Amazon has banned the sale of the Flipper Zero portable multi-tool for pen-testers as it no longer allows its sale on the platform after tagging it...
Cybercriminals ‘CAN’ Steal Your Car, Using Novel IoT Hack
Automotive security experts have uncovered a novel method for stealing cars by breaking into their control systems through a headlight. The key (so to speak) is...
Fight AI With AI
On Wednesday, KPMG Studios, the consulting giant’s incubator, launched Cranium, a startup to secure artificial intelligence (AI) applications and models. Cranium’s “end-to-end AI security and trust...
Twitter ‘Shadow Ban’ Bug Gets Official CVE
A vulnerability in Twitter’s code was recently discovered that allows users to game the algorithm with mass blocking actions from large numbers of accounts, in an...
US Space Force Requests $700M for Cybersecurity Blast Off
US Space Force top brass have requested a $700 million investment in cybersecurity as part of the military branch’s overall $30 billion 2024 budget. The Russian...
DDoS attacks rise as pro-Russia groups attack Finland, Israel
Image: Golden Sikorka/Adobe Stock The pro-Russia hacker group NoName057(16) reportedly claimed it was behind Denial of Service (DoS) attacks against the Finnish parliament’s website on Tuesday,...
Weekly Update 342
Next time I post a poll about something as simple as “when is next Friday”, I don’t expect I’ll get as much interest. Of course “next...
Phishers migrate to Telegram
Experts warn that Telegram is becoming a privileged platform for phishers that use it to automate their activities and for providing various services. Kaspersky researchers have...
OCR Labs exposes its systems, jeopardizing major banking clients
A digital identification tool provided by OCR Labs to major banks and government agencies leaked sensitive credentials, putting clients at severe risk. London-based OCR Labs is...
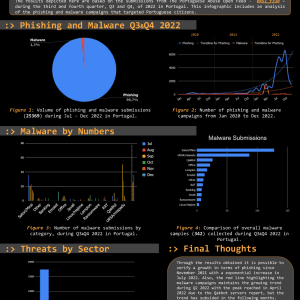
Threat Report Portugal: Q3 & Q4 2022
The Threat Report Portugal: H2 2022 compiles data collected on the malicious campaigns that occurred from July to December, H2, 2022. The Portuguese Abuse Open Feed 0xSI_f33d is...
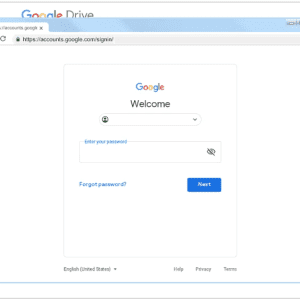
Analyzing attacks conducted by North Korea-linked ARCHIPELAGO APT group
Google’s Threat Analysis Group (TAG) warns of a North Korea-linked cyberespionage group tracked as ARCHIPELAGO. Google’s Threat Analysis Group (TAG) is warning of the North Korea-linked...
Steer clear of tax scams – Week in security with Tony Anscombe
In a rush to file your taxes? Watch out for cybercriminals preying on stressed taxpayers as Tax Day looms large on the horizon. The IRS-approved tax...
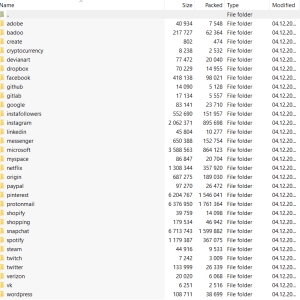
Cleaning up your social media and passwords: What to trash and what to treasure
Give your social media presence a good spring scrubbing, audit your passwords and other easy ways to bring order to your digital chaos Spring has sprung,...
Designing Your Threat Hunting Framework from Scratch – Core Essentials
A threat hunting framework is a collation of data-driven adversarial scenarios, backed up by hypothetical, field-tested, or time-honored TTPs (i.e., Tactics, Techniques, and Procedures). Serving a...
Research on AI in Adversarial Settings
New research: “Achilles Heels for AGI/ASI via Decision Theoretic Adversaries“: As progress in AI continues to advance, it is important to know how advanced systems will...
What is an ‘island hopping’ attack? (and how to stop one)
EXECUTIVE SUMMARY: At the mention of island hopping, you’re likely dreaming about adventures in Hawaii, the Caribbean, or similar destinations with majestic views and white-sand beaches....
Ukrainian hackers spend $25,000 of pro-Russian blogger’s money on sex toys
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s. View all...
A fireside chat with four CISOs about how they secure their cybersecurity firms from attack
On Tuesday 11 April, I’ll be joined by the CISOs of security firms Wiz, Rubrik, Noname, and Abnormal, for a friendly chat about how they protect...
Own a Nexx “smart” alarm or garage door opener? Get rid of it, or regret it
Nexx is a manufacturer of “smart” devices – plus, alarms, garage door openers, that kind of thing. Unfortunately their response to vulnerabilities is not-so-smart. According to...
UK criminal records office confirms cyber incident behind portal issues
The UK’s Criminal Records Office (ACRO) has finally confirmed, after weeks of delaying issuing a statement, that online portal issues experienced since January 17 resulted from...
Hackers use Rilide browser extension to bypass 2FA, steal crypto
Security researchers discovered a new malicious browser extension called Rilide, that targets Chromium-based products like Google Chrome, Brave, Opera, and Microsoft Edge. The malware is designed...
Microsoft: Windows 10 21H2 is reaching end of service in June
Microsoft reminded customers today that multiple editions of Windows 10, version 21H2, will reach the end-of-service (EOS) in two months, on June 13, 2023. This applies...
Microsoft and Fortra crack down on malicious Cobalt Strike servers
Microsoft, Fortra, and the Health Information Sharing and Analysis Center (Health-ISAC) have announced a broad legal crackdown against servers hosting cracked copies of Cobalt Strike, one...
Medusa ransomware claims attack on Open University of Cyprus
The Medusa ransomware gang has claimed a cyberattack on the Open University of Cyprus (OUC), which caused severe disruptions of the organization’s operations. OUC is an...
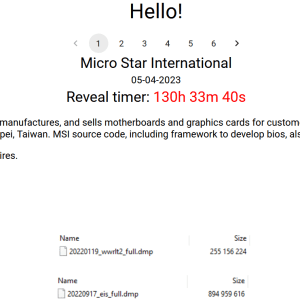
Money Message ransomware gang claims MSI breach, demands $4 million
Taiwanese PC parts maker MSI (Micro-Star International) has been listed on the extortion portal of a new ransomware gang known as “Money Message,” which claims to...
Telegram now the go-to place for selling phishing tools and services
Telegram has become the working ground for the creators of phishing bots and kits looking to market their products to a larger audience or to recruit...
‘BEC 3.0’ Is Here With Tax-Season QuickBooks Cyberattacks
Cybercriminals continue to target victims with cleverly-crafted phishing attacks, this time from QuickBooks online accounts, aimed harvesting credentials. The gambits use a level of legitimacy and social engineering...
Australia Is Scouring the Earth for Cybercriminals — the US Should Too
The constant stream of cyberattacks sweeping making headlines may seem almost inevitable by this point. And while sometimes the organizations being attacked have clearly made themselves...
It Takes AI Security to Fight AI Cyberattacks
Generative artificial intelligence technologies such as ChatGPT have brought sweeping changes to the security landscape almost overnight. Generative AI chatbots can produce clear, well-punctuated prose, images,...