Source: securityboulevard.com – Author: Michael Vizard A Barracuda Networks report published today suggests cybercriminals are becoming more adept at manipulating email inbox rules to hide their...
The Zero Trust Security Model: What You Need to Know – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mark Knowles Remember the days when security was simple – or so we thought. You locked your valuable data deep inside corporate...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – Targeting The Ransomware Kill Chain – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-targeting-the-ransomware-kill-chain/ Category & Tags: CISO Suite,Governance, Risk &...
The 10 most common cyber security myths – Source: securityboulevard.com
Source: securityboulevard.com – Author: Scott Wright Although no data is unimportant, there are different security or risk levels to data which will change how you share...
Black Hat Fireside Chat: Flexxon introduces hardened SSD drives as a last line defense – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Byron V. Acohido Creating ever smarter security software to defend embattled company networks pretty much sums up the cybersecurity industry....
IoT Security Best Practices: 2023 Guide to Safeguard Your Devices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback Introduction: The Rising Importance of IoT in 2023 In the digital age, the Internet of Things (IoT) has emerged as...
UK Parliament Approves Online Safety Bill – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Encryption & Key Management , Geo Focus: The United Kingdom , Geo-Specific Cabinet Ministers Call on Facebook to Stop Rollout of...
Why Palo Alto Is Eyeing Secure Browser Firm Talon for $600M – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Next-Generation Technologies & Secure Development Talon Is in Line for a 9-Figure Deal Just 29 Months After Emerging...
Financially Motivated Hacks by Chinese-Speaking Actors Surge – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime These Hackers May Equal or Surpass Threat Posed by Russian Hackers, Researchers Say Prajeet Nair...
Live Webinar | Unlocking the 8 Key Human Cyber Risk Factors: Strengthening Security in Your Organization – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Ira Winkler Field CISO and Vice President, CYE Considered one of the world’s most influential security professionals, Ira Winkler, CISSP, is...
5 Ways to Protect Critical Infrastructure in the Oil and Gas Industry – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Matt Wiseman Sr. Product manger, OPSWAT Matt Wiseman is a Sr. Product Manager at OPSWAT managing the OT product line. Matt’s...
WatchGuard Buys CyGlass to Bring NDR to Midmarket Customers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Network Detection & Response , Open XDR , Security Operations M&A Gives WatchGuard Clients More Visibility Into East-West Traffic, Cloud Activity...
Feds Warn Health Sector of Lazarus Group Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development HHS: North Korean-Sponsored Group Is Exploiting Critical Zoho ManageEngine...
Financially Motivated Hacks by Chinese-Speaking Actors Surge – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime These Hackers May Equal or Surpass Threat Posed by Russian Hackers, Researchers Say Prajeet Nair...
Why Palo Alto Is Eyeing Secure Browser Firm Talon for $600M – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Endpoint Security , Next-Generation Technologies & Secure Development Talon Is in Line for a 9-Figure Deal Just 29 Months After Emerging...
Live Webinar | Protecting Your Workloads from Modern Threats with VMware Ransomware Recovery – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Brett Foy Staff Solution Architect, VMware A member of VMware’s Cloud Incubation team, Brett focuses on helping customers, partners, VMware field...
Feds Warn Health Sector of Lazarus Group Attacks – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development HHS: North Korean-Sponsored Group Is Exploiting Critical Zoho ManageEngine...
5 Ways to Protect Critical Infrastructure in the Oil and Gas Industry – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Matt Wiseman Sr. Product manger, OPSWAT Matt Wiseman is a Sr. Product Manager at OPSWAT managing the OT product line. Matt’s...
Don’t Let AI Frenzy Lead to Overlooking Security Risks – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Successful AI Implementation Requires a Secure Foundation, Attention to Regulations...
WatchGuard Buys CyGlass to Bring NDR to Midmarket Customers – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Network Detection & Response , Open XDR , Security Operations M&A Gives WatchGuard Clients More Visibility Into East-West Traffic, Cloud Activity...
