Source: securityboulevard.com - Author: Kelly Dougherty Welcome to the “Life in the Swimlane” blog series. Here...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Kayne McGladrey Last year, the Securities and Exchange Commission (SEC) announced new...
Source: securityboulevard.com - Author: Dex Tovin Secret scanning is essential for unlocking next-level software supply chain...
Source: securityboulevard.com - Author: Dave Lewis It has been a long time since I last posted...
Source: securityboulevard.com - Author: Laura Bruck March 25, 2024[1] — Social Links, a leading developer of...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
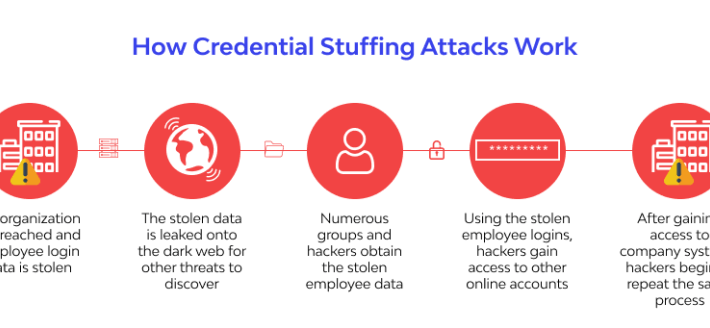
Source: securityboulevard.com - Author: wlrmblog All industries are at risk of credential stuffing and account takeover...
Source: securityboulevard.com - Author: Kevin Smith In the event of a security breach, logs play a...
Source: securityboulevard.com - Author: Wajahat Raja Tomer Peled, an Akamai cybersecurity security researcher, recently discovered a...
Source: securityboulevard.com - Author: madhav Amid ongoing economic uncertainty and a progressively complex threat landscape, businesses...
Source: securityboulevard.com - Author: Tom Eston In this episode, special guest Alyssa Miller joins the hosts...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity Cybersecurity experts from state and local government, as well...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: hrbrmstr VulnCheck has some new, free API endpoints for the cybersecurity community....
Source: securityboulevard.com - Author: Max Aulakh Whenever a business wants to work with the federal government,...
Source: securityboulevard.com - Author: hrbrmstr I use Fantastical as it’s a much cleaner and native interface...
Source: securityboulevard.com - Author: John Gallagher IoT devices and applications exist all over the place, and...
Source: securityboulevard.com - Author: Wajahat Raja As per recent reports, threat actors are increasingly leveraging Facebook...
Source: securityboulevard.com - Author: Kari Hulkko Exploitation IP address spoofing involves creating IP packets with a...
Source: securityboulevard.com - Author: Shelley Leveson, Director of Content Marketing, HYPR The National Security Agency (NSA),...
Source: securityboulevard.com - Author: Neatsun Ziv Historically, Security Operations Centers (SOCs) and Application Security (AppSec) programs...
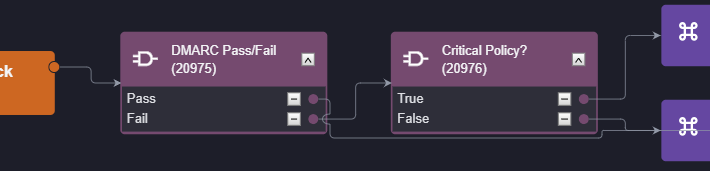
Source: securityboulevard.com - Author: Kartik Subramanian, Engineering Welcome the third part of our series on how...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Mingshi Wu, Jackson Sippe, Danesh Sivakumar, Jack Burg, Peter...
Source: securityboulevard.com - Author: Rohan Ramesh With the turn of the 20th century and the rise...
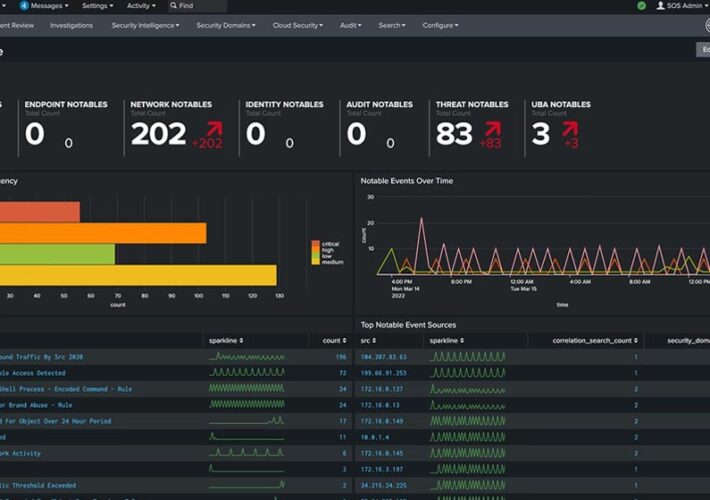
Source: securityboulevard.com - Author: LogRhythm Dataproof Communications is a leading IT Services and Consulting Company specializing...
Source: securityboulevard.com - Author: Kevin Smith The losses companies suffered in 2023 ransomware attacks increased by...
Source: securityboulevard.com - Author: Dwayne McDaniel On March 19th, news broke that researchers uncovered more than...
Source: securityboulevard.com - Author: Aravind Iyengar Creating an accurate inventory of an organization’s assets and applications...
Source: securityboulevard.com - Author: Tom Eston In episode 321, the hosts discuss how connected cars are...