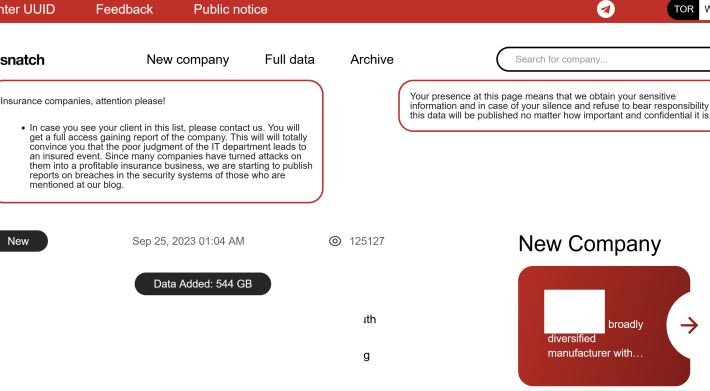
Source: krebsonsecurity.com – Author: BrianKrebs The victim shaming site operated by the Snatch ransomware group is leaking data about its true online location and internal operations,...
Webinar Highlights – Mastering the new SEC Regs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gaurav Banga It was great to chat last week on the topic of the new SEC Rules with my good friend Ed...
Step on It: What to Know About TISAX Compliance in the Automotive Market – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matt Kelly The automotive industry is one of the largest in the world, with sales estimated at $2.95 trillion for 2022. It’s...
Protecting Critical Infrastructure From Ransomware with LogRhythm NDR – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ianni Le A European-based organization in the transportation industry needed a way to protect its data with a solution that could mitigate...
Google LibWebP Arbitrary Code Execution Vulnerability (CVE-2023-5129) Notification – Source: securityboulevard.com
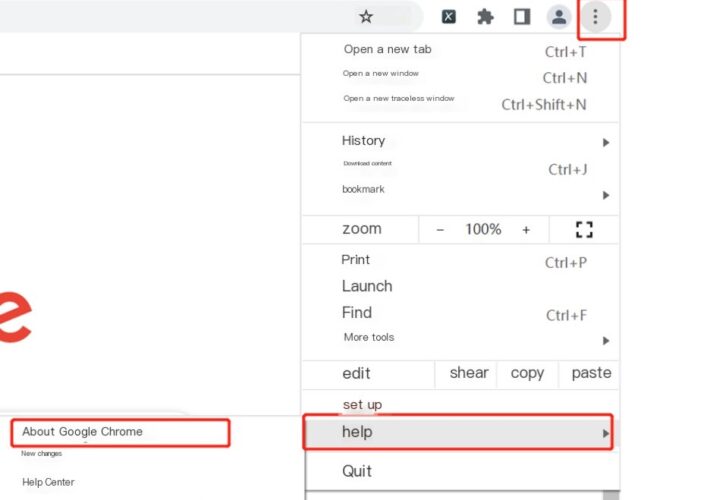
Source: securityboulevard.com – Author: NSFOCUS Overview Recently, NSFOCUS CERT found that Google officially fixed a heap buffer overflow vulnerability (CVE-2023-4863). Due to a flaw in the...
Cyber Week 2023 & The Israel National Cyber Directorate Presents – Scaling up Cyber Capacity Building: The Sectoral Approach to Critical Infrastructure Protection – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/cyber-week-2023-the-israel-national-cyber-directorate-presents-scaling-up-cyber-capacity-building-the-sectoral-approach-to-critical-infrastructure-protection/ Category & Tags: CISO Suite,Governance, Risk &...
ZenRAT Targets Windows Users with Fake Bitwarden Site – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Hackers are using a bogus download page for Bitwarden’s password manager solution to target Windows users with a new remote...
Meet the Ona: Stefan Popa – Source: securityboulevard.com
Source: securityboulevard.com – Author: ltabo Meet the Ona: Stefan Popa ltabo Wed, 09/27/2023 – 18:12 Today, we announced a series of strategic expansion efforts, including a...
RATs, rootkits, and ransomware (oh my!) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Avast Blog In a vast world of online threats, certain terms can stand out for their mysterious nature and vague implications. They...
Randall Munroe’s XKCD ‘Lying’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe, maker of XKCD! Permalink *** This is a Security Bloggers...
Unlock 2023’s Top Benefits of Security as a Service! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback Introduction In today’s digital age, the significance of robust cybersecurity for small and medium-sized businesses (SMBs) is more crucial than...
School, Hospital Leaders on Front Lines of Ransomware Attack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware From Paying Ransoms to Rebuilding IT Systems, Here’s What the Response Looked Like Michael Novinson...
Why Palo Alto Is Eyeing Data Defense Firm Dig at $300M-$400M – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Big Data Security Analytics , Data Loss Prevention (DLP) , Endpoint Security Dig Security Is Set for a 9-Figure Deal Just...
Why OT Security Keeps Some Healthcare Leaders Up at Night – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 It’s not just medical device cybersecurity that’s keeping some healthcare security leaders up at night – it’s also the risks posed...
ShadowSyndicate: A New Player in the RaaS Landscape – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware New Group Has Connections to Name-Brand Ransomware-as-a-Service Groups Mihir Bagwe (MihirBagwe) • September 27, 2023...
Live Webinar I Breaking Barriers: Transforming Threat Detection and Response – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Simon Perry Security Evangelist, VMware Carbon Black Simon Perry has 40 years of work experience and has provided strategic cyber security...
Live Webinar | With the Rise of Generative AI, Where is Cloud Security Headed? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 JT Rakitan Security Product Marketer, Sumo Logic Currently a Security Product Marketer at Sumo Logic, JT Rakitan began his marketing journey...
Chinese Hackers Target Routers in IP Theft Campaign – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Network Firewalls, Network Access Control BlackTech Exploits Trusted Relationship Between Outpost...
FDA Finalizes Guidance Just as New Device Cyber Regs Kick In – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Healthcare , Industry Specific Starting Oct. 1, Agency to Require Secure Dev Framework, Threat Modeling, SBOMs Marianne Kolbasuk...
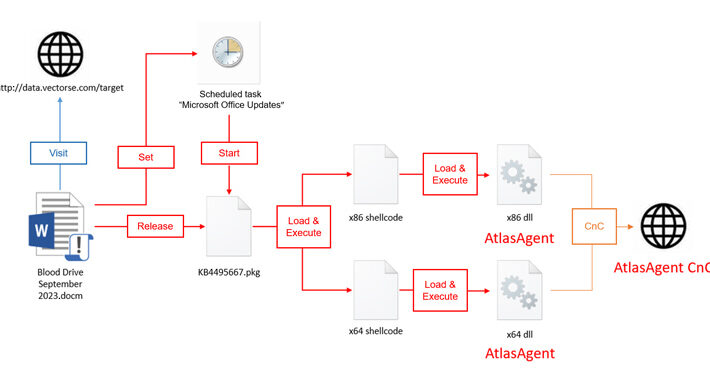
Red Cross-Themed Phishing Attacks Distributing DangerAds and AtlasAgent Backdoors – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 27, 2023THNMalware / Cyber Attack A new threat actor known as AtlasCross has been observed leveraging Red Cross-themed phishing lures...
Researchers Uncover New GPU Side-Channel Vulnerability Leaking Sensitive Data – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 27, 2023THNVulnerability / Endpoint Security A novel side-channel attack called GPU.zip renders virtually all modern graphics processing units (GPU) vulnerable...
New Survey Uncovers How Companies Are Confronting Data Security Challenges Head-On – Source:thehackernews.com
Source: thehackernews.com – Author: . Data security is in the headlines often, and it’s almost never for a positive reason. Major breaches, new ways to hack...
Predicting the next wave of emerging threats in neobank security – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau Tamas Kadar, CEO of SEON, shares his expert insights into what neobanks need to look out for when it comes to...
Must-know insights when navigating the CISO career path – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: The CISO career path is as exciting as it is fraught with perils. Modern CISOs reside at the intersection...
Breaking News Q&A: What Cisco’s $28 billion buyout of Splunk foretells about cybersecurity – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido There’s a tiny bit more to Cisco’s acquisition of Splunk than just a lumbering hardware giant striving...
Sony`s Systems Breached. Ransomed.vc Claims Stealing 260 GB of Data – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Ransomed.vc threat group claims they`re responsible for an alleged Sony data breach and attempt to sell the stolen data on...
Phobos Ransomware: Everything You Need to Know and More – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Alina Georgiana Petcu In the ever-evolving landscape of cyber threats, ransomware remains a pervasive and destructive weapon in the arsenal of cybercriminals....
QR codes in email phishing – Source: securelist.com
Source: securelist.com – Author: Roman Dedenok QR codes are everywhere: you can see them on posters and leaflets, ATM screens, price tags and merchandise, historical buildings...
Microsoft now rolling out AI-powered Paint Cocreator to Insiders – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft’s new AI image generation Paint tool powered by OpenAI’s DALL-E text-to-image model is now rolling out to Windows Insiders...
US and Japan warn of Chinese hackers backdooring Cisco routers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas US and Japanese law enforcement and cybersecurity agencies warn of the Chinese ‘BlackTech’ hackers breaching network devices to install custom...