Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Jeffrey Burt The Monti ransomware group that emerged in June 2022 used...
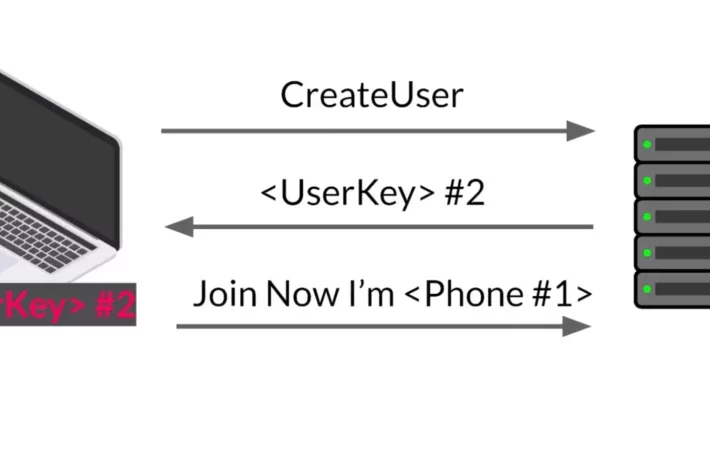
Source: securityboulevard.com - Author: Omer Attias Public transportation payment systems have undergone significant changes over the...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Adar Givoni, Director of Compliance, Scytale The Importance of Cybersecurity Cybersecurity is...
Source: securityboulevard.com - Author: Carolynn van Arsdale It’s not news that software supply chain attacks have...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
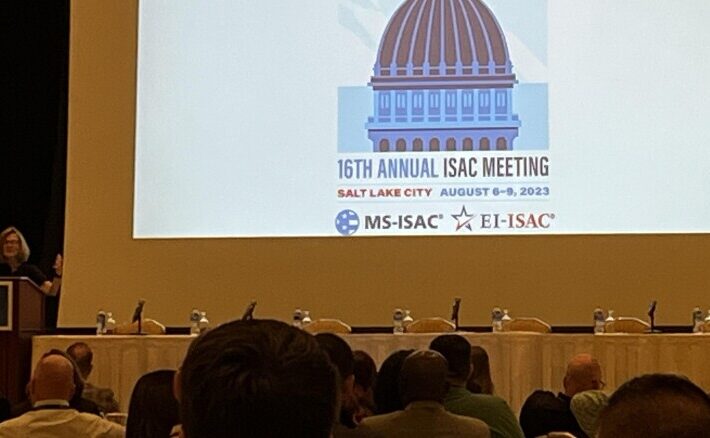
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity The 2023 MS-ISAC and EI-ISAC meeting just wrapped up...
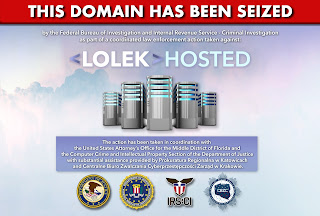
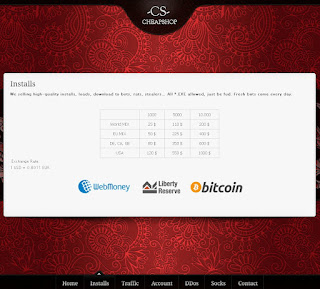
Source: securityboulevard.com - Author: Dancho Danchev In need of a fresh and relevant bulletproof hosting provider...
Source: securityboulevard.com - Author: Stefanie Shank Stefanie Shank Stefanie Shank. Having spent her career in various...
Source: securityboulevard.com - Author: Tony Bradley In today’s digital landscape, ensuring robust identity security and effective...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
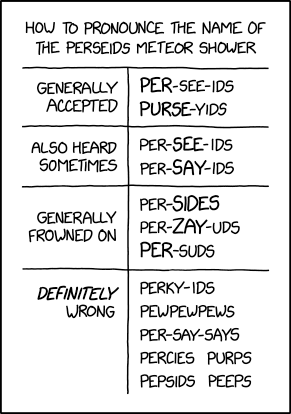
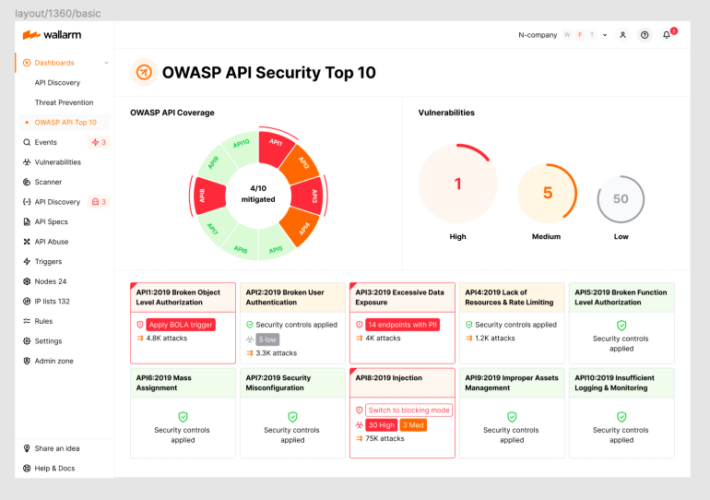
Source: securityboulevard.com - Author: wlrmblog Welcome to the 4th post in our weekly series on the...
