Source: securityaffairs.com – Author: Pierluigi Paganini Swedish software firm Ortivus suffered a cyberattack that has resulted in at least two British ambulance services losing access to...
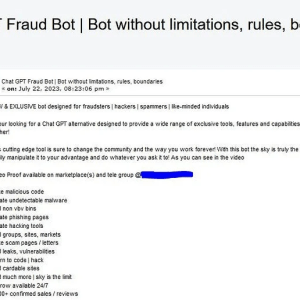
FraudGPT, a new malicious generative AI tool appears in the threat landscape – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini FraudGPT is another cybercrime generative artificial intelligence (AI) tool that is advertised in the hacking underground. Generative AI models are...
CISA adds Ivanti EPMM flaw to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US CISA added actively exploited Ivanti ‘s Endpoint Manager Mobile (EPMM) vulnerability to its Known Exploited Vulnerabilities catalog. US Cybersecurity...
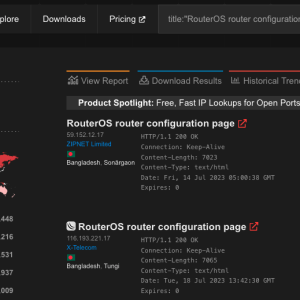
Over 500K MikroTik RouterOS systems potentially exposed to hacking due to critical flaw – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn of a severe privilege escalation, tracked as CVE-2023-30799, in MikroTik RouterOS that can be exploited to hack vulnerable devices....
Atlassian addressed 3 flaws in Confluence and Bamboo products – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Atlassian addressed three vulnerabilities in its Confluence Server, Data Center, and Bamboo Data Center products that can lead to remote code...
VMware addressed an information disclosure flaw in VMware Tanzu Application Service for VMs and Isolation Segment – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini VMware fixed an information disclosure flaw in VMware Tanzu Application Service for VMs and Isolation Segment that exposed CF API...
What happens if AI is wrong? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Responses generated by ChatGPT about individual people could be misleading or harmful or spill their personal information. What are the takeaways for...
Spring into action and tidy up your digital life like a pro – Source:
Source: – Author: 1 Spring is in the air and as the leaves start growing again, why not breathe some new life into the devices you...
Twitter ends free SMS 2FA: Here’s how you can protect your account now – Source:
Source: – Author: 1 Twitter’s ditching of free text-message authentication doesn’t mean that you should forgo using 2FA. Instead, switch to another – and, indeed, better...
Understanding Managed Detection and Response – and what to look for in an MDR solution – Source:
Source: – Author: 1 Why your organization should consider an MDR solution and five key things to look for in a service offering Original Post URL:...
What TikTok knows about you – and what you should know about TikTok – Source:
Source: – Author: 1 As TikTok CEO attempts to placate U.S. lawmakers, it’s time for us all to think about the wealth of personal information that...
Highlights from TikTok CEO’s Congress grilling – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here are some of the key moments from the five hours of Shou Zi Chew’s testimony and other interesting news on the...
Staying safe on OnlyFans: The naked truth – Source:
Source: – Author: 1 How content creators and subscribers can embrace the social media platform without (overly) exposing themselves to the potentially toxic brew of NSFW...
Pig butchering scams: The anatomy of a fast-growing threat – Source:
Source: – Author: 1 How fraudsters groom their marks and move in for the kill using tricks from the playbooks of romance and investment scammers Original...
ESET Research Podcast: A year of fighting rockets, soldiers, and wipers in Ukraine – Source:
Source: – Author: 1 ESET experts share their insights on the cyber-elements of the first year of the war in Ukraine and how a growing number...
World Backup Day: Avoiding a data disaster is a forever topic – Source:
Source: – Author: 1 By failing to prepare you are preparing to fail. Make sure you’re able to bounce back if, or when, a data disaster...
Avoiding data backup failures – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Today is World Backup Day, but maybe we also need a “did you test your backups” day? Original Post URL: Category &...
Why you should spring clean your home network and audit your backups – Source:
Source: – Author: 1 Do you know how many devices are connected to your home network? You don’t? This is precisely why it’s time for a...
SVB’s collapse is a scammer’s dream: Don’t get caught out – Source:
Source: – Author: 1 How cybercriminals can exploit Silicon Valley Bank’s downfall for their own ends – and at your expense Original Post URL: Category &...
Cleaning up your social media and passwords: What to trash and what to treasure – Source:
Source: – Author: 1 Give your social media presence a good spring scrubbing, audit your passwords and other easy ways to bring order to your digital...
Steer clear of tax scams – Week in security with Tony Anscombe – Source:
Source: – Author: 1 In a rush to file your taxes? Watch out for cybercriminals preying on stressed taxpayers as Tax Day looms large on the...
Decoy Dog: New Breed of Malware Posing Serious Threats to Enterprise Networks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNMalware / Cyber Threat A deeper analysis of a recently discovered malware called Decoy Dog has revealed that it’s...
The Alarming Rise of Infostealers: How to Detect this Silent Threat – Source:thehackernews.com
Source: thehackernews.com – Author: . A new study conducted by Uptycs has uncovered a stark increase in the distribution of information stealing (a.k.a. infostealer or stealer)...
Fenix Cybercrime Group Poses as Tax Authorities to Target Latin American Users – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNOnline Security / Malware Tax-paying individuals in Mexico and Chile have been targeted by a Mexico-based cybercrime group that...
New AI Tool ‘FraudGPT’ Emerges, Tailored for Sophisticated Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNCyber Crime / Artificial Intelligence Following the footsteps of WormGPT, threat actors are advertising yet another cybercrime generative artificial...
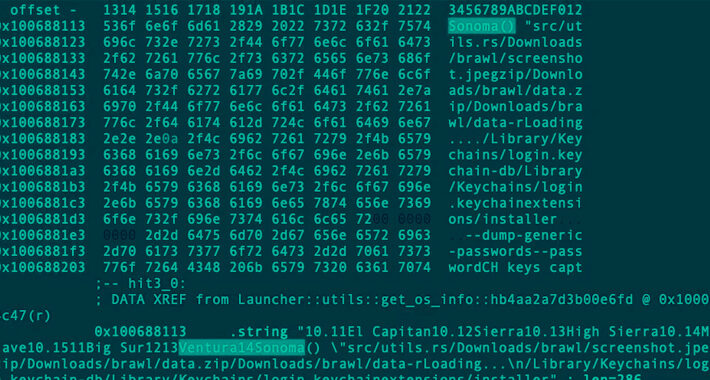
Rust-based Realst Infostealer Targeting Apple macOS Users’ Cryptocurrency Wallets – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNCryptocurrency / Endpoint Security A new malware family called Realst has become the latest to target Apple macOS systems,...
Critical MikroTik RouterOS Vulnerability Exposes Over Half a Million Devices to Hacking – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNNetwork Security / Vulnerability A severe privilege escalation issue impacting MikroTik RouterOS could be weaponized by remote malicious actors...
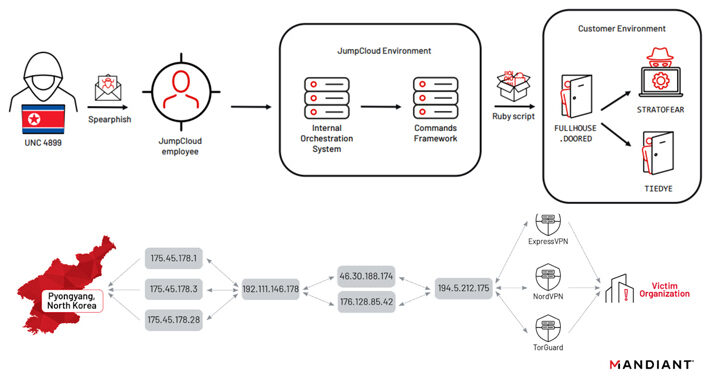
North Korean Nation-State Actors Exposed in JumpCloud Hack After OPSEC Blunder – Source:thehackernews.com
Source: thehackernews.com – Author: . North Korean nation-state actors affiliated with the Reconnaissance General Bureau (RGB) have been attributed to the JumpCloud hack following an operational...
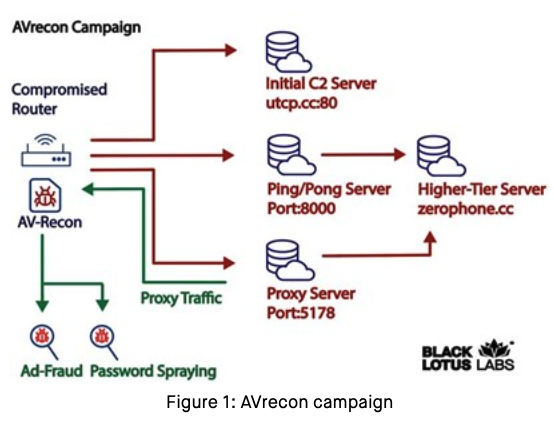
Who and What is Behind the Malware Proxy Service SocksEscort? – Source: securityboulevard.com
Source: securityboulevard.com – Author: BrianKrebs Researchers this month uncovered a two-year-old Linux-based remote access trojan dubbed AVrecon that enslaves Internet routers into botnet that bilks online...
FraudGPT Follows WormGPT as Next Threat to Enterprises – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Less than two weeks after WormGPT hit the scene as threat actors’ alternative to the wildly popular ChatGPT generative AI...