Finnish Authorities Dismantle Notorious PIILOPUOTI Dark Web Drug Marketplace – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNCyber Crime / Dark Web Finnish law enforcement authorities have announced the takedown of PIILOPUOTI, a dark web marketplace...
Critical Security Flaws Exposed in Nagios XI Network Monitoring Software – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNNetwork Security / Vulnerability Multiple security flaws have been disclosed in the Nagios XI network monitoring software that could...
Do You Really Trust Your Web Application Supply Chain? – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023The Hacker NewsWeb Application Security Well, you shouldn’t. It may already be hiding vulnerabilities. It’s the modular nature of...
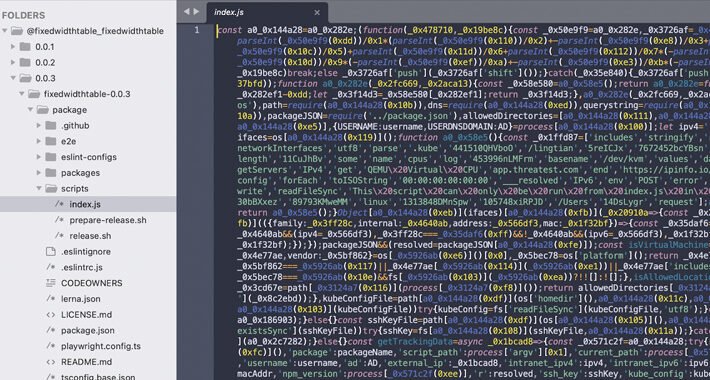
Fresh Wave of Malicious npm Packages Threaten Kubernetes Configs and SSH Keys – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNKubernetes / Supply Chain Attack Cybersecurity researchers have discovered a fresh batch of malicious packages in the npm package...
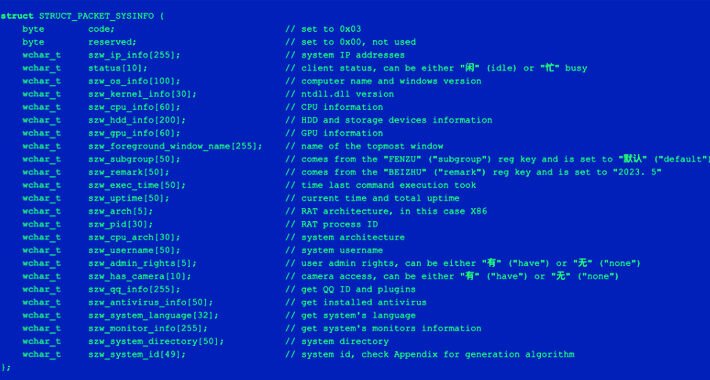
Sophisticated Phishing Campaign Targeting Chinese Users with ValleyRAT and Gh0st RAT – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 20, 2023THNMalware Attack / Cyber Threat Chinese-language speakers have been increasingly targeted as part of multiple email phishing campaigns that...
Intel Launches New Attestation Service as Part of Trust Authority Portfolio – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Chip giant Intel announced on the second day of its Intel Innovation 2023 event the general availability of an attestation...
Tor-Based Drug Marketplace Piilopuoti Shut Down by Law Enforcement – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Authorities in Finland and Europol on Tuesday announced the seizure of Piilopuoti, a drugs marketplace operating on the Tor network...
Staying on Topic in an Off Topic World – Source: www.securityweek.com
Source: www.securityweek.com – Author: Joshua Goldfarb Have you ever been in a meeting where someone keeps taking the discussion off topic? Have you ever tried to...
Discern Security Emerges From Stealth Mode With $3 Million in Funding – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire AI-driven policy management cybersecurity startup Discern Security on Tuesday announced that it has emerged from stealth mode with $3 million...
DHS Publishes New Recommendations on Cyber Incident Reporting – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Department of Homeland Security (DHS) on Tuesday published a new document containing recommendations on how federal agencies can...