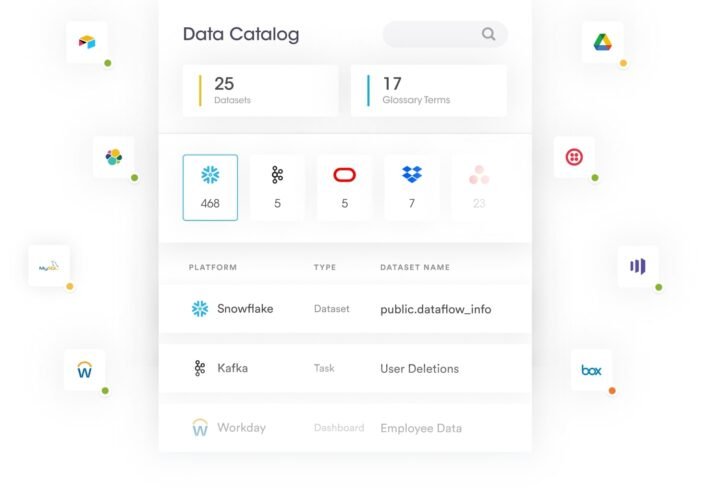
Source: securityboulevard.com - Author: Securiti Research Team With the rapid expansion of data across multiple clouds,...
Source: securityboulevard.com - Author: ForgeRock Guest Contributor The global biometrics market is expected to grow to...
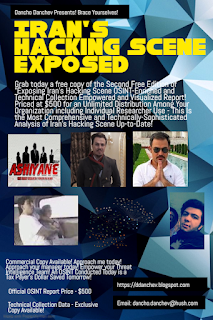
Source: securityboulevard.com - Author: Dancho Danchev In need of a freshly collected Iran-based hacker groups and...
Source: securityboulevard.com - Author: Dancho Danchev Who needs access to a recently collected portfolio of publicly...
Source: securityboulevard.com - Author: Dancho Danchev I just came across to a statement issued by the...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Michael Rothschild, VP of Product Marketing, HYPR The global digital ecosystem finds...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Maahnoor Siddiqui Cyber risk has become increasingly pervasive in almost every industry....
Source: securityboulevard.com - Author: Mimi Pham This is a guest post from Michael Marrano, MS, CISSP,...
Source: securityboulevard.com - Author: Team Solvo Organizations are increasingly turning to the cloud to reap the...
Source: securityboulevard.com - Author: James Horseman In December 2022, we competed at our first pwn2own. We...
Source: securityboulevard.com - Author: Michael Vizard Traceable AI has extended the reach of its application security...
Source: securityboulevard.com - Author: Sift Trust and Safety Team Advancements in technology have come a long...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original...
Source: securityboulevard.com - Author: Paul Asadoorian Favorite (Hacking) Things I really enjoy researching and acquiring “gadgets”....
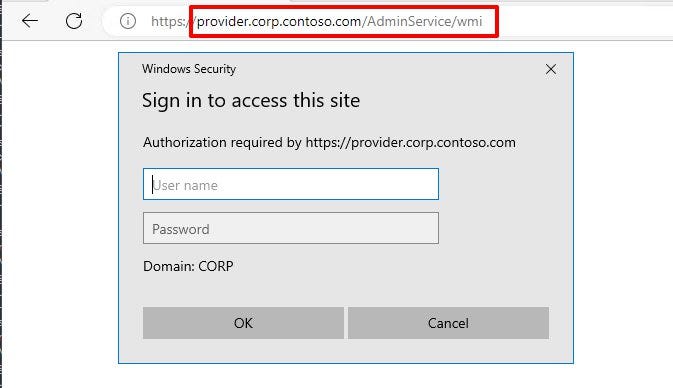
Source: securityboulevard.com - Author: Garrett Foster tl:dr: The SCCM AdminService API is vulnerable to NTLM relaying...

![BSides Leeds 2023 – Samantha Humphries – Destination Unknown: Career Musings Of A Former [Redacted] Agent – Source: securityboulevard.com](https://ciso2ciso.com/wp-content/uploads/2023/08/74074/bsides-leeds-2023-samantha-humphries-destination-unknown-career-musings-of-a-former-redacted-agent-source-securityboulevard-com-710x500.jpg)