Source: securityboulevard.com - Author: cybernewswire Tel Aviv, Israel, May 2nd, 2024, CyberNewsWire Early adoption by Fortune...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: EasyDmarc This instructional article will demonstrate the Survalyzer configuration process of Sender...
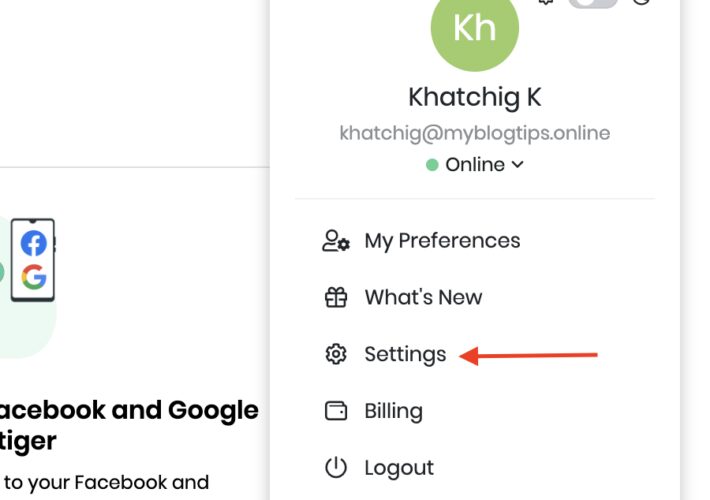
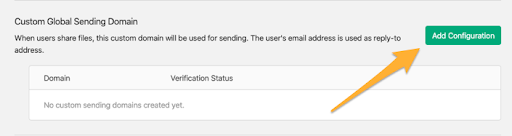
Source: securityboulevard.com - Author: EasyDmarc Vtiger is a cloud-based CRM that enables businesses to deliver outstanding...
Source: securityboulevard.com - Author: EasyDmarc This instructional article will demonstrate the Spamhero configuration process of Sender...
Source: securityboulevard.com - Author: Leah Hopper Introduction Phishing attacks are an increasingly frequent problem and a...
Source: securityboulevard.com - Author: EasyDmarc This instructional article will demonstrate the Simply configuration process of Sender...
Source: securityboulevard.com - Author: EasyDmarc This instructional article will demonstrate the Showpad configuration process of Sender...
Source: securityboulevard.com - Author: EasyDmarc This instructional article will demonstrate the Rocketseed configuration process of Sender...
Source: securityboulevard.com - Author: Michael Vizard Venafi today launched an initiative to help organizations prepare to...
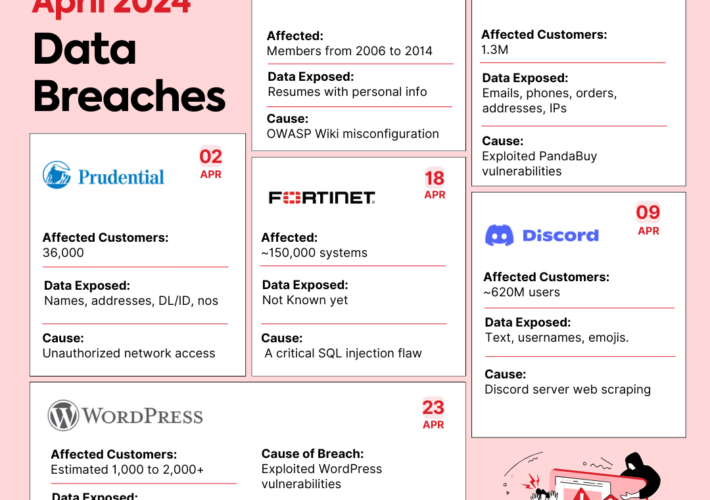
Source: securityboulevard.com - Author: Shubham Jha Data breaches are like uninvited guests at a party –...
Source: securityboulevard.com - Author: Cyborg Security The fusion of Cyborg Security with Intel 471 delivers advanced...
Source: securityboulevard.com - Author: NSFOCUS The RSA Conference 2024 will kick off on May 6. Known...
Source: securityboulevard.com - Author: Kaseya The technology industry continually evolves, and managed service providers (MSPs) are...
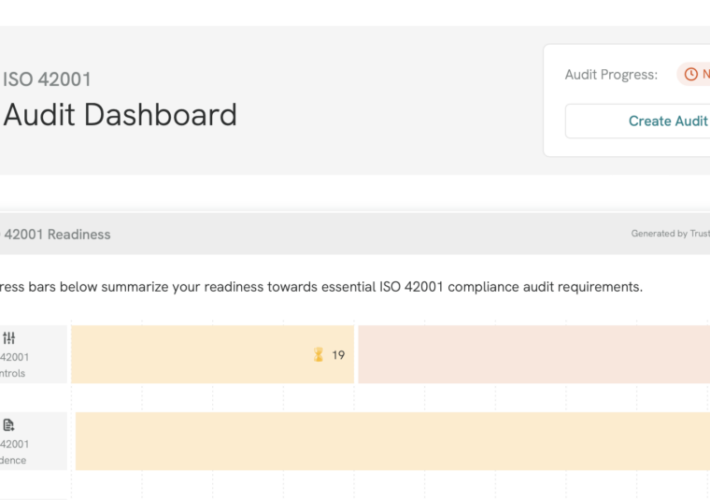
Source: securityboulevard.com - Author: Tejas Ranade While AI has created exciting new opportunities for business, it...
Source: securityboulevard.com - Author: Accutive Security What is PIPEDA, Canada’s Personal Information Protection and Electronic Documents...
Source: securityboulevard.com - Author: Tejas Ranade You know us: Every month we’re cooking up something new!...
Source: securityboulevard.com - Author: bacohido Tel Aviv, Israel – April 30, 2024 – Cybersixgill, the global cyber threat intelligence data...
Source: securityboulevard.com - Author: Tally Shea Amazon Web Services (AWS) has over 200 cloud services available...
Source: securityboulevard.com - Author: Lauren Yacono A zero-day attack leaves your software vulnerable to being exploited...
Source: securityboulevard.com - Author: Krupa Patil SSH and SSL/TLS are two widely used cryptographic protocols for...
Source: securityboulevard.com - Author: Nathan Eddy Global ransomware attacks rose slightly in March compared to the...
Source: securityboulevard.com - Author: Rohan Timalsina The Ubuntu security team recently addressed several Apache HTTP Server...
Source: securityboulevard.com - Author: Nik Hewitt How can security teams be ready for holiday cyberattacks and...
Source: securityboulevard.com - Author: Anca Trusca Debian holds a distinguished position. Recognized as one of the...
Source: securityboulevard.com - Author: Wajahat Raja In the realm of cybersecurity, vigilance is paramount. Recent discoveries...
Source: securityboulevard.com - Author: Riddika Grover The rise of digital technology has provided great convenience to...
Source: securityboulevard.com - Author: Farah Iyer The MITRE ATT&CK framework is a continually evolving resource, tracking...
Source: securityboulevard.com - Author: Matt Palmer Cyber security is often conflated with the term confidentiality, but...
Source: securityboulevard.com - Author: Jeffrey Burt The takedown this week of a massive phishing-as-a-service (PhaaS) operation...
Source: securityboulevard.com - Author: Shriram Sharma Security operations centers (SOCs) are the front lines in the...






















![Choosing SOC Tools? Read This First [2024 Guide] – Source: securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2024/04/128699/choosing-soc-tools-read-this-first-2024-guide-source-securityboulevard-com-710x500.jpg)





