Source: securityboulevard.com - Author: Marc Handelman Thursday, February 1, 2024 Security Boulevard The Home of the...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Team Nuspire Cybersecurity is a fast-paced and constantly changing industry. Ongoing technological...
Source: securityboulevard.com - Author: Jeffrey Burt The encrypted messaging app Telegram has become a veritable marketplace...
Source: securityboulevard.com - Author: Raymond Kirk The SOC 2 Effect: Elevating Security and Trust in Netography...
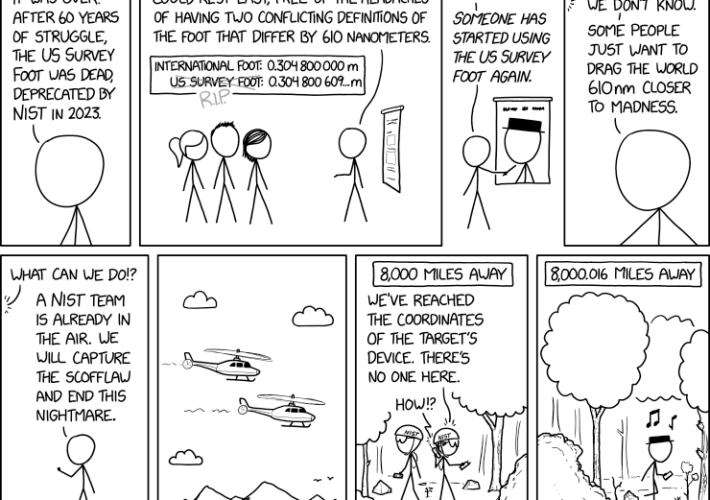
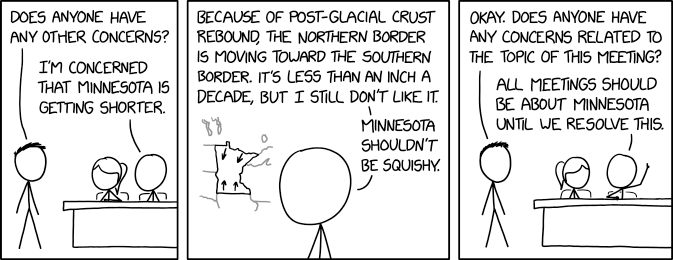
Source: securityboulevard.com - Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Impart Security Blog We’re proud to announce Impart Security’s newest release,...
Source: securityboulevard.com - Author: Hyperproof Team Managing controls across multiple business units becomes increasingly challenging and...
Source: securityboulevard.com - Author: Richi Jennings FBI head Wray won’t tolerate China’s “real-world threat to our...
Source: securityboulevard.com - Author: Marc Handelman Sponsorships Available Author/Presenters: Théophile Wallez, Inria Paris; Jonathan Protzenko, Benjamin...
Source: securityboulevard.com - Author: Michael Vizard Aim Security this week emerged from stealth to launch a...
Source: securityboulevard.com - Author: Tamara Bailey, Content Marketing Specialist @ AppOmni San Francisco, CA – [January...
Source: securityboulevard.com - Author: bacohido San Francisco, Calif., Jan. 31, 2024 – Reken, an AI &...
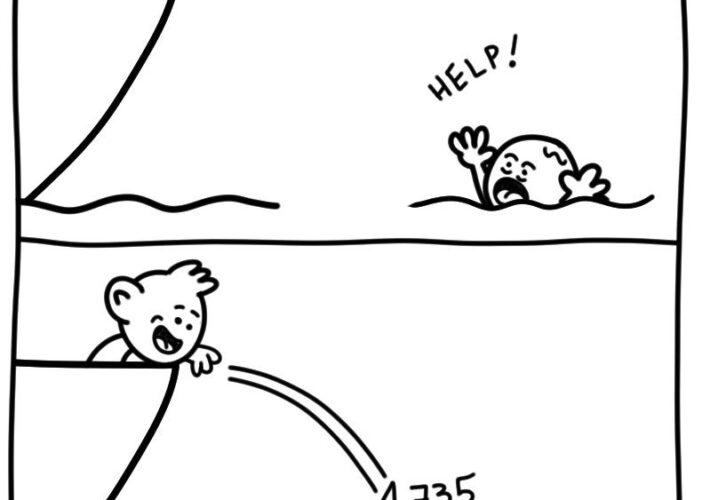
Source: securityboulevard.com - Author: Marc Handelman via the webcomic talent of the inimitable Daniel Stori at...
Source: securityboulevard.com - Author: Richi Jennings Government ministry denies hackers hacked its network infrastructure.The Russian internet was...
Source: securityboulevard.com - Author: Jeffrey Burt It’s still relatively early in the year, but bad actors...
Source: securityboulevard.com - Author: The Coalfire Blog The surge in electric vehicles (EVs) and expanding EV...
Source: securityboulevard.com - Author: Flare The Network Information Systems Directive (NIS2) and its predecessor NIS focus...
Source: securityboulevard.com - Author: Sift Trust and Safety Team Business is booming for online food delivery...
Source: securityboulevard.com - Author: Marc Handelman Author/Presenters: Heng Li, Zhang Cheng, Bang Wu, Liheng Yuan, Cuiying...
Source: securityboulevard.com - Author: David Ratner With high-profile breaches in the news across the world and...
Source: securityboulevard.com - Author: Avast Blog In a recent unsettling turn of events, AI-generated explicit images...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Jeffrey Burt The ransomware landscape continues to evolve, with attackers now more...
Source: securityboulevard.com - Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe,...
Source: securityboulevard.com - Author: Richi Jennings My friends all hack Porsches—I must make amends.For four months, Mercedes-Benz...
Source: securityboulevard.com - Author: Kellie Roessler Web applications offer powerful workforce efficiencies, but they are not...
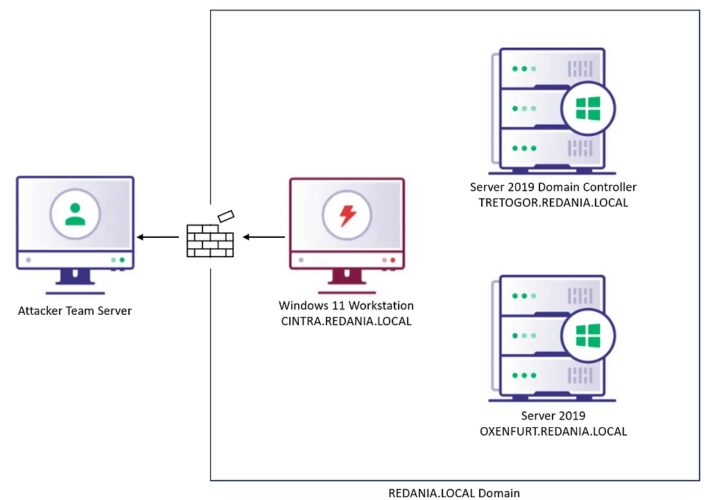
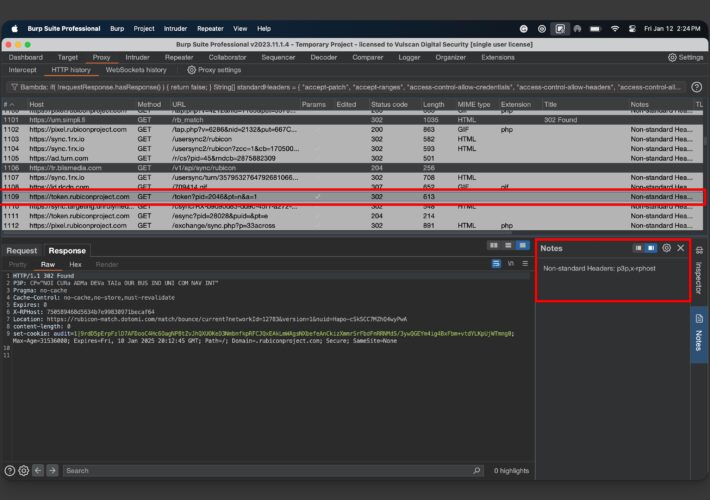
Source: securityboulevard.com - Author: Matt Creel Background If you’ve found yourself on a red team assessment...
Source: securityboulevard.com - Author: Dana Epp What if I told you that many APIs leverage custom...
Source: securityboulevard.com - Author: Impart Security Blog Today we are announcing the launch of Impart AI...
Source: securityboulevard.com - Author: Jeffrey Burt Insurance broker Keenan and Associates is notifying more than 1.5...