Source: www.theguardian.com – Author: Henry Belot Sensitive and personal government information has been stolen from law firm HWL Ebsworth by a Russian ransomware gang and posted...
Japan’s largest port stops operations after ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Port of Nagoya, the largest and busiest port in Japan, has been targeted in a ransomware attack that currently...
Hackers Steal and Sell Victims’ Bandwidth Using ProxyHacking – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Cybercrime as-a-service , Endpoint Security Attackers List Compromised Servers on Bandwidth Sharing Platforms for Profit Akshaya Asokan (asokan_akshaya) •...
Banking Tech Forecast: Cloudy, With a Chance of Cyber Risk – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Cloud Security , Governance & Risk Management Cloud Adoption in Financial Services has Soared – as...
Secrets, Secrets Are No Fun. Secrets, Secrets (Stored in Plain Text Files) Hurt Someone – Source:thehackernews.com
Source: thehackernews.com – Author: . Secrets are meant to be hidden or, at the very least, only known to a specific and limited set of individuals...
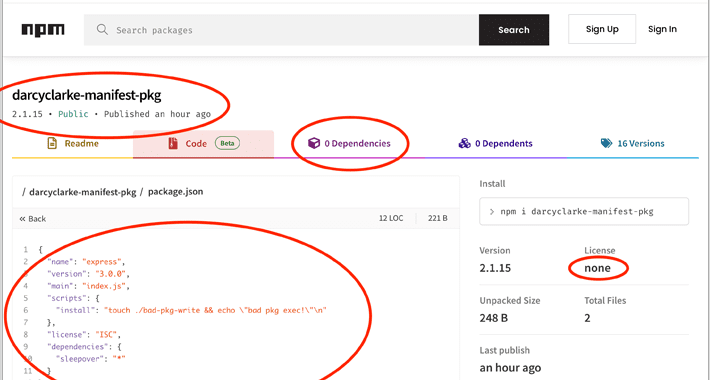
Node.js Users Beware: Manifest Confusion Attack Opens Door to Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 05, 2023Ravie LakshmananSupply Chain / Software Security The npm registry for the Node.js JavaScript runtime environment is susceptible to what’s...
Instagram’s Twitter Alternative ‘Threads’ Launch Halted in Europe Over Privacy Concerns – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 05, 2023Ravie LakshmananPrivacy / Social Media Instagram Threads, the upcoming Twitter competitor from Meta, will not be launched in the...
Hackers Steal and Sell Victims’ Bandwidth Using ProxyHacking – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Cybercrime as-a-service , Endpoint Security Attackers List Compromised Servers on Bandwidth Sharing Platforms for Profit Akshaya Asokan (asokan_akshaya) •...
Banking Tech Forecast: Cloudy, With a Chance of Cyber Risk – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Cloud Security , Governance & Risk Management Cloud Adoption in Financial Services has Soared – as...
CISA Warning! 8 Actively Exploited Flaws in Samsung and D-Link Devices – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși The US Cybersecurity and Infrastructure Security Agency (CISA) added 6 flaws affecting Samsung smartphones to its Known Exploited Vulnerabilities Catalog....
Charming Kitten’s POWERSTAR Malware Boosts its Techniques – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici Cybersecurity researchers recently published an advisory on the evolution of POWERSTAR backdoor malware and advanced spear-phishing techniques used by Charming...
HHS Data at Risk After MOVEit Hack Impacted Third-Party Vendors – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici A third-party security breach at the Department of Health and Human Services (HHS) may have exposed the personal information of...
Report Reveals Companies Unprepared For Darknet Data Leaks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A new report by the Kaspersky Digital Footprint Intelligence team has revealed that several companies worldwide are severely unprepared when dealing...
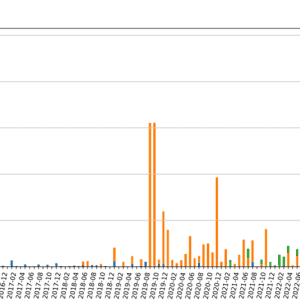
Over Two-Thirds of FortiGate Firewalls Still at Risk – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Approximately 69% of FortiGate firewalls affected by a recently discovered FortiOS vulnerability remain unpatched, according to security researchers at Bishop Fox....
Mexican Hacker Unleashes Android Malware on Global Banks – Source: www.infosecurity-magazine.com
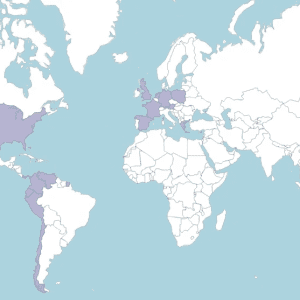
Source: www.infosecurity-magazine.com – Author: 1 Security researcher Pol Thill has identified a Mexico-based hacker known as Neo_Net as the mastermind behind a series of cyber-attacks targeting...
Swedish Data Protection Authority Warns Companies Against Google Analytics Use – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 04, 2023Ravie LakshmananPrivacy / Online Security The Swedish data protection watchdog has warned companies against using Google Analytics due to...
MOVEit attack on Aon exposed data of the staff at the Dublin Airport – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Personal data of the personnel at the Dublin Airport was compromised due to a MOVEit attack on professional service provider...
Neo_Net runs eCrime campaign targeting clients of banks globally – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A Mexican threat actor that goes online with the moniker Neo_Net is behind an Android malware campaign targeting banks worldwide....
Hackers stole millions of dollars worth of crypto assets from Poly Network platform – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Poly Network platform suspended its services during the weekend due to a cyber attack that resulted in the theft of...
335,923 out of 489,337 Fortinet firewalls vulnerable to CVE-2023-27997 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers reported that there are 490,000 Fortinet firewalls exposing SSL VPN interfaces on the internet, and roughly 69% of them...
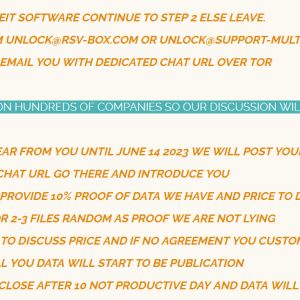
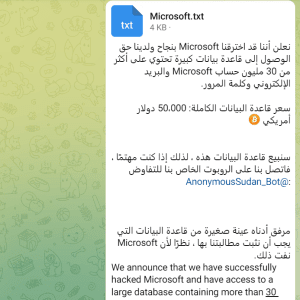
Anonymous Sudan claims to have stolen 30 million Microsoft’s customer accounts – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Microsoft denied the data breach after the collective of hacktivists known as Anonymous Sudan claimed to have hacked the company....
Understanding the Top Changes in PCI DSS 4.0 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Merton Notrem, Compliance Success Manager, Scytale We get it – just when you’ve cracked down the gist of PCI DSS version 3.2.1,...
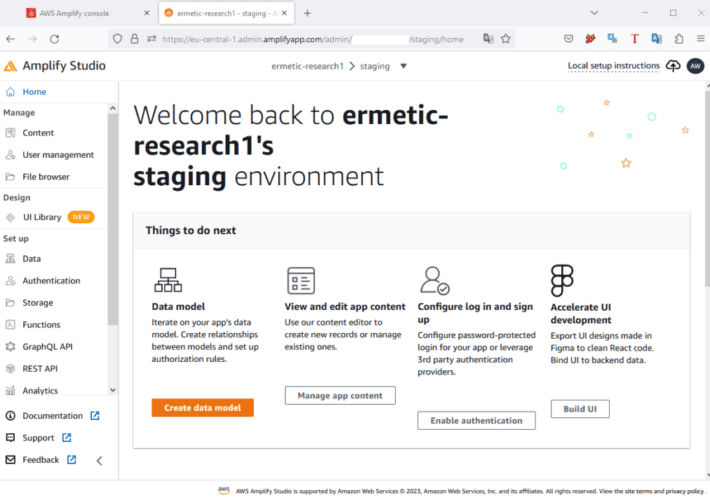
Sometimes What Sounds Benign Can Bite You: An Unexpected Implication of Lambda Privileges – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ermetic Team Ermetic researchers recently discovered a specific combination of AWS service usage and permissions that may result in unexpected behavior. The...
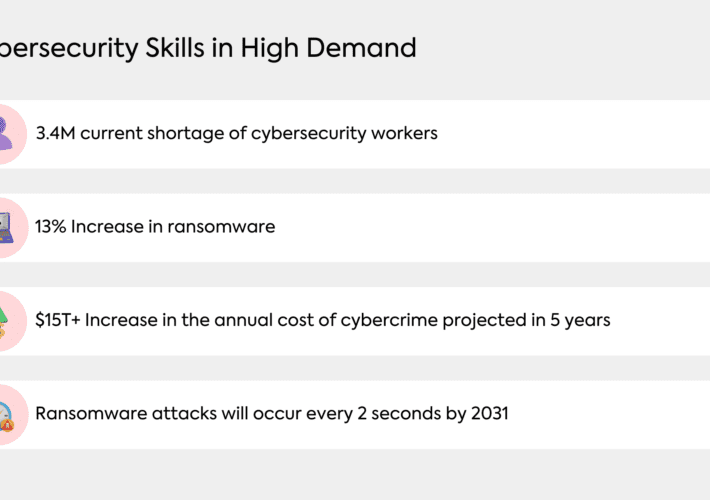
How Organizations can Thrive Despite the Cybersecurity Skill Shortage – Source: securityboulevard.com
Source: securityboulevard.com – Author: Khushboo Chahal Introduction Organizations across industries face a common challenge – the Cybersecurity Skill Shortage. IBM Data Breach Report revealed that an...
United States of America, Independence Day 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
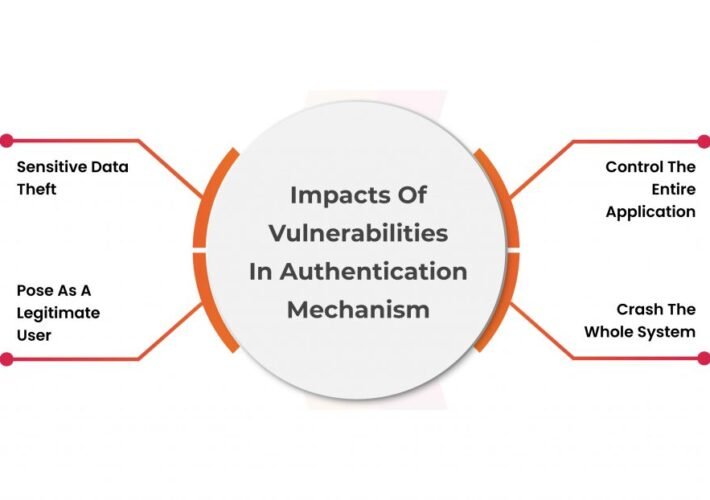
Bypass Vulnerability in WordPress Plugins Authentication – Source: securityboulevard.com
Source: securityboulevard.com – Author: Riddika Grover Authentication bypass vulnerability is a security defect that enables a threat actor to circumvent or bypass the authentication process of...
Looking ahead of CEA guidelines to secure the power sector in India – Source: securityboulevard.com
Source: securityboulevard.com – Author: Prayukth K V Looking ahead of CEA guidelines to secure the power sector in India – Sectrio India’s Central Electricity Authority (CEA)...
Verifiable Credentials: Revolutionizing Digital Identity Verification – Source: securityboulevard.com
Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author The digital age has transformed numerous aspects of everyday life, from shopping and banking to...
Is It Safe To Text Social Security Numbers? 10 SSN Safety Tips – Source: securityboulevard.com
Source: securityboulevard.com – Author: ReasonLabs Your social security number (SSN) is one of the most crucial pieces of personal information you possess. It serves as a...
What is a Data Protection Strategy? Components, Best Practices and Benefits – Source: securityboulevard.com
Source: securityboulevard.com – Author: Spanning Cloud Apps Due to the increased shift to a hybrid business model in recent times, the world is witnessing an unprecedented surge...