The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Value creation in the metaverse – The Real business of the virtual world by McKinsey & Company – June 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 ThreatLabz Research Team – State of Ransomware Report by Zscaler
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
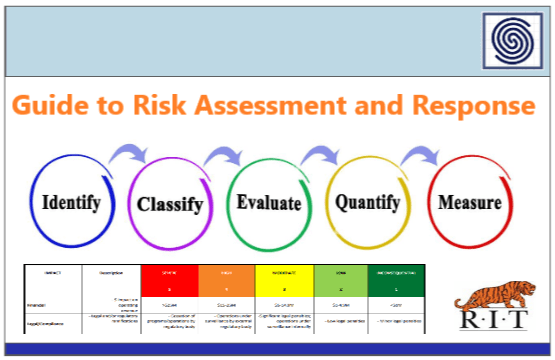
Guide to Risk Assessment and Response by RIT
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
HUNTPEDIA – Your Threat Hunting Knowledge Compendium by sqrrl
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
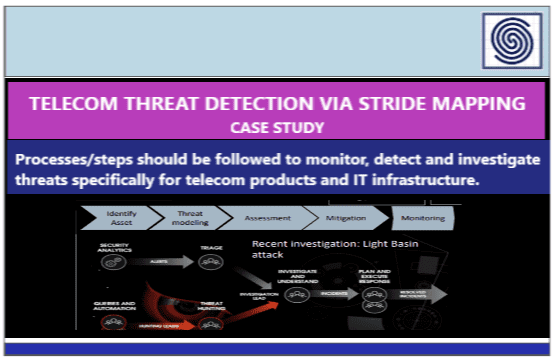
Telecom Threat Detection via Stride Mapping Case Study
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Security and Business Resilience – Thinking strategically by IT Governance
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Malware Analysis TIPS & TRICKS Poster by SANS DFIR
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CYBERSECURITY HANDBOOK – Best practices for the protection and resilience of network and information systems – Ministry of Digital Governance – Greece
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Deception at Scale – How Malware Abuses Trust by VIRUSTOTAL
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Five Ways to Secure SAP S/4 HANA Migrations by ONAPSIS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
5 Ways to Maximize the Security, Performance and Reliability of Your Online Business by Cloudflare
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Social Engineering and its menace by Hidecybersecurity.com
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
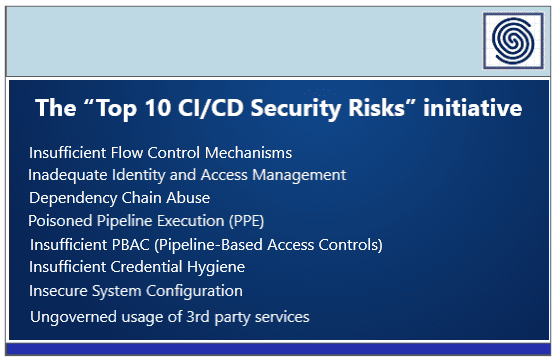
Top 10 CI/CD Security Risks by Cider Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Adopting secure DevOps – An introduction to transforming your organization by KPMG
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A global study EVERYTHING IS CONNECTED – Uncovering the ransomware threat from global supply chains by TRENDMICRO
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Nature of cyber incidents – Based on cyberattack investigations conducted by Kaspersky Global Emergency Response Team
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
PEN-200 and the OSCP prep book by offs.ec
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CIBER SEGURO – Una guía perruna sobre seguridad en Internet para niños y adultos “todos deben leer esto” by Renee Tarun y Susan Burg
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Malware and Vulnerability Trends Report H1 2022 by Recorded Future
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Maltego handbook for Incident Response
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Remediation and Hardering Strategies for Microsoft 365 to Defend Against APT29 Group – Threat Intelligence White Paper by MANDIANT
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 Consumer Identity Breach Report by ForgeRock – Eve Maler.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The State of Ransomware in Retail 2022 by SOPHOS –
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity in OT Environments – Case Study in the Oil & Gas Sector by Telefonica Tech & Nozomi Networks
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Web3 Defined – An overview report by Brainsy
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
State of Crypto & the Web3 An overview report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
M-TRENDS 2022 Mandiant Special Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Threat Hunting 101 – A Framework for Building and Maturing a Proactive Threat Hunting Program by RELIAQUEST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
THIRD-PARTY SECURITY – RISK MANAGEMENT PLAYBOOK – A study of common , emerging, and pioneering capabilities and practices by riskrecon Mastercard
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...