Source: news.sophos.com – Author: gallagherseanm
Late in January 2025, a Managed Service Provider (MSP) administrator received a well-crafted phishing email containing what appeared to be an authentication alert for their ScreenConnect Remote Monitoring and Management (RMM) tool. That email resulted in Qilin ransomware actors gaining access to the administrator’s credentials—and launching ransomware attacks on the MSP’s customers.
Sophos MDR’s threat Intelligence team assesses with high confidence that this incident can be attributed to a ransomware affiliate whose activity is tracked by Sophos as STAC4365. The attack used similar infrastructure, domain naming patterns, techniques, tools, and practices to those used in other phishing campaigns Sophos MDR threat intelligence found dating back to late 2022. Those attempts leveraged phishing sites built with the evilginx open-source adversary-in-the-middle attack framework to collect credentials and session cookies and bypass multi-factor authentication (MFA).
In this case, as in others tied to this threat cluster, the attackers used fake ScreenConnect domains to act as proxies to the actual ScreenConnect login process. Once the administrator clicked on the login link on the email to review the authentication, they were redirected to a malicious phishing site, cloud.screenconnect[.]com.ms, that masqueraded as the legitimate ScreenConnect login page. Once they entered their credentials into the fake ScreenConnect site, the attackers were able to intercept those inputs. Sophos believes the fake ScreenConnect site proxied the inputs back to the legitimate ScreenConnect site to verify the credentials and capture the time-based one-time password (TOTP) sent from ScreenConnect to the administrator by email.
After intercepting the MFA inputs, the attacker successfully authenticated to the legitimate ScreenConnect Cloud portal using the administrator’s super administrator account. This granted them permission to effectively do anything inside this ScreenConnect instance and led to an attack deploying Qilin.
Background: Qilin
Qilin is a Ransomware-as-a-Service program that has been in operation since 2022, previously operating under the name “Agenda.” The Qilin group recruits affiliates on Russian-language cybercrime forums. According to Microsoft Threat Intelligence, those affiliates have grown this year to include a North Korean state actor labeled by Microsoft as “Moonstone Sleet.”
Qilin ransomware uses a data-leak site hosted on Tor to apply pressure on victims being extorted. In May of 2024, that pressure was expanded to the open internet when threat actors associated with Qilin ransomware launched a data-leak site named “WikiLeaksV2.” This project was hosted at an IP address provided by a Russian Internet service provider that has been tied to command-and-control (C2) activity, malware hosting, and phishing activities in the past. The site remains active and was linked in the ransom notes left in this incident.

Figure 2: The Qilin data-leak site hosted on Tor features a QR code and hyperlink to the WikiLeaksV2 page
Background: STAC4365
STAC4365 is associated with a pattern of activities and indicators held in common by a group of phishing sites dating back to November 2022. These sites shared characteristics such as URL path and site structure, and the domains associated with them have focused on spoofing legitimate ScreenConnect URLs.

| Domain | Earliest Activity |
| account.microsoftonline.com[.]ec | February 2025 |
| cloud.screenconnect.com[.]ms | January 2025 |
| cloud.screenconnect[.]is | November 2024 |
| cloud.screenconnect.com[.]so | October 2024 |
| cloud.screenconnect.com[.]bo | July 2024 |
| cloud.screenconnect.com[.]cm | July 2024 |
| cloud.screenconnect.com[.]am | April 2024 |
| cloud.screenconnect.com[.]ly | February 2024 |
| cloud.screenconect[.]com[.]mx | January 2024 |
| cloud.screenconnect[.]co[.]za | January 2024 |
| cloud.screenconnect[.]uk[.]com | January 2024 |
| cloud.screenconnect[.]de[.]com | November 2023 |
| cloud.screenconnect.com[.]se | October 2023 |
| cloud.screenconnect.jpn[.]com | October 2023 |
| cloud.screenconnect.com[.]ng | June 2023 |
| cloud.screenconnect.com[.]ph | May 2023 |
| cloud.screenconnect.com[.]vc | May 2023 |
| cloud.screenconnect[.]cl | April 2023 |
| cloud.screenconnect[.]gr[.]com | April 2023 |
| cloud.screenconect[.]eu | January 2023 |
| cloud.screenconnect[.]co[.]com | January 2023 |
| cloud.screenconnect[.]us[.]com | January 2023 |
| cloud.iscreenconnect[.]com | December 2022 |
| cloud.screenconnect[.]app | November 2022 |
Figure 4: A list of domains matching STAC4365’s pattern of activity
To provision these phishing sites, STAC4365 leverages evilginx, an open-source adversary-in-the-middle attack framework used for phishing credentials and session cookies and acting as an MFA relay.

