check work...
Source: www.techrepublic.com - Author: Cedric Pernet This attack sent approximately 120,000 phishing emails to organizations worldwide...
Source: www.techrepublic.com - Author: Karl Greenberg Adobe stock, by Busra At the Black Hat kickoff keynote...
Source: www.techrepublic.com - Author: Drew Robb Enterprise IT teams are struggling to cope with three major...
Source: www.techrepublic.com - Author: Franklin Okeke Image: RareStock/Adobe Stock Application development often requires the integration of...