As recently as 2021, the notorious Russian APT28 was exploiting network routers running outdated versions of Cisco’s IOS and IOS XE operating system software, using them...
7 Sizzling Sessions to Check Out at RSA Conference 2023
Keep up with the latest cybersecurity threats, newly-discovered vulnerabilities, data breach information, and emerging trends. Delivered daily or weekly right to your email inbox. Subscribe Views:...
Coro Raises an Additional $75M Bringing the Total Raised to $155M in 12 Months
NEW YORK–(BUSINESS WIRE) — Coro, the modern cybersecurity platform for mid-market organizations, today announced a $75M funding round, bringing the total funding raised in the last...
Gary Bowser, Former Nintendo Hacker, Released From Prison
Gary Bowser, who was indicted in 2020 and sentenced in 2021 to 40 months in prison for being a part of a hacking ring known as Team...
Popular Fitness Apps Leak Location Data Even When Users Set Privacy Zones
Fitness apps such as Strava leak sensitive location information of users, even when they’ve used in-app features to specifically set up privacy zones to hide their...
OT Zero Trust
The Last Frontier to Protect OT Environments By Terence Liu, CEO, TXOne Networks OT Zero Trust – a Device-Centric Methodology In the IT world, the heart...
3 Flaws, 1 War Dominated Cyber-Threat Landscape in 2022
Popular attacks for a trio of critical vulnerabilities kept exploitation at the top of the list of initial-access methods in 2022, while the war between Russia...
Akamai Technologies to Acquire API Security Company Neosec
CAMBRIDGE, Mass., April 19, 2023 /PRNewswire/ — Akamai Technologies, Inc. (NASDAQ: AKAM), the cloud company that powers and protects life online, today announces that it has entered into a...
How to Prevent 2 Common Attacks on MFA
It’s a well-known and statistically proven fact that password-only credentials pose the highest cyber-risk to people and organizations. Passwords are easily compromised through a wide variety...
Smashing Security podcast #318: Tesla workers spy on drivers, and Operation Fox Hunt scams
Graham wonders what would happen if his bouncing buttocks were captured on camera by a Tesla employee, and we take a look at canny scams connected...
Join my Twitter Subscription for the Inside Word on Data Breaches – Source: www.troyhunt.com
Source: www.troyhunt.com – Author: Troy Hunt I want to try something new here – bear with me here: Data breach processing is hard and the hardest...
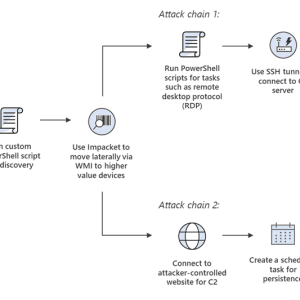
Iranian Nation-State Actor “Mint Sandstorm” Weaponizes N-day Flaws
A threat actor associated with Iranian nation-state hackers has been weaponizing N-day vulnerabilities, as well as deploying new techniques to access environments of interest. The threat...
#CYBERUK23: Threat Posed by ‘Irresponsible’ Use of Commercial Hacking Tools Increasing, NCSC Warns
Spyware, hackers for hire and access to other cyber capabilities such as hacking-as-a-service kits are expected to be in growing demand globally, the UK’s National Cyber...
Raspberry Robin Adopts Unique Evasion Techniques
Threat actors relying on the Raspberry Robin malware have been observed adopting unique evasion techniques to avoid detection. Security researchers at Check Point Research (CPR) published...
Nurse Call Systems, Infusion Pumps Riskiest Connected Medical Devices
Nurse call systems and infusion pumps have been found to be the riskiest connected medical devices, suggests a new report by asset visibility and security company...
US Company CommScope Hit by Ransomware
Following a ransomware attack back in March, sensitive employee data was compromised at CommScope, a major US telecommunications and IT infrastructure company. The Vice Society ransom gang...
APT28 Russian Hackers Inject Routers with Jaguar Tooth Custom Malware
Researchers in US and UK warn that Russian state sponsored APT28 hackers deploy ”Jaguar Tooth” custom malware on routers in order to obtain unauthorized access. The...
Discarded, not destroyed: Old routers reveal corporate secrets – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Cameron Camp. When decommissioning their old hardware, many companies ‘throw the baby out with the bathwater’ Taking a defunct router out of...
US and UK agencies warn of Russia-linked APT28 exploiting Cisco router flaws – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. UK and US agencies are warning of Russia-linked APT28 group exploiting vulnerabilities in Cisco networking equipment. Russia-linked APT28 group accesses unpatched Cisco...
Iran-linked Mint Sandstorm APT targeted US critical infrastructure – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. An Iran-linked APT group tracked as Mint Sandstorm is behind a string of attacks aimed at US critical infrastructure between late 2021...
PWNYOURHOME, FINDMYPWN, LATENTIMAGE: 3 iOS Zero-Click exploits used by NSO Group in 2022 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Citizen Lab reported that Israeli surveillance firm NSO Group used at least three iOS zero-click exploits in 2022. A new...
Experts temporarily disrupted the RedLine Stealer operations – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Security experts from ESET, have temporarily disrupted the operations of the RedLine Stealer with the help of GitHub. ESET researchers...
Hackers actively exploit critical RCE bug in PaperCut servers
Print management software developer PaperCut is warning customers to update their software immediately, as hackers are actively exploiting flaws to gain access to vulnerable servers. PaperCut...
Google patches another actively exploited Chrome zero-day
Google has released a security update for the Chrome web browser to fix the second zero-day vulnerability found to be exploited in attacks this year. “Google...
Play ransomware gang uses custom Shadow Volume Copy data-theft tool
The Play ransomware group has developed two custom tools in .NET, namely Grixba and VSS Copying Tool, which it uses to improve the effectiveness of its...
March 2023 broke ransomware attack records with 459 incidents
March 2023 was the most prolific month recorded by cybersecurity analysts in recent years, measuring 459 attacks, an increase of 91% from the previous month and...
Google Search outage prevents some from seeing search results
Update 4/18/23: The outage appears to be resolved, with fewer people reporting issues. Google Search is currently suffering a partial outage that prevents the search engine...
US, UK warn of govt hackers using custom malware on Cisco routers
The US, UK, and Cisco are warning of Russian state-sponsored APT28 hackers deploying a custom malware named ‘Jaguar Tooth’ on Cisco IOS routers, allowing unauthenticated access...
ANZ Webinar | What You Don’t Know Can Hurt You: Open Source License Compliance and M&A Activity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Sam Quakenbush Senior Director – Field Innovation & Strategy, Mend Sam Quakenbush has spent the past 10 years working for cyber...
Why FDA’s New Cyber Device Regs Are a ‘Watershed Moment’ – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Endpoint Security , Events , Healthcare Kevin Fu of Northeastern University on How the Regulations Will Ensure Uniformity Marianne Kolbasuk McGee...