Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: Data Breaches,data breach – Data Breaches,data breach UK-based photo editing, graphic design and publishing software developer Affinity...
The Security and Productivity Implications of Low Code/No Code Development – Source: www.securityweek.com – Author: Kevin Townsend –
Source: www.securityweek.com – Author: Kevin Townsend. Category & Tags: Vulnerabilities,Featured,Software,vulnerability – Vulnerabilities,Featured,Software,vulnerability The low code/no code movement provides simplified app generation – but it needs to...
ZeroFox to Acquire Threat Intelligence Firm LookingGlass for $26 Million – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: Funding/M&A,Threat Intelligence,M&A,threat intelligence – Funding/M&A,Threat Intelligence,M&A,threat intelligence ZeroFox (ZFOX), which advertises itself as an external cybersecurity solutions...
Swatting as a Service
Swatting as a Service Motherboard is reporting on AI-generated voices being used for “swatting”: In fact, Motherboard has found, this synthesized call and another against Hempstead...
LockBit Ransomware Group Developing Malware to Encrypt Files on macOS – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: Ransomware,ransomware – Ransomware,ransomware The notorious LockBit ransomware group is apparently developing a piece of malware that can...
FIN7, Former Conti Gang Members Collaborate on ‘Domino’ Malware
Former members of the Conti ransomware group are compromising systems for follow-up exploits using malware that the financially motivated FIN7 group developed; FIN7 has used the “Domino” tool in...
lockr Raises $2.5M
NEW YORK, April 17, 2023 /PRNewswire/ — lockr, the first consumer-focused platform for digital identity, consent and data, has raised $2.5M in pre-seed funding. Mozilla Ventures, Junction Venture Partners, and...
Google Issues Emergency Chrome Update for Zero-Day Bug
A Google Chrome zero-day vulnerability is under active exploit in the wild, and while details are scarce, users are urged to update their Windows, Mac, and...
NSA’s National Centers for Academic Excellent (NCAE) Cyber Games to Hold National Finals on April 22
Cyber Florida at the University of South Florida – Tampa will host the national championship round of the NCAE Cyber Games on April 22 on the...
Pen Testers Need to Hack AI, but Also Question Its Existence
Samsung has banned some uses of ChatGPT, Ford Motor and Volkswagen shuttered their self-driving car firm, and a letter calling for a pause in training more...
How CISOs Can Craft Better Narratives for the Board
For at least a decade now, career-minded security leaders have well understood the importance of effective communication with the board and CEO. CISOs know they must...
Aloha PoS Restaurant Software Downed by Ransomware Attack
After days of outages, NCR Corp. has confirmed that its Aloha point-of-sale (PoS) software platform, used by thousands of restaurants across the US, was taken down...
Ex-Conti members and FIN7 devs team up to push new Domino malware
Ex-Conti ransomware members have teamed up with the FIN7 threat actors to distribute a new malware family named ‘Domino’ in attacks on corporate networks. Domino is...
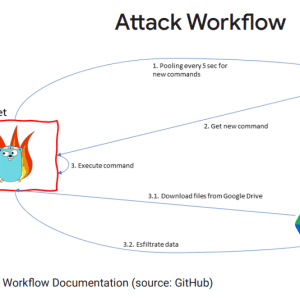
Hackers abuse Google Command and Control red team tool in attacks
The Chinese state-sponsored hacking group APT41 was found abusing the GC2 (Google Command and Control) red teaming tool in data theft attacks against a Taiwanese media...
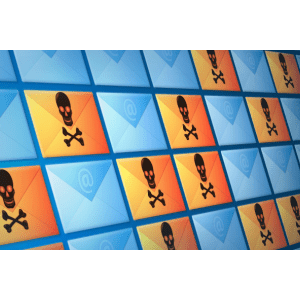
New QBot email attacks use PDF and WSF combo to install malware
QBot malware is now distributed in phishing campaigns utilizing PDFs and Windows Script Files (WSF) to infect Windows devices. Qbot (aka QakBot) is a former banking...
New Chameleon Android malware mimics bank, govt, and crypto apps
A new Android trojan called ‘Chameleon’ has been targeting users in Australia and Poland since the start of the year, mimicking the CoinSpot cryptocurrency exchange, an...
Telegram – How a Messenger Turned into a Cybercrime Ecosystem by 2023 by Kela Cybercrime Intelligence
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Montana Becomes First US State to Pass TikTok Ban
The state of Montana in the US has become the first to pass legislation banning TikTok on personal devices. The bill, SB 419, passed by a vote...
Ransomware Attack Hits Payments Giant NCR’s Datacenter
US payments giant NCR has been hit by a ransomware attack that targeted one of its data centers in Aloha, Hawaii. The company unveiled the breach...
Qbot Banking Trojan Increasingly Delivered Via Business Emails
A malicious spam-email campaign has been observed increasingly spreading banking Trojans from the QBot (or Qakbot) family using fake business emails. Discovered by security researchers at...
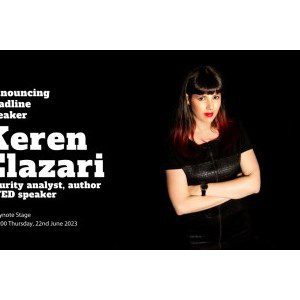
Friendly Hacker, Keren Elazari, to Announced as Keynote Speaker at Infosecurity Europe 2023
Acclaimed security analyst, author and TED speaker, Keren Elazari, has today been announced as the latest keynote speaker at Infosecurity Europe, the most influential information security event running...
The State of Cloud Native Security Report 2023 by Paloalto Networks
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
How to Protect Your Ecommerce Site from Cybersecurity Threats
By Karl Pulanco, Product Portfolio Manager, Yondu Modern businesses no longer need a physical store to sell goods and services. All they need now is an...
China-linked APT41 group spotted using open-source red teaming tool GC2 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. China-linked APT41 group used the open-source red teaming tool GC2 in an attack against a Taiwanese media organization. Google Threat...
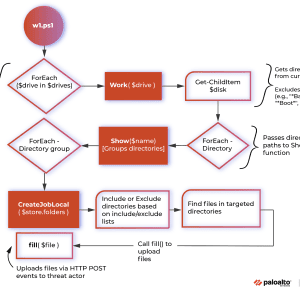
Vice Society gang is using a custom PowerShell tool for data exfiltration – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Vice Society ransomware operators have been spotted using a PowerShell tool to exfiltrate data from compromised networks. Palo Alto Unit...
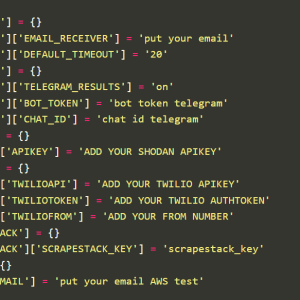
Experts warn of an emerging Python-based credential harvester named Legion – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Legion is an emerging Python-based credential harvester and hacking tool that allows operators to break into various online services. Cado...
Experts found the first LockBit encryptor that targets macOS systems – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Researchers warn that the LockBit ransomware gang has developed encryptors to target macOS devices. The LockBit group is the first...
LockBit Ransomware Tests Taking a Bite Out of Apple Users – Source: www.databreachtoday.com – Author: 1.
Source: www.databreachtoday.com – Author: 1. Cybercrime , Cybercrime as-a-service , Endpoint Security Don’t Panic: Apparent macOS Beta Testing is Highly Buggy, Poses No Immediate Threat Mathew...
GUEST ESSAY: The Top 10 cybersecurity shortfalls that put SMBs, enterprises at elevated risk
By Harman Singh No organization is immune to cybersecurity threats. Even the most well-protected companies can be susceptible to attacks if they are not careful about...
Payments Giant NCR Hit by Ransomware – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: Ransomware,Featured,ransomware – Ransomware,Featured,ransomware US payments giant NCR confirmed over the weekend that a data center outage is...