Source: www.govinfosecurity.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
CommonSpirit Ups Cost Estimate on Its 2022 Ransomware Breach – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyber Insurance , Fraud Management & Cybercrime , Governance & Risk Management Company Executive Hopes Insurance Will Help Cover Most Costs...
GoldenJackal APT Targeting South Asian Government Agencies – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Threat Actor Shares Limited Code Similarity With Turla Jayant Chakravarti (@JayJay_Tech) •...
Barracuda Email Security Gateway (ESG) hacked via zero-day bug – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Barracuda warned customers that some of its Email Security Gateway (ESG) appliances were breached exploiting a zero-day vulnerability. Network security...
The US government sanctioned four entities and one individual for supporting cyber operations conducted by North Korea – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The US Department of the Treasury sanctioned four entities and one individual for their role in cyber operations conducted by...
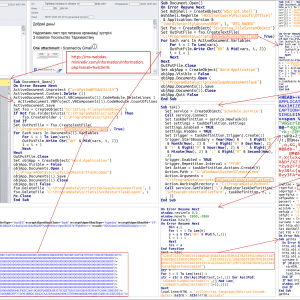
Ukraine’s CERT-UA warns of espionage activity conducted by UAC-0063 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The Computer Emergency Response Team of Ukraine (CERT-UA) warns of a cyberespionage campaign targeting state bodies in the country. The...
AhRat Android RAT was concealed in iRecorder app in Google Play – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini ESET found a new remote access trojan (RAT), dubbed AhRat, on the Google Play Store that was concealed in an...
Hackers target 1.5M WordPress sites with cookie consent plugin exploit – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Ongoing attacks are targeting an Unauthenticated Stored Cross-Site Scripting (XSS) vulnerability in a WordPress cookie consent plugin named Beautiful Cookie...
Chinese hackers breach US critical infrastructure in stealthy attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft says a Chinese cyberespionage group it tracks as Volt Typhoon has been targeting critical infrastructure organizations across the United...
GitLab ‘strongly recommends’ patching max severity flaw ASAP – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas GitLab has released an emergency security update, version 16.0.1, to address a maximum severity (CVSS v3.1 score: 10.0) path traversal...
New PowerExchange malware backdoors Microsoft Exchange servers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan A new PowerShell-based malware dubbed PowerExchange was used in attacks linked to APT34 Iranian state hackers to backdoor on-premise Microsoft...
Windows 11 Moment 3 released with KB5026446 update, how to enable – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft has released the Windows 11 22H2 KB5026446 update, aka ‘Moment 3,’ bringing quite a few new and long-awaited features...
Windows 10 KB5026435 update released with 2 new features, 18 fixes – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft has released the optional KB5026435 Preview cumulative update for Windows 10 22H2 with two new features and 18 additional...
Iranian hackers use new Moneybird ransomware to attack Israeli orgs – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Image: Bing Create A suspected Iranian state-supported threat actor known as ‘Agrius’ is now deploying a new ransomware strain named...
Barracuda warns of email gateways breached via zero-day flaw – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Barracuda, a company known for its email and network security solutions, warned customers today that some of their Email Security...
‘Volt Typhoon’ China-Backed APT Infiltrates US Critical Infrastructure Orgs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading China-sponsored threat actors have managed to establish persistent access within telecom networks and other critical...
Honeywell Releases Cyber Insights to Better Identify Cybersecurity Threats and Vulnerabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 ATLANTA, May 23, 2023 – Honeywell (Nasdaq: HON) today announced the release of its operational technology (OT) cybersecurity solution, Honeywell Forge...
Harvard Pilgrim Health Care Notifies Individuals of Privacy Incident – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 CANTON, Mass., May 23, 2023 /PRNewswire/ — On April 17, 2023, Point32Health, the parent organization of Harvard Pilgrim Health Care (“Harvard Pilgrim“) and Tufts...
Technology Veterans James Wickett and Ken Johnson Launch DryRun Security to Bring Security to Developers – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Austin Texas, May 23, 2023 – DryRun Security emerged from stealth with the mission to fix the disconnect between security and...
Appdome Launches Build-to-Test, Automated Testing Option for Protected Mobile Apps – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 REDWOOD CITY, Calif., May 23, 2023 /PRNewswire/ — Appdome, the mobile app economy’s one and only Cyber Defense Automation platform, today announced Build-to-Test which...
Netwrix Report: Enterprises Suffer More Ransomware and Other Malware Attacks Than Smaller Organizations – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 FRISCO, Texas, May 23, 2023 /PRNewswire/ — Netwrix, a cybersecurity vendor that makes data security easy, today announced additional findings for the enterprise sector (organizations...
Threat Actors Compromise Barracuda Email Security Appliances – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Email and network security solutions company Barracuda Networks is warning customers that threat actors have targeted its email security...
Google’s .zip, .mov Domains Give Social Engineers a Shiny New Tool – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading Two new top-level domain names — .zip and .mov — have caused concern among security researchers,...
OAuth Flaw in Expo Platform Affects Hundreds of Third-Party Sites, Apps – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A vulnerability in the implementation of the Open Authorization (OAuth) standard that websites and applications use to...
How Universities Can Bridge Cybersecurity’s Gender Gap – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dr. Ashley Podhradsky, Vice President for Research and Economic Development, Dakota State University The United States faces a tremendous shortage of cybersecurity...
Indiana, Iowa, and Tennessee Pass Comprehensive Privacy Laws – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Indiana, Iowa, and Tennessee Pass Comprehensive Privacy Laws It’s been a big month for US data privacy. Indiana, Iowa,...
SMBs and regional MSPs are increasingly targeted by state-sponsored APT groups – Source: www.csoonline.com
Source: www.csoonline.com – Author: Research shows a shift toward advanced persistent threat actors compromising smaller organization, in part to enable other attacks. Advanced persistent threat (APT)...
New hyperactive phishing campaign uses SuperMailer templates: Report – Source: www.csoonline.com
Source: www.csoonline.com – Author: Network security firm Cofense was able to identify a code trace in phishing emails that revealed SuperMailer abuse in the attacks. Thinkstock...
US sanctions four North Korean entities for global cyberattacks – Source: www.csoonline.com
Source: www.csoonline.com – Author: North Korean hackers stole more virtual currency in 2022 than in any previous year, with estimates ranging from $630 million to over...
CyberArk’s enterprise browser promises zero-trust support, policy management – Source: www.csoonline.com
Source: www.csoonline.com – Author: The identity security vendor is set to launch an enterprise browser in response to increasing post-MFA attacks on session cookies. By Samira...