Source: www.techrepublic.com - Author: Megan Crouse The tech industry courses people are taking online can tell...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security TechRepublic
Source: www.techrepublic.com - Author: Drew Robb We may earn from vendors via affiliate links or sponsorships....
Source: www.techrepublic.com - Author: Megan Crouse The RSA Conference, held in San Francisco from May 6-9,...
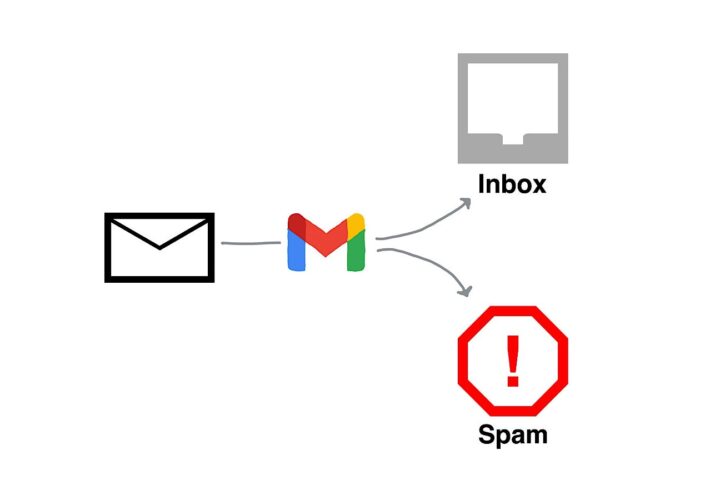
Source: www.techrepublic.com - Author: Andy Wolber Starting in early 2024, Google tightened three enforcement efforts in...
Source: www.techrepublic.com - Author: The first step to increasing your business’ cybersecurity is to educate yourself...
Source: www.techrepublic.com - Author: Fiona Jackson The U.K.’s National Cyber Security Centre (NCSC) and other international...
Source: www.techrepublic.com - Author: Ben Abbott Working for a salary in tech has been somewhat of...
Source: www.techrepublic.com - Author: Fiona Jackson The realm of the Internet of Things encompasses more than...
Source: www.techrepublic.com - Author: Drew Robb We may earn from vendors via affiliate links or sponsorships....
Source: www.techrepublic.com - Author: Megan Crouse Security researchers in Adobe’s bug bounty program can now pick...
Source: www.techrepublic.com - Author: Franklin Okeke We may earn from vendors via affiliate links or sponsorships....
Source: www.techrepublic.com - Author: Megan Crouse The number of Microsoft vulnerabilities has mostly flattened in 2023,...
Source: www.techrepublic.com - Author: Fiona Jackson The GPT-4 large language model from OpenAI can exploit real-world...
Source: www.techrepublic.com - Author: Megan Crouse Only 17% of respondents to the ISC2 Cybersecurity Workforce Study...
Source: www.techrepublic.com - Author: TechRepublic Academy Published April 25, 2024 We may earn from vendors via...
Source: www.techrepublic.com - Author: Fiona Jackson AI’s newfound accessibility will cause a surge in prompt hacking...
Source: www.techrepublic.com - Author: Luis Millares A virtual private network is one of the easiest ways...
Source: www.techrepublic.com - Author: Threats from malware, cryptographic infections and compromised networks have never been greater....
Source: www.techrepublic.com - Author: The tech world has a problem: Security fragmentation. There’s no standard set...
Source: www.techrepublic.com - Author: Fiona Jackson Businesses are one step closer to quantum cloud computing, thanks...
Source: www.techrepublic.com - Author: Fiona Jackson The number of devices infected with data-stealing malware in 2023...
Source: www.techrepublic.com - Author: The Data Encryption Policy’s purpose is to define for employees, computer users...
Source: www.techrepublic.com - Author: Luis Millares Yes, virtual private networks are worth it. In today’s digital...
Source: www.techrepublic.com - Author: Luis Millares Speedify VPN fast facts Our rating: 3.1 stars out of...
Source: www.techrepublic.com - Author: Luis Millares Private Internet Access Fast facts Our rating: 4.2 stars out...
Source: www.techrepublic.com - Author: Fiona Jackson Apple sent a threat notification to iPhone users in 92...
Source: www.techrepublic.com - Author: Fiona Jackson Organisations that have backed up their sensitive data may believe...
Source: www.techrepublic.com - Author: Digital information is generally the lifeblood of any given organization, containing essential...
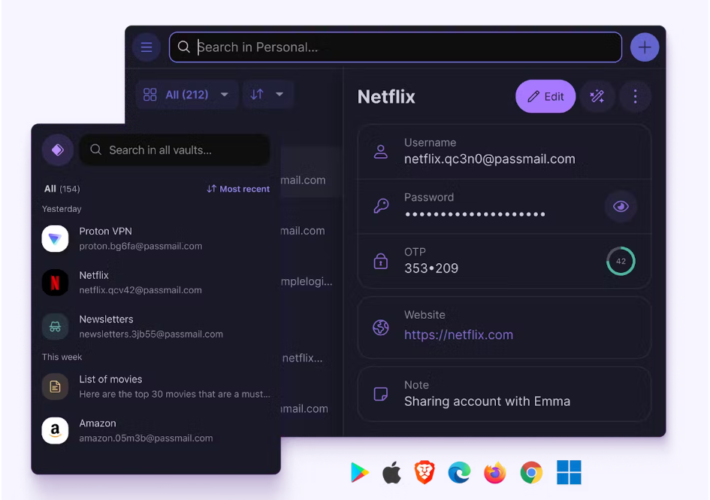
Source: www.techrepublic.com - Author: Luis Millares We may earn from vendors via affiliate links or sponsorships....
Source: www.techrepublic.com - Author: Cybercriminal activity is increasing. It is no longer a matter of if...