Evilginx2, the latest version, includes a “javascriptRedirect” feature that threat actors use to selectively route traffic. STAC4365 leverages awstrack[.]me along with JavaScript redirects to ensure that only targeted victims, accessing the phishing site via the intended tracking link, reach the credential-harvesting page – while those visiting directly (such as researchers) are redirected to the legitimate service portal, evading detection and analysis. This feature is common in other MFA phishing platforms, as demonstrated by Rockstar and FlowerStorm.
STAC4365 Qilin attack chain
Initial access
The phishing lure specifically targeted the MSP’s administrator account, and accurately mimicked a ConnectWise ScreenConnect login alert:
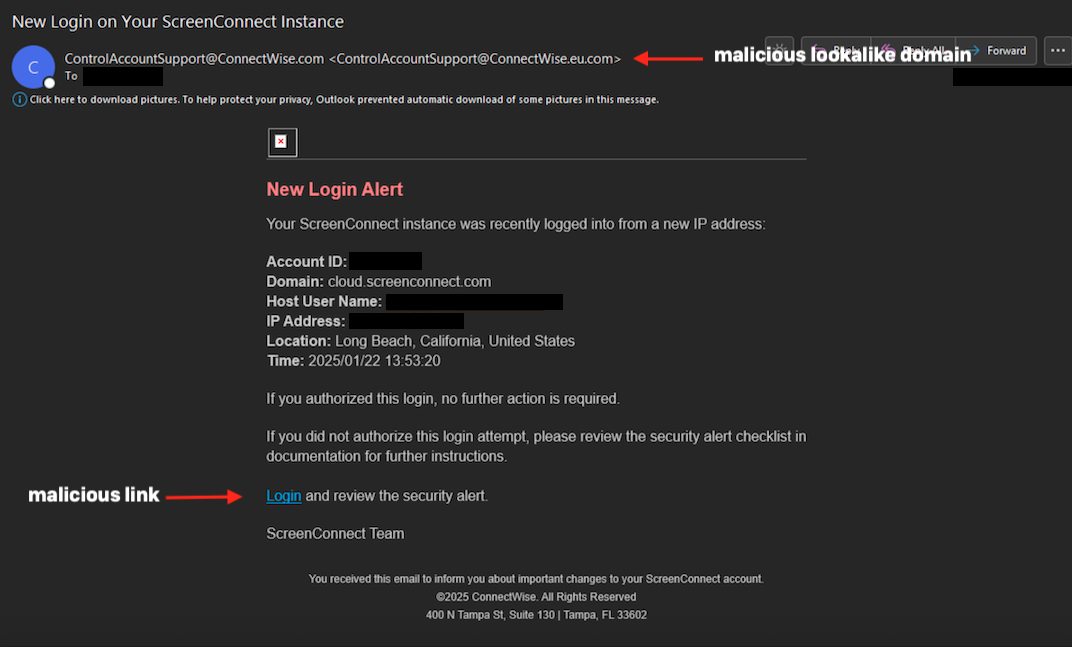
The targeted administrator clicked the “Login and review the security alert” link, which took the victim’s browser to the phishing page via a malicious redirect using Amazon Simple Email Service (SES):
hxxps[:]//b8dymnk3.r.us-east-1.awstrack[.]me/L0/https[:]%2F%2Fcloud.screenconnect[.]com.ms%2FsuKcHZYV/1/010001948f5ca748-c4d2fc4f-aa9e-40d4-afe9-bbe0036bc608-000000/mWU0NBS5qVoIVdXUd4HdKWrsBSI=410
The redirected link resolved to the URI of a ScreenConnect-mimicking domain:
hxxps[:]//cloud.screenconnect[.]com.ms/suKcHZYV/1/010001948f5ca748-c4d2fc4f-aa9e-40d4-afe9-bbe0036bc608-000000/mWU0NBS5qVoIVdXUd4HdKWrsBSI=410
This URI was used to verify the target; other visits to the domain were redirected to the legitimate cloud.screenconnect.com. The host at cloud.screenconnect[.]com.ms (186.2.163[.]10) was likely configured as a reverse proxy to the legitimate ScreenConnect domain.
Using the intercepted credentials and the MFA code, the attacker logged into the target’s ScreenConnect subdomain through the ScreenConnect Control Panel and gained access to the MSP’s remote management environment.
