Source: securityboulevard.com - Author: Marc Handelman Permalink *** This is a Security Bloggers Network syndicated blog...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
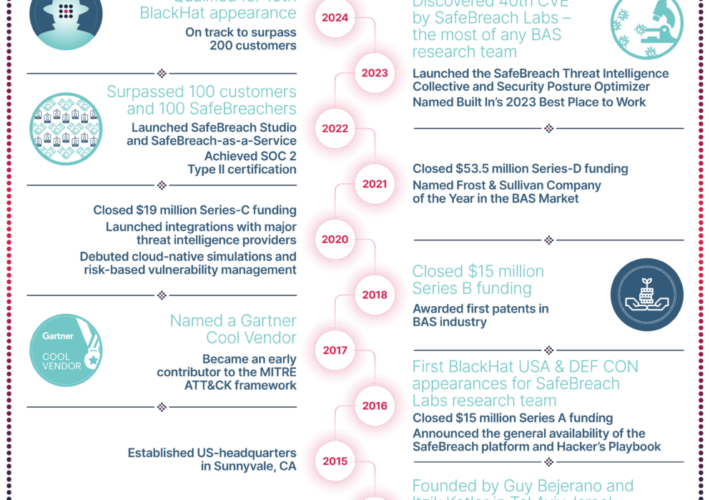
Source: securityboulevard.com - Author: SafeBreach We all know cybersecurity is a team sport—one that is enhanced...
Source: securityboulevard.com - Author: Maahnoor Siddiqui After several years of deliberation and collaboration with industry experts,...
Source: securityboulevard.com - Author: Gabi Stapel A critical security flaw, identified as CVE-2024-1071, was discovered in...
Source: securityboulevard.com - Author: Sarah Hunter-Lascoskie When a customer signs up for a loyalty program or...
Source: securityboulevard.com - Author: Marc Handelman Hot Topics USENIX Security ’23 - Yu Chen, Yang Yu,...
Source: securityboulevard.com - Author: Michael Vizard A report published today by Synopsys finds nearly three-quarters (74%)...
Source: securityboulevard.com - Author: John Gallagher Surveys play an important role in setting strategy and choosing...
Source: securityboulevard.com - Author: Kevin Smith Most school districts are equipped to deal with an emergency—whether...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Jan Philipp Thoma, Christian Niesler, Dominic Funke, Gregor Leander,...
Source: securityboulevard.com - Author: cyberwire Brea, Calif. Feb. 27, 2024 — The current large surge in...
Source: securityboulevard.com - Author: Richi Jennings State Dept. Global Engagement Centre chief James Rubin (pictured) follows...
Source: securityboulevard.com - Author: Team Nuspire UnitedHealth Group, the largest healthcare company in the world by...
Source: securityboulevard.com - Author: Lee Painter It goes without saying that password management is essential to...
Source: securityboulevard.com - Author: Lee Painter Many employees at all kinds of businesses can suffer from...
Source: securityboulevard.com - Author: Francis Guibernau On February 26, 2024, the Cybersecurity & Infrastructure Security Agency...
Source: securityboulevard.com - Author: Jeffrey Burt Threat groups continue to look to open source software repositories...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Jiyong Yu, Aishani Dutta, Trent Jaeger, David Kohlbrenner, Christopher...
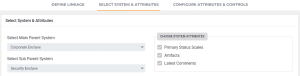
Source: securityboulevard.com - Author: Ignyte Team If you are managing multiple GRC frameworks for multiple environments,...
Making Companies Whole: The Impact of Cyber Insurance on Materiality – Source: securityboulevard.com
Source: securityboulevard.com - Author: Axio Hot Topics Malicious Packages in npm, PyPI Highlight Supply-Chain Threat USENIX...
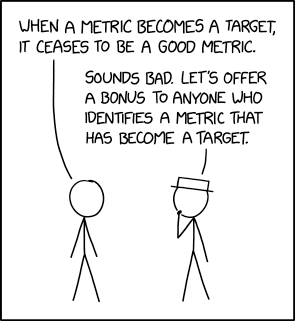
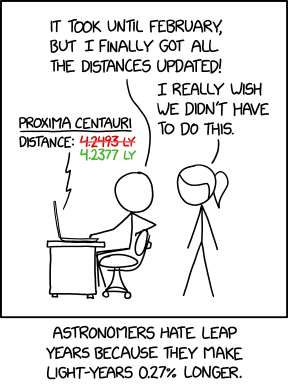
Source: securityboulevard.com - Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security...
Source: securityboulevard.com - Author: Jeffrey Burt The LockBit ransomware group is swinging back days after U.S....
Source: securityboulevard.com - Author: Gilad David Maayan Before we dive into the xSPM trend, let’s define...
Source: securityboulevard.com - Author: Dancho Danchev The popular cybercrime-friendly xDedic service was recently shut down and...
Source: securityboulevard.com - Author: Maria Chachas Mastakas For about a decade, much has been written about...
Source: securityboulevard.com - Author: Matt Palmer Passwords should be the easiest area of security. Every organisation...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity In this interview, Pavlina Pavlova, public policy adviser at...
Source: securityboulevard.com - Author: Rom Carmel Organizations often use multiple applications to perform business. For example,...
Source: securityboulevard.com - Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security...