Source: thehackernews.com – Author: . Jul 18, 2023THNMalware / Cyber Attack An unidentified threat actor compromised an application used by multiple entities in Pakistan to deliver...
VirusTotal Data Leak Exposes Some Registered Customers’ Details – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 18, 2023THNPrivacy / Malware Data associated with a subset of registered customers of VirusTotal, including their names and email addresses,...
Go Beyond the Headlines for Deeper Dives into the Cybercriminal Underground – Source:thehackernews.com
Source: thehackernews.com – Author: . Discover stories about threat actors’ latest tactics, techniques, and procedures from Cybersixgill’s threat experts each month. Each story brings you details...
FIN8 Group Using Modified Sardonic Backdoor for BlackCat Ransomware Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 18, 2023THNRansomware / Cyber Threat The financially motivated threat actor known as FIN8 has been observed using a “revamped” version...
Owner of BreachForums Pleads Guilty to Cybercrime and Child Pornography Charges – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 18, 2023THNCybercrime / Data Breach Conor Brian Fitzpatrick, the owner of the now-defunct BreachForums website, has pleaded guilty to charges...
Cybercriminals Exploiting WooCommerce Payments Plugin Flaw to Hijack Websites – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 18, 2023THNServer Security / Vulnerability Threat actors are actively exploiting a recently disclosed critical security flaw in the WooCommerce Payments...
JumpCloud Blames ‘Sophisticated Nation-State’ Actor for Security Breach – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 18, 2023THNData Security / Cyber Attack A little over a week after JumpCloud reset API keys of customers impacted by...
Hackers Exploit WebAPK to Deceive Android Users into Installing Malicious Apps – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 17, 2023THNMobile Security / Malware Threat actors are taking advantage of Android’s WebAPK technology to trick unsuspecting users into installing...
These 6 Questions Will Help You Choose the Best Attack Surface Management Platform – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 17, 2023The Hacker NewsAttack Surface Management The hype around different security categories can make it difficult to discern features and...
Malicious USB Drives Targetinging Global Targets with SOGU and SNOWYDRIVE Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 17, 2023THNEndpoint Security / Cyber Attack Cyber attacks using infected USB infection drives as an initial access vector have witnessed...
Cybercriminals Exploit Microsoft Word Vulnerabilities to Deploy LokiBot Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 17, 2023THNMalware / Cyber Threat Microsoft Word documents exploiting known remote code execution flaws are being used as phishing lures...
CERT-UA Uncovers Gamaredon’s Rapid Data Exfiltration Tactics Following Initial Compromise – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 17, 2023THNCyber Attack / Data Safety The Russia-linked threat actor known as Gamaredon has been observed conducting data exfiltration activities...
WormGPT: New AI Tool Allows Cybercriminals to Launch Sophisticated Cyber Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 15, 2023THNArtificial Intelligence / Cyber Crime With generative artificial intelligence (AI) becoming all the rage these days, it’s perhaps not...
Microsoft Bug Allowed Hackers to Breach Over Two Dozen Organizations via Forged Azure AD Tokens – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 15, 2023THNCyber Attack / Enterprise Security Microsoft on Friday said a validation error in its source code allowed for Azure...
Critical Security Flaws Uncovered in Honeywell Experion DCS and QuickBlox Services – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 14, 2023THNVulnerability/ Cyber Threat Multiple security vulnerabilities have been discovered in various services, including Honeywell Experion distributed control system (DCS)...
Rogue IT security worker who impersonated ransomware gang is sentenced to jail – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley A British IT worker who exploited a ransomware attack against the company he worked for, in an attempt to extort...
Ransomware Crypto Payments Poised to Set New Record in 2023 – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cryptocurrency Fraud , Fraud Management & Cybercrime , Ransomware Crypto Cybercrime Falls 65% Overall, But Ransomware Projected to Hit $899M Rashmi...
Leveraging Usage-Based Licensing – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Application Security , Application Security & Online Fraud , DevSecOps How to Enable Digital Acceleration Success Vince Hwang, Senior Director, Products...
Russia to Ban iPhone Use by Government Employees – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government Russia Says Restrictions Needed to Defend Against US Spying With...
Security Awareness Matters: How to Build Awareness that Transforms Culture and Reduces Risk – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Theo Zafirakos CISO, Professional Services Lead, Fortra’s Terranova Security Theo is an experienced CISO, trusted cyber security advisor, and expert in...
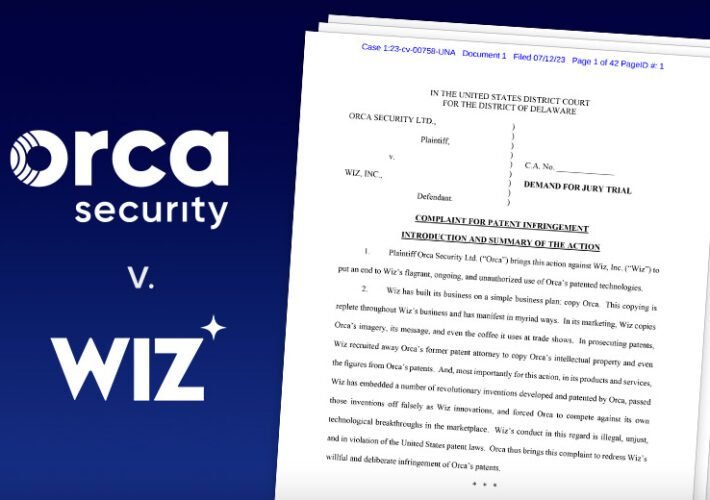
Orca Security Sues Wiz for Allegedly Violating 2 Patents – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Security , Security Operations Wiz Says ‘Baseless Accusations’ Follow Orca’s Failed Attempts to Compete With Wiz Michael Novinson (MichaelNovinson) •...
China-Based Hacker Hijacked EU, US Government Emails – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Email Security & Protection , Fraud Management & Cybercrime 26 Countries Hit by Espionage Group Storm-0558...
AI in the OT/IoT environment: Deus ex machina – the good, bad & ugly – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Antoinette Hodes is a Global Solutions Architect, specializing in IoT, and serves as an Evangelist with the Check Point Office of...
News Alert: Oxeye provides remediation guidance for ‘Owncast’ and ‘EaseProbe’ vulnerabilities – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Tel Aviv, Israel– July 12, 2023 – Oxeye, the provider of an award-winning cloud-native application security platform, has uncovered two critical...
News Alert: AcuityTec welcomes Alfredo Solis as their new Senior Director and Business Strategist – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Montreal, Canada, July 11, 2023 — AcuityTec, a leading provider of Global KYC, KYT, compliance, and multi-layered fraud prevention solutions, is...
News Alert: Utimaco finds regional disparities in consumers’ level of trust in digital security – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Aachen, Germany, July 10, 2023 – Utimaco, a leading global provider of IT security solutions that is celebrating its 40th year pioneering trusted...
News Alert: Silent Signal discovers a critical vulnerability in IBM i System – CVE-2023-30990 – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Budapest, Hungary, July 07, 2023 — Silent Signal, a leading technology provider of state-of-the-art ethical hacking services and solutions, discovered and...
Brute Force and Dictionary Attacks: A Guide for IT Leaders – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: It’s essential that cybersecurity professionals understand the risks associated with brute force attacks. Read this guide from TechRepublic Premium to find out...
Ransomware Extortion Skyrockets in 2023, Reaching $449.1 Million and Counting – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023THNRansomware / Cyber Threat Ransomware has emerged as the only cryptocurrency-based crime to grow in 2023, with cybercriminals extorting...
Startup Spotlight: Mobb Aims to Be the Fixer – Source: www.darkreading.com
Source: www.darkreading.com – Author: Karen Spiegelman, Features Editor In response to widespread and dangerous vulnerabilities such as Log4j and the exploited GoAnywhere remote-code execution flaw, savvy...