Source: – Author: 1 Why is kids’ personal information in high demand, how do criminals steal it, and what can parents do to help prevent child...
Protect yourself from ticketing scams ahead of the Premier League Summer Series USA Tour – Source:
Source: – Author: 1 There is a significant secondary marketplace where tickets can sell for several times their original value, opening the opportunity for scammers and...
Key findings from ESET Threat Report H1 2023 – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here’s how cybercriminals have adjusted their tactics in response to Microsoft’s stricter security policies, plus other interesting findings from ESET’s new Threat...
The danger within: 5 steps you can take to combat insider threats – Source:
Source: – Author: 1 Some threats may be closer than you think. Are security risks that originate from your own trusted employees on your radar? Original...
ESET Research Podcast: Finding the mythical BlackLotus bootkit – Source:
Source: – Author: 1 Here’s a story of how an analysis of a supposed game cheat turned into the discovery of a powerful UEFI threat Original...
ESET Threat Report H1 2023 – Source:
Source: – Author: 1 A view of the H1 2023 threat landscape as seen by ESET telemetry and from the perspective of ESET threat detection and...
Emotet: sold or on vacation? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Originally a banking trojan, Emotet later evolved into a full-blown botnet and went on to become one of the most dangerous cyberthreats...
What’s up with Emotet? – Source:
Source: – Author: 1 A brief summary of what happened with Emotet since its comeback in November 2021 Original Post URL: Category & Tags: – Views:...
Deepfaking it: What to know about deepfake-driven sextortion schemes – Source:
Source: – Author: 1 Criminals increasingly create deepfake nudes from people’s benign public photos in order to extort money from them, the FBI warns Original Post...
Verizon 2023 DBIR: What’s new this year and top takeaways for SMBs – Source:
Source: – Author: 1 Here are some of the key insights on the evolving data breach landscape as revealed by Verizon’s analysis of more than 16,000...
Linux version of Abyss Locker ransomware targets VMware ESXi servers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The Abyss Locker operation is the latest to develop a Linux encryptor to target VMware’s ESXi virtual machines platform in...
Browser developers push back on Google’s “web DRM” WEI API – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Google’s plans to introduce the Web Environment Integrity (WEI) API on Chrome has been met with fierce backlash from internet...
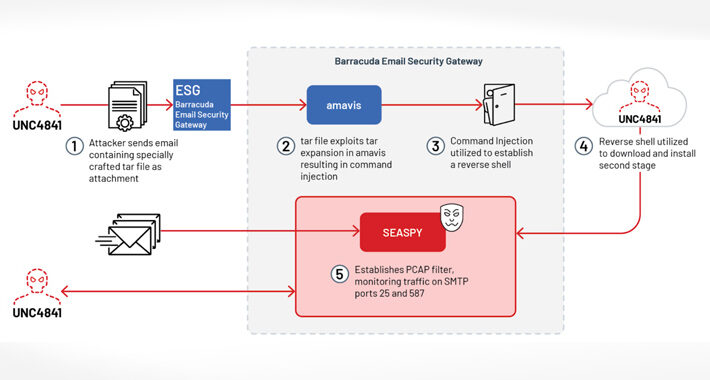
CISA warns about SUBMARINE Backdoor employed in Barracuda ESG attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warns of threat actors deploying the SUBMARINE Backdoor in Barracuda ESG attacks....
Now Abyss Locker also targets VMware ESXi servers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A Linux variant of the Abyss Locker designed to target VMware ESXi servers appeared in the threat landscape, experts warn....
BSides Leeds 2023 – Janette Bonar Law – Hackanory: The Power Of Stories – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
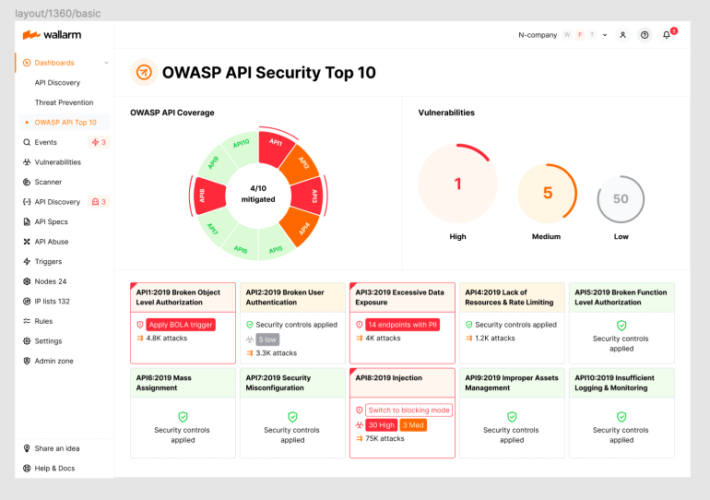
2023 OWASP Top-10 Series: API1:2023 Broken Object Level Authorization – Source: securityboulevard.com
Source: securityboulevard.com – Author: wlrmblog Welcome to the 2nd post in our weekly series on the new 2023 OWASP API Security Top-10 list, with a particular...
Ivanti Says Second Zero Day Used in Norway Govt Breach – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Cybercrime , Fraud Management & Cybercrime Exploitation No Longer Requires Admin Authentication When Chained with Earlier...
N Korean Hackers Phishing With US Army Job Lures – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Anti-Phishing, DMARC , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Researchers Say APT37 Group Likely Behind Campaign Targeting South...
Ivanti Says Second Zero Day Used in Norway Govt Breach – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Cybercrime , Fraud Management & Cybercrime Exploitation No Longer Requires Admin Authentication When Chained with Earlier...
N Korean Hackers Phishing With US Army Job Lures – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Anti-Phishing, DMARC , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Researchers Say APT37 Group Likely Behind Campaign Targeting South...
Security Serious Unsung Heroes Awards 2023 Open for Nominations – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Nominations are open for the eighth annual Security Serious Unsung Heroes Awards to be held in London and run by Eskenzi PR. The...
New Android Malware CherryBlos Utilizing OCR to Steal Sensitive Data – Source:thehackernews.com
Source: thehackernews.com – Author: . A new Android malware strain called CherryBlos has been observed making use of optical character recognition (OCR) techniques to gather sensitive...
RFP Template for Browser Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 29, 2023The Hacker NewsBrowser Security / Data Security Increasing cyber threats and attacks have made protecting organizational data a paramount...
Apple Sets New Rules for Developers to Prevent Fingerprinting and Data Misuse – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 29, 2023THNData Security / Privacy Apple has announced plans to require developers to submit reasons to use certain APIs in...
Hackers Deploy “SUBMARINE” Backdoor in Barracuda Email Security Gateway Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 29, 2023THNEmail Security / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday disclosed details of a “novel...
Ivanti Warns of Another Endpoint Manager Mobile Vulnerability Under Active Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 29, 2023THNVulnerability / Enterprise Security Ivanti has disclosed yet another security flaw impacting Endpoint Manager Mobile (EPMM), formerly known as...
Apple rejects new name ‘X’ for Twitter iOS app because… rules – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma Mr. Musk may have successfully pushed Twitter’s new name and logo, ‘X’, and even made the vanity domain x.com redirect to...
CISA: New Submarine malware found on hacked Barracuda ESG appliances – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan CISA says new malware known as Submarine was used to backdoor Barracuda ESG (Email Security Gateway) appliances on federal agencies’...
Apple says new App Store API rules will limit user fingerprinting – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Starting this fall, Apple has announced that developers will be required to provide a reason for using certain APIs that...
The Week in Ransomware – July 28th 2023 – New extortion tactics – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams With ransom payments declining, ransomware gangs are evolving their extortion tactics to utilize new methods to pressure victims. This was...