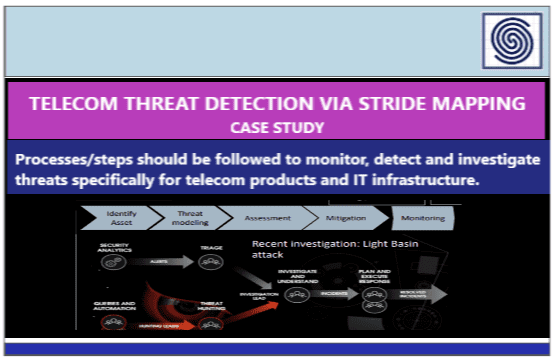
Objective:What processes/steps should be followed to monitor, detect and investigate threats specifically for telecom products and...
- Home
- About Us
- Contact Us