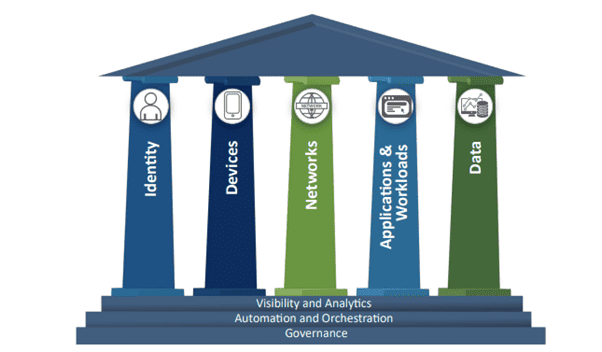
Source: securityboulevard.com - Author: Bhagwat Swaroop When it comes to Zero Trust, the conversation has moved...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Aimee Simpson It’s no secret that sensitive data management is a top...
Source: securityboulevard.com - Author: Bruce Schneier A Peruvian oversight law has the opposite effect: Peru in...
Source: securityboulevard.com - Author: Richa Tiwari Achieving SOC 2 compliance often necessitates the use of specialized...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Jenn Sherman As you’ll recall from our last post, FedRAMP just soared...
Source: securityboulevard.com - Author: Richi Jennings Privacy Sandbox inching towards reality. But concerns remain.Google’s plan to...
Source: securityboulevard.com - Author: Danielle Cook If you’re thinking about building a Kubernetes platform that your...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Deepak Gupta - Tech Entrepreneur, Cybersecurity Author As businesses continue to evolve...
Source: securityboulevard.com - Author: Nathan D. By Nathan Davis This body of work also appears in the...
Source: securityboulevard.com - Author: Cyborg Security In the ever-evolving landscape of cybersecurity, two disciplines stand out:...
Source: securityboulevard.com - Author: Lalit Shinde My colleagues and our partners attended the annual IDC South...
Source: securityboulevard.com - Author: Gilad David Maayan Elastic Security, which includes Elastic security information and event...
Source: securityboulevard.com - Author: Dwayne McDaniel On the west coast of Canada, you will find Vancouver,...
Source: securityboulevard.com - Author: Mark Rasch Geolocation data is among the most sensitive personal data. Marketers...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Anchal Mehra The global decentralized identity market was valued at $285 million...
Source: securityboulevard.com - Author: Maahnoor Siddiqui Cybersecurity is no longer just an IT issue but a...
Source: securityboulevard.com - Author: Lauren Yacono Hot Topics Comic Agilé - Mikkel Noe-Nygaard, Luxshan Ratnarav -...
Source: securityboulevard.com - Author: Grip Security Blog Today, many organizations rely on software as a service...
Source: securityboulevard.com - Author: anecdotes Blog Lessons Sales and Compliance Can Learn from the Wolf of...
Source: securityboulevard.com - Author: Michael Vizard Aviatrix today made generally available a Distributed Cloud Firewall (DCF)...
Source: securityboulevard.com - Author: Jim Broome ChatGPT has become a powerful tool for security professionals seeking...
Source: securityboulevard.com - Author: LeaksID Watermarking has long been used as a method to protect digital...
Source: securityboulevard.com - Author: Michael Vizard IBM this week acquired Polar Security to add a data...
Source: securityboulevard.com - Author: Sebastian Wallin Automating account verification has become the norm for businesses to...
Source: securityboulevard.com - Author: Cavelo Blog Ever evolving and pervasive cyber threats are everywhere. The reality...
Source: securityboulevard.com - Author: Jonathan Bridges Every day, coordinated cybercriminal groups are developing more advanced skills...