Source: thehackernews.com – Author: . Sep 06, 2023THNZero Day / Mobile Security Google has rolled out monthly security patches for Android to address a number of...
Alert: Phishing Campaigns Deliver New SideTwist Backdoor and Agent Tesla Variant – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023THNCyber Threat / Malware The Iranian threat actor tracked as APT34 has been linked to a new phishing attack...
Three CISOs Share How to Run an Effective SOC – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023The Hacker NewsSecurity Operations Center (SOC) The role of the CISO keeps taking center stage as a business enabler:...
Cryptocurrency Startup Loses Encryption Key for Electronic Wallet – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Anonymous • September 6, 2023 7:49 AM “I can’t understand why anyone thinks these technologies are a good...
Pizza Hut Australia leaks one million customers’ details, claims ShinyHunters hacking group – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley The ShinyHunters hacking group has claimed that in the last couple of months it has stolen more than 30 million...
Zscaler Data Security Platform Takes on Symantec, CASB Tools – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Access Security Brokers (CASB) , Data Loss Prevention (DLP) , Endpoint Security CEO Jay Chaudhry: In-Line Inspection, App-to-App Protection Aid...
Why Tenable Is Eyeing Security Vendor Ermetic at Up to $350M – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Security , Security Operations Ermetic Is in Line for a 9-Figure Deal Just 40 Months After Emerging From Stealth Michael...
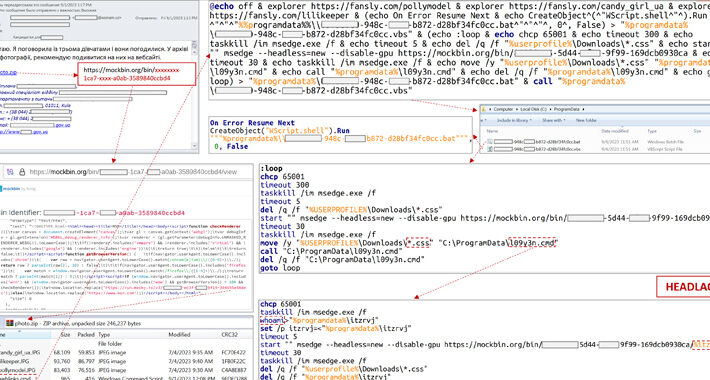
APT28 Spear-Phishes Ukrainian Critical Energy Facility – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Energy Facility Impeded Attack by Blocking the Launch of the Windows Script...
Official Slams Aussie Firms for Data Breach Reporting Delays – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Security Operations , Standards, Regulations & Compliance Information Commissioner Urges Organizations to Accelerate Breach Notifications Jayant Chakravarti (@JayJay_Tech)...
EU Artificial Intelligence Act Not a Panacea for AI Risk – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Standards, Regulations & Compliance Dutch Citizens ‘Should Not Expect...
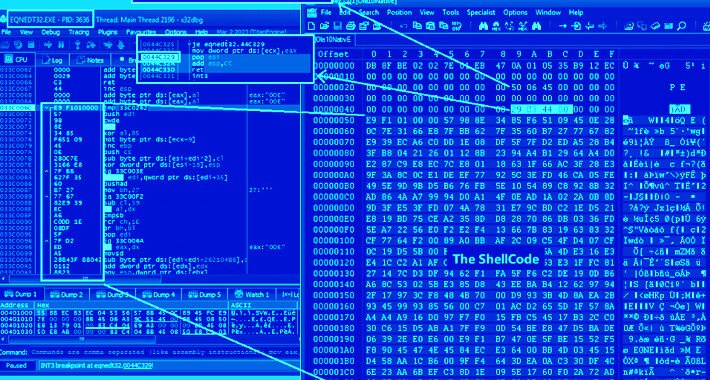
Researchers Discover Critical Vulnerability in PHPFusion CMS – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Security researchers have discovered what they described as a critical vulnerability in the relatively widely used...
LockBit Leaks Documents Filched From UK Defense Contractor – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Last month, a British perimeter security company was breached by the LockBit group. Despite only accessing...
Tuya Smart and Amazon Web Services Collaborate to Establish an IoT Security Lab – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 NEW YORK, Sept. 4, 2023 /PRNewswire/ — Tuya Smart (NYSE: TUYA, HKEX: 2391), a global IoT developer service provider, announced at the re:Inforce China conference to...
Global Cloud Security Market to Reach $62.9B by 2028 – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 DUBLIN, Sept. 4, 2023 /PRNewswire/ — The “Global Cloud Security Market by Offering (Solution and Services), Solutions (CASB, CWPP, CSPM, CDR, and CIEM), Services...
Hornetsecurity Releases 365 Total Protection Plan 4 for Microsoft 365 – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 LONDON, Sept. 5, 2023 /PRNewswire/ — Leading cybersecurity provider Hornetsecurity has launched its Plan 4 ‘Compliance & Awareness’ solution of the 365 Total...