Persistence, Command and Control
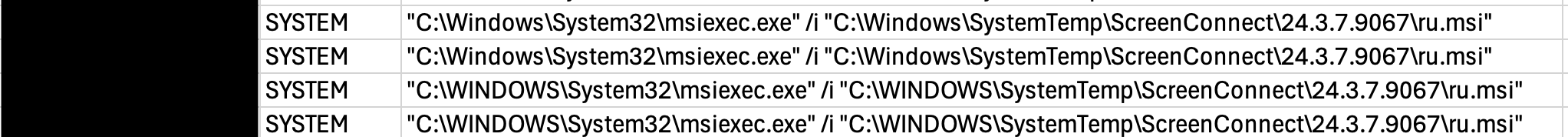
Shortly after successfully authenticating into the ScreenConnect environment as the super administrator account, the attacker pushed out a new ScreenConnect instance using a file named ‘ru.msi,’ which installed an attacker-managed ScreenConnect instance across multiple of the MSP’s managed customers.
Discovery, credential access and lateral movement
The malicious ScreenConnect instance was used in multiple customer environments to perform network enumeration and user discovery and reset numerous user account credentials. The attackers also used the ScreenConnect instance to number of legitimate tools to gain access to more local credentials and execute remote commands, as well as utilized Windows tools, including:
- PsExec
- exe (NetExec from GitHub)
- WinRM
- ScreenConnect instance
Additionally, the actors downloaded a file named “veeam.exe,” an executable coded to exploit CVE-2023-27532, a vulnerability in the Veeam Cloud Backup service which allows an unauthenticated user to request unencrypted credentials from the local Veeam configuration database. This file’s name, path location, and SHA256 hash are identical to one reported by Huntress in a 2023 cyberattack that also leveraged ScreenConnect but did not result in ransomware deployment.
Collection
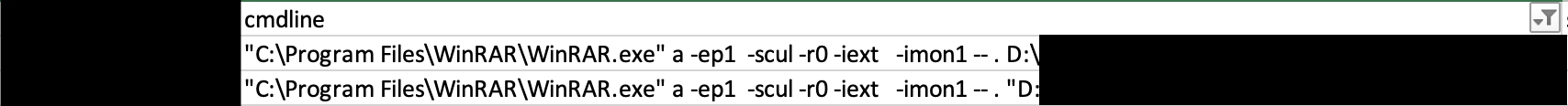
Following the discovery and lateral movement phases, the attacker began double extortion efforts by leveraging the accounts they changed credentials for, executing WinRAR to collect files across multiple customer environments.
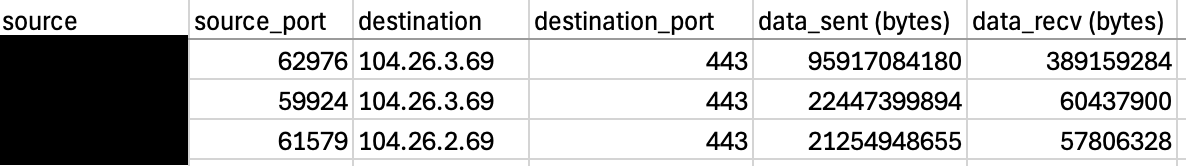
Exfiltration
Once the attackers collected data utilizing WinRAR, they exfiltrated the .rar files to easyupload.io via an Incognito tab in Google Chrome.
Defense evasion and impact
Throughout the incident, the attackers utilized various defense evasion techniques to clear their tracks. When accessing EasyUpload via Google Chrome, they utilized Incognito mode to hide forensic data. They also removed tools after execution such as WinRAR.
Using the malicious ScreenConnect instance, the attacker made sure to identify and target backups at multiple customer locations to prevent restoration of services and to better ensure their ransom demands were met. Additionally, they modified various boot options to ensure that the targeted devices would boot into Safe Mode with networking.
Finally, they leveraged the compromised accounts to deploy Qilin ransomware across multiple customers’ environments.
SophosLabs analyzed the ransomware binary retrieved by the MDR team. It contained the following functionality:
- Stop and disable Volume Shadow Copy Service (VSS) service
- Enable symbolic links
- Enumerate hosts
- Delete shadow copies
- Delete Windows Event Logs
- Set wallpaper to ransomware message
- Delete itself after execution
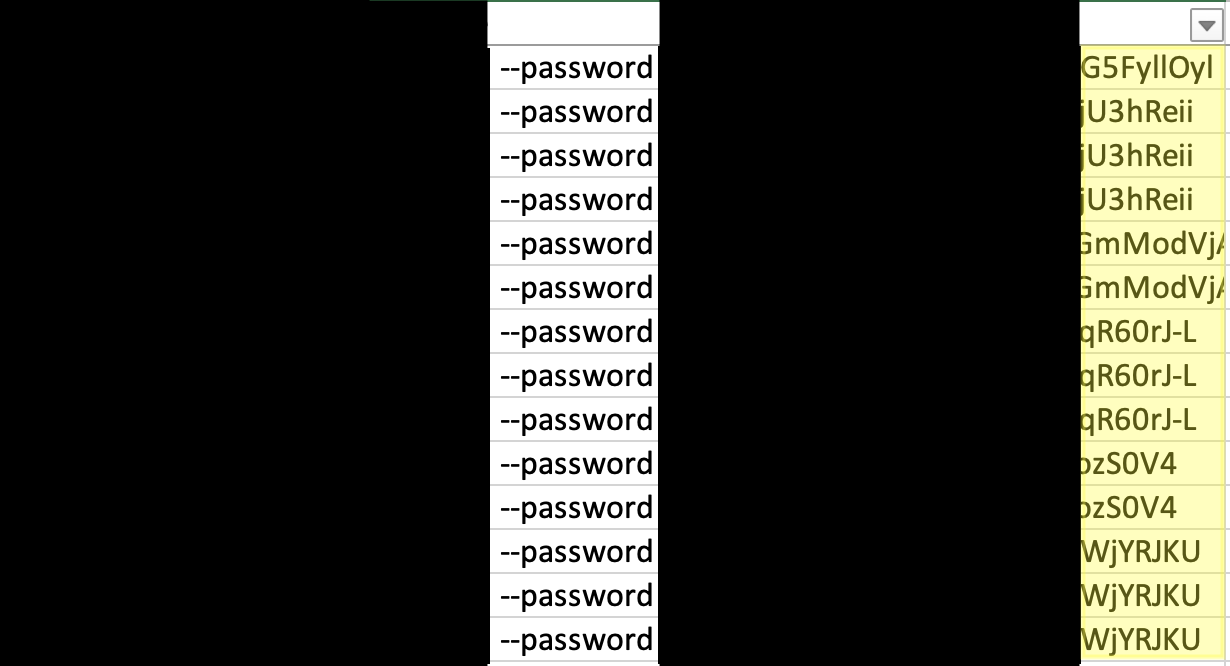
While multiple customer environments were impacted by the same ransomware binary, each customer had their own unique 32-character password associated with the execution of the ransomware binary.
Note the different end of the redacted passwords in the screenshot below:
Additionally, the readme files dropped by the ransomware had unique chat IDs for each customer, indicating that the threat actor knew they were targeting different organizations and customers.

Recommendations for defenders
MSPs rely extensively on external software and services to fulfill their operational tasks for customer organizations. Ransomware operators target these services for the same reason—they have become an increasingly common vector for downstream attacks on MSP customers. So it is important for MSPs and organizations of all sizes that utilize these services to understand the risk factors associated with them and take steps to mitigate them.
Attackers with valid administrative credentials and access are difficult to stop, particularly when it comes to the exfiltration of data. But there are measures organizations can take to prevent the initial compromise of key credentials, and to Impede execution of ransomware..
Initial access in this case was gained through targeted phishing and interception of an MFA TOTP. The attackers used a lookalike domain and a well-crafted email to get the target to click on the link. Defenders should incorporate assessments into organizational phishing training to help users spot lookalike and other suspicious domains. Additionally, ensure your email solution either flags or blocks incoming messages that fail to pass a Domain-based Message Authentication, Reporting and Conformance (DMARC) check.
The phishing attack in this case used an AITM phishing kit to relay credentials and a TOTP to obtain a valid session. When possible, organizations should limit access to corporate applications and third-party services to known managed devices through conditional access, and migrate to phishing-resistant authentication services (such as those based on FIDO 2).
In this attack, the actor configured systems to reboot in safe mode to bypass endpoint security protections. Organizations should deploy protection against safe boot restarts without endpoint protection. Sophos customers can do this by enabling active attack enhancements in Sophos Central through Endpoint and Server Threat Protection policies.
Indicators of compromise for STAC4365 and Qilin are provided on the Sophos GitHub page here.
Original Post URL: https://news.sophos.com/en-us/2025/04/01/sophos-mdr-tracks-ongoing-campaign-by-qilin-affiliates-targeting-screenconnect/
Category & Tags: Security Operations,Threat Research,adversary in the middle,MFA,MFA phishing,qilin,RMM,ScreenConnect,supply chain compromise – Security Operations,Threat Research,adversary in the middle,MFA,MFA phishing,qilin,RMM,ScreenConnect,supply chain compromise
Views: 1