Source: securityboulevard.com - Author: Wajahat Raja Cybersecurity threat experts have recently discovered a new variant of...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News
Security Boulevard
Source: securityboulevard.com - Author: Nisos Nisos The Digital Services Act is Here. Nisos Can Help! As...
Source: securityboulevard.com - Author: LogRhythm Titanium stands as the information security division of Pakistan’s leading ISP...
Source: securityboulevard.com - Author: Jeffrey Burt Buried among the piles of legal documents that form WhatsApp’s...
Source: securityboulevard.com - Author: Bruce Schneier The European Court of Human Rights has ruled that breaking...
Source: securityboulevard.com - Author: Itzik Alvas. Co-founder & CEO, Entro In the face of a cyberattack,...
Source: securityboulevard.com - Author: Jeffrey Burt Google is pushing AI as the technology that will shift...
Source: securityboulevard.com - Author: Alexandra Charikova We're migrating Escape Community from Discord to Slack! After feedback...
Source: securityboulevard.com - Author: Matt Palmer Cloud security means multiple teams with a shared responsibility. The...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Lohrmann on Cybersecurity New terminology and cyber questions about generative artificial intelligence...
Source: securityboulevard.com - Author: Pierre Noujeim The quality of integrations within your SOAR (Security Orchestration, Automation,...
Source: securityboulevard.com - Author: davehull Small family farming is a labor intensive way to go broke. ...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: Dwayne McDaniel Recently, Datadog released their report on attacker techniques that they...
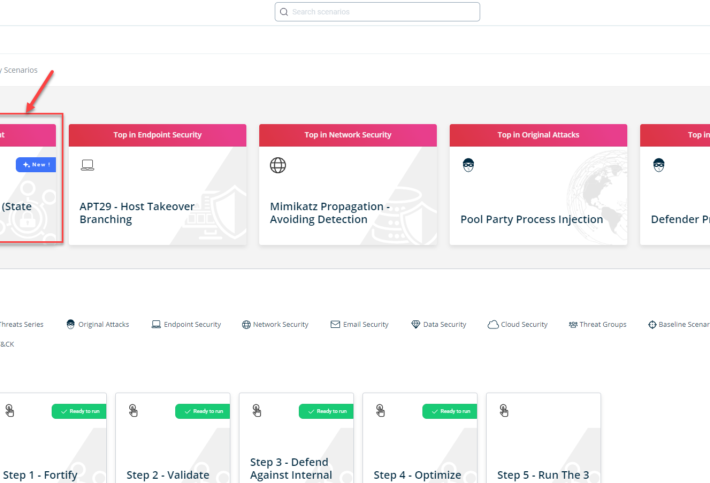
Source: securityboulevard.com - Author: Kaustubh Jagtap Author: Kaustubh Jagtap, Product Marketing Director, SafeBreach On February 15th,...
Source: securityboulevard.com - Author: Marc Handelman Security Bloggers Network Home » Security Bloggers Network » USENIX...
Source: securityboulevard.com - Author: claude.mandy This blog originally appeared here: https://drj.com/industry_news/love-in-the-age-of-ai-navigating-online-dating-scams-this-valentines-day/ With Valentine’s Day approaching, love...
Source: securityboulevard.com - Author: Kevin Smith Within just a couple years, AI seems to have overtaken...
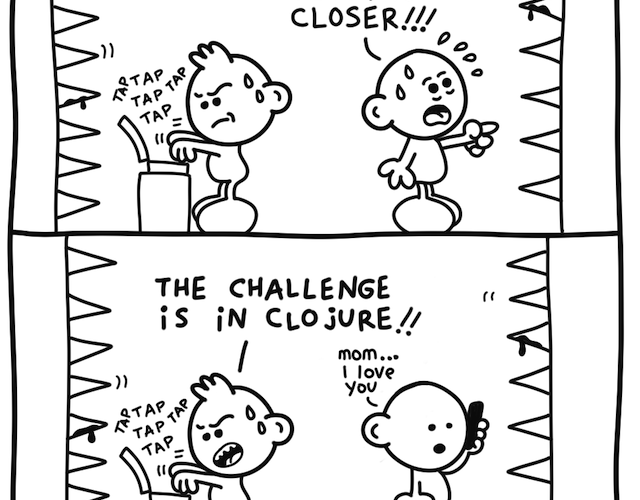
Source: securityboulevard.com - Author: Marc Handelman via the inimitable Daniel Stori at Turnoff.US. Permalink *** This...
Source: securityboulevard.com - Author: Jeffrey Burt A week after offering a $10 million reward for information...
Source: securityboulevard.com - Author: Alexandra Charikova There are more than 50 new requirements in PCI DSS v4.0 –...
Source: securityboulevard.com - Author: Team Nuspire Microsoft has released a substantial set of patches in its...
Source: securityboulevard.com - Author: Andy Robbins Entra ID has a built-in role called “Partner Tier2 Support”...
Source: securityboulevard.com - Author: Hyperproof Team As the leader of a sales organization, it’s your job...
Source: securityboulevard.com - Author: Jeffrey Burt Federal law enforcement kicked Russian state hackers off a botnet...
Source: securityboulevard.com - Author: Marc Handelman Authors/Presenters: Haiming Wang, Zhikun Zhang, Tianhao Wang, Shibo He, Michael...
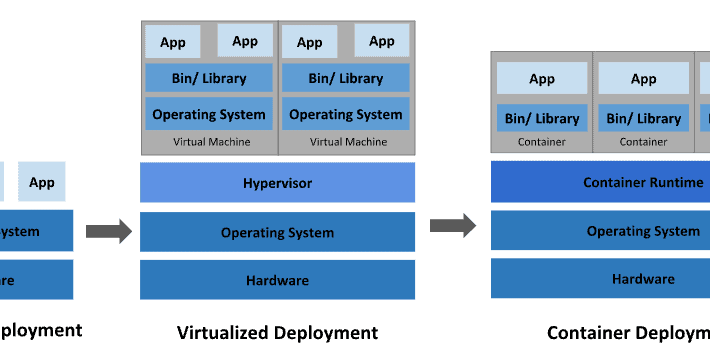
Source: securityboulevard.com - Author: Kelsey Gast In today’s fast-paced landscape of container orchestration, Kubernetes is a...
Source: securityboulevard.com - Author: Kevin Smith Malicious actors and hacker groups are actively targeting schools. According...
Source: securityboulevard.com - Author: Rezonate Identity-based attacks are on the rise, but they can be prevented...