When to Use Penetration Testing Software, Services, or Both The post When to Use Penetration Testing...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
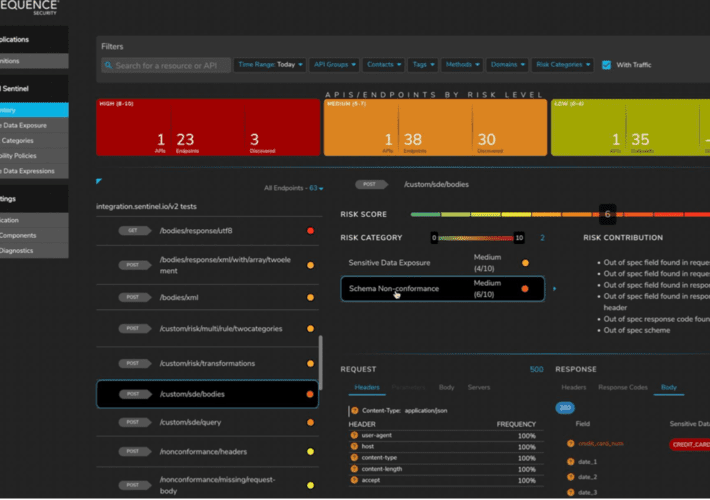
Unified API Protection for Telcos and Mobile Carriers – Time to Value Largest Mobile Carrier Identified...
BSidesTLV 2022 – Shira Stepansky’s ‘Diamond Model Analysis Of Whatsapp Security Breach’ Our thanks to BSidesTLV...
IAM budget in a recession How to make the most out of your 2023 IAM budget...
LastPass Breach Raises Disclosure Transparency Concerns In the graphic novel “The Watchman” by Alan Moore and...
The inevitable pivot to BYOA (Bring Your Own Application): Mitigating risk to enable innovation Security teams...
Security and Cheap Complexity I’ve been saying that complexity is the worst enemy of security for...
Cybersecurity Insights with Contrast CISO David Lindner | 8/26 Insight #1 “ If you are struggling...
What I wish I knew about security when I started programming It’s critical for developers to...
Insurers May Not Cover ‘State-Sponsored’ Cyberattacks Many of the more expensive cyberattacks and ransomware attacks, including...
Confidential Computing Beats Homomorphic Encryption for Data Security For the enterprise, data is like the air...
Cybersecurity News Round-Up: Week of August 22, 2022 Twitter’s Ex-CSO accuses the company of cybersecurity negligence,...
LastPass attackers steal source code, no evidence users’ passwords compromised LastPass, the popular password manager used...
The 4 Best Open Source PKI Software Solutions (And Choosing the Right One) In the never-ending...
TSA Requirements: A Snapshot of Growing Attention to Pipeline Cybersecurity The post TSA Requirements: A Snapshot...
What Is a TLS/SSL Port? What Is a TLS/SSL Port? 97thfloor Fri, 08/26/2022 – 09:15 1...
How to Comply With the US Government’s Strict Software Requirements We break down H.R. 7900, a...
Daniel Stori’s ‘How To Cut Onions Without Tears (Using Oracle)’ via the inimitable Daniel Stori, crafting...
What is Big Data Security? Large organizations and enterprises are embracing big data like never before....
Defending in a hostile environment: Key findings from the BlackHat NOC Key points The Black Hat...
FinOps “Crawl, Walk, Run” Maturity Model Applied to Kubernetes FinOps has become an increasingly popular goal...
2022 Cequence Roadshow — Learn the ABCs of API Protection Summer’s almost over, and it’s time...
Case Study: DTEX InTERCEPT Helps Multinational Retailer Gain Visibility into Risk in Retail Stores As insider...
BSidesTLV 2022 – Ayelet HaShachar Penrod’s ‘Hack LinkedIn Networking (The People Skill, Not The Tech Skill)’...
Elastic Security Advances SOAR Integration Elastic Security today updated its security orchestration, automation and response (SOAR)...
Security Awareness Games in Slack Users love ❤️ learning in Slack. We hear this consistently from...
BSidesTLV 2022 – Gal Bitensky’s ‘SS-Oh No!’ Our thanks to BSidesTLV for publishing their outstanding conference...
Hacktivism and DDOS Attacks Rise Dramatically in 2022 2022 has brought a surge in distributed denial-of-service...
How to Mitigate Insider Threat Using Internal Controls As your company grows, you’ll want to reduce...
BSidesTLV 2022 – Rotem Reiss’ ‘Code C.A.I.N – Keeping Your Source Code Under Control’ Our thanks...