Tesla and Twitter Should be Banned as Threats to Global Security As you may remember, I’ve...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
All You Need to Know About Secure Shell Protocol An Ultimate Guide on Secure Shell, What...
BSidesPDX 2022 – Pim Trouerbach’s ‘Smokeloader: The Pandora’s Box Of Tricks, Payloads And Anti-Analysis’ Our sincere...
2022 Midterm Election Cybersecurity: Are We Ready? As we head into the pivotal 2022 midterm elections...
The Week in Security: OpenSSL danger downgraded but still real, GitHub exposed Welcome to the latest...
Security Awareness Needs a New Experience, Not More New Content If you are shopping for a...
BSidesPDX 2022 – Ken Westin’s ‘Opening Remarks’ Our sincere thanks to BSidesPDX 2022 for publishing their...
CVE-2022-3602 and CVE-2022-3786 OpenSSL Vulnerabilities: Scanning Container Images On November 1st, 2022, OpenSSL announced a pair...
Cyber Security and Segregation of Duties What Cybersecurity Needs To Know About Segregation Of DutiesCybersecurity has...
Analyzing CISA Known Exploited Vulnerabilities with Business Context What is CISA Directive BOD 22-01? In November...
What You Need to Know About SBOM Generation Tools When it comes to tools for generating...
Five Tips for Low-Friction Authentication Authentication processes often introduce unwelcome friction into the user experience. Generally...
How can Identity Verification prevent scams in MLM and D2C industries? In India, there have been...
What is an Organization Validation (OV) Code Signing Certificate? An organization must utilize an OV Code...
Emergency plan: What to do if you’ve been hacked Your family has a plan in case...
6 Steps to Ensure Compliance For Your Storage & Backup Systems Here are just a few...
DRaaS Leads Companies Into the World of Cloud As more and more large enterprises adopt cloud...
14 All Day DevOps (ADDO) Sessions You Won’t Want to Miss The post 14 All...
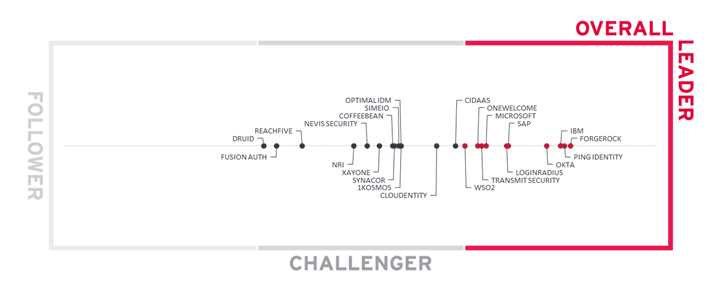
The Road to Passwordless is Paved with Orchestration A new report from KuppingerCole Names ForgeRock an...
BSidesLV 2022 Lucky13 I Am The Cavalry (IATC) – Allan Friedman’s, Adam Kojak’s, Katie Bratman’s, Chris...
Security Advisory for OpenSSL Vulnerabilities CVE-2022-3602 & CVE-2022-3786 Background On 01-Nov-2022, OpenSSL published an advisory about...
SOVA – A New Android Banking Trojan Introduction How many people are aware of the new...
Complete Guide on Comodo Code Signing Certificate Comodo is a cybersecurity solutions provider helping businesses and...
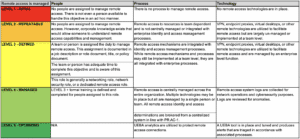
Measuring Up: How to Architect a Systematic Security Program – Part 2 In Part 1 of...
See Tickets Breach Sheds Light on the Blind-Side of Web Security Despite its name, leading ticketing...
BSidesLV 2022 Lucky13 I Am The Cavalry (IATC) – Lily H. Newman’s, Joe Uchill’s, Suzanne Smalley’s...
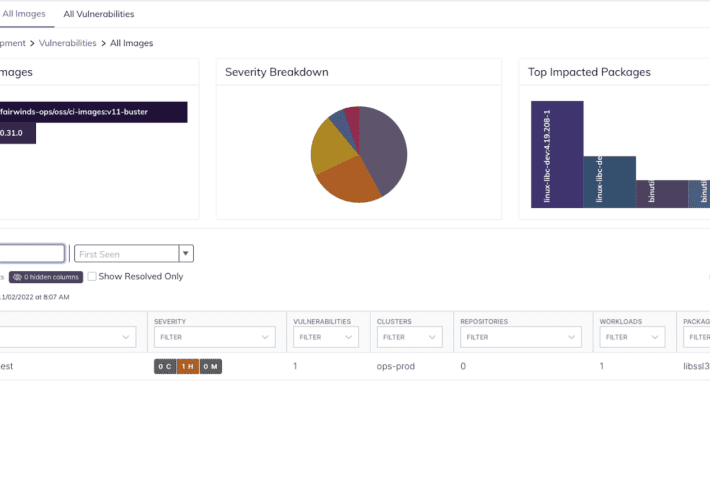
Using Binary Analysis to Hunt Down OSS Vulnerabilities Having an SBOM and software inventory aids in...
Using Sysmon for Linux to Monitor Against MITRE ATT&CK Techniques There was a lot covered at...
Hacking with your Browser Today I rebuilt my Windows 7 partition. Amidst flurry of backing up...
Metasploit Buyout Today HD Moore and Rapid7 announced that Rapid7 has purchased the Metasploit Framework Project....