GhostSec Leaks Source Code of Alleged Iranian Surveillance Tool – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Hacker group GhostSec is disclosing the source code of the various software packages, alleging them to...
Peiter ‘Mudge’ Zatko Lands Role as CISA Senior Technical Adviser – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Former Twitter security chief and “executive in residence” at cybersecurity firm Rapid7, Peiter “Mudge” Zatko, has landed...
United Airlines Says the Outage That Held Up Departing Flights Was Not a Cybersecurity Issue – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press United Airlines said Tuesday that a software update triggered a glitch that forced it to halt departures nationwide, briefly crippling...
CISA Hires ‘Mudge’ to Work on Security-by-Design Principles – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine The U.S. government’s cybersecurity agency CISA on Monday confirmed the addition of Peiter ‘Mudge’ Zatko to its roster of prominent...
MITRE and CISA Release Open Source Tool for OT Attack Emulation – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The MITRE Corporation and the US Cybersecurity and Infrastructure Security Agency (CISA) today announced a new extension for the open...
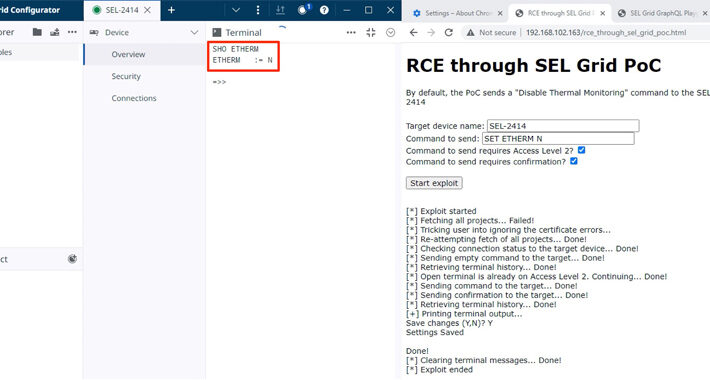
9 Vulnerabilities Patched in SEL Power System Management Products – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Nine vulnerabilities, including potentially serious flaws, were patched recently in a couple of electric power management products made by Schweitzer...
7 Million Users Possibly Impacted by Freecycle Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Freecycle.org, a platform that allows users to recycle their belongings, has prompted millions of users to reset their passwords after...
Norfolk Southern Says a Software Defect — Not a Hacker — Forced It to Park Its Trains This Week – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Norfolk Southern believes a software defect — not a hacker — was the cause of the widespread computer outage that...
Okta Says US Customers Targeted in Sophisticated Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Identity and access management solutions provider Okta warns that multiple customers based in the United States have been targeted in...
UK Boards Are Growing Less Concerned About Cyber-Risk – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Far fewer board members of UK companies are worried about cyber-risk than their global peers, according to a new study from...
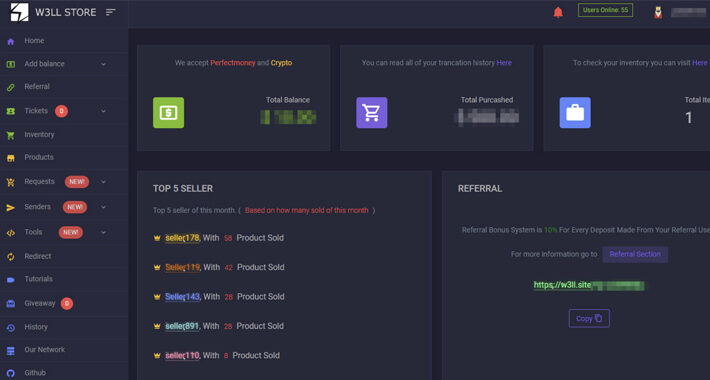
Experts Uncover Underground Phishing “Empire” W3LL – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have uncovered a new covert phishing operation selling sophisticated tools used to target an estimated 56,000 Microsoft 365 accounts...
Crypto Casino Stake.com Back Online After $40m Heist – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Hackers have stolen over $40m in cryptocurrency from the self-styled “world’s leading betting platform,” the firm has revealed. Curaçao-headquartered Stake.com offers...
9 Alarming Vulnerabilities Uncovered in SEL’s Power Management Products – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023THNVulnerability / ICS Nine security flaws have been disclosed in electric power management products made by Schweitzer Engineering Laboratories...
W3LL Store: How a Secret Phishing Syndicate Targets 8,000+ Microsoft 365 Accounts – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023THNCyber Crime / Email Security A previously undocumented “phishing empire” has been linked to cyber attacks aimed at compromising...
Ukraine’s CERT Thwarts APT28’s Cyberattack on Critical Energy Infrastructure – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 06, 2023THNCyber Attack / Critical Infrastructure The Computer Emergency Response Team of Ukraine (CERT-UA) on Tuesday said it thwarted a...