Source: securityboulevard.com - Author: Trail of Bits By Spencer Michaels, William Woodruff, Jeff Braswell, and Cliff...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Mourne Fourie The last couple of years have seen a wave of...
Source: securityboulevard.com - Author: Mark Rasch Every year at this time, we look back at the...
Source: securityboulevard.com - Author: Emma Kelly San Antonio Woman Accused of Stealing $103 Million from US...
Source: securityboulevard.com - Author: Michelle Ofir Geveye Your business relies on a vast network of third-party...
Source: securityboulevard.com - Author: Marc Handelman Network Security Security Bloggers Network Home » Cybersecurity » Network Security...
Source: securityboulevard.com - Author: Nathan Sportsman Introduction With the recent rise and adoption of artificial intelligence...
Source: securityboulevard.com - Author: Mourne Fourie The purpose of PCI DSS is simply to ensure that...
Source: securityboulevard.com - Author: Yehuda Raz Today’s businesses don’t operate in a vacuum. To maintain high...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity What were the top government technology and security blogs...
Source: securityboulevard.com - Author: Amy Luby Execution is a fundamental component of success for any organization....
Source: securityboulevard.com - Author: Gary Warner The U.S. Attorney’s office in Delaware charged Olugbenga Lawal with...
Source: securityboulevard.com - Author: Dancho Danchev In this brief analysis I’ll take a look at who’s...
Source: securityboulevard.com - Author: Marc Handelman Saturday, January 13, 2024 Security Boulevard The Home of the...
Source: securityboulevard.com - Author: Avast Blog You may be searching for your soulmate, a low-risk situationship...
Source: securityboulevard.com - Author: Tony Bradley Tony Bradley I have a passion for technology and gadgets--with...
Source: securityboulevard.com - Author: Shriram Sharma We’re looking forward to having you join us for our...
Source: securityboulevard.com - Author: Marc Handelman Network Security Security Bloggers Network Home » Cybersecurity » Network Security...
Source: securityboulevard.com - Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community...
Source: securityboulevard.com - Author: Neeraj Gupta The landscape of online fraud has undergone a profound transformation...
Source: securityboulevard.com - Author: Mitch W Online brand impersonation attacks threaten businesses large and small, but...
Source: securityboulevard.com - Author: Lucy McCue In October 2023, we welcomed Arif Husain to the team...
Source: securityboulevard.com - Author: Seed and Soil Knowing this will allow you to have these customized...
Source: securityboulevard.com - Author: Marc Handelman Network Security Security Bloggers Network Home » Cybersecurity » Network Security...
Source: securityboulevard.com - Author: Jeffrey Burt The Federal Communications Commission is pressing automakers and wireless service...
Source: securityboulevard.com - Author: Richi Jennings Under active exploitation since last year—but still no patch available.A critical zero-day...
Source: securityboulevard.com - Author: Julie Peterson The typical global enterprise has over 12,000 web-based applications, including...
Source: securityboulevard.com - Author: Dilan Krishnamurthy Countless data breaches are exposed daily, and finding the vulnerabilities...
Source: securityboulevard.com - Author: Marc Handelman Thursday, January 11, 2024 Security Boulevard The Home of the...
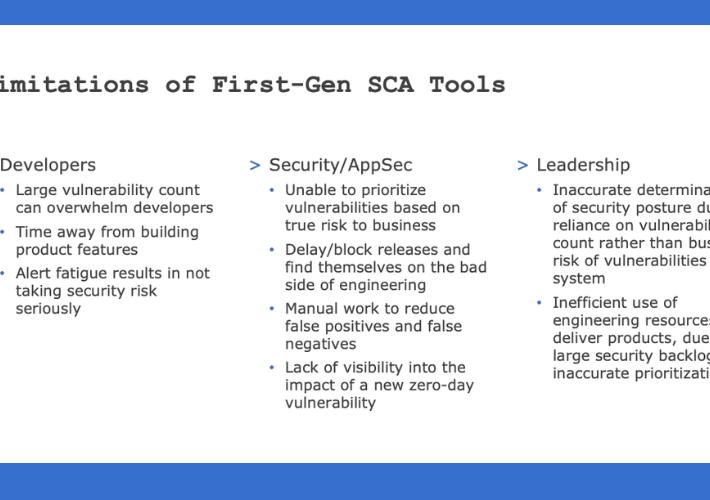
Source: securityboulevard.com - Author: William Penfield Sprawl happens Software development organizations evolve. Teams grow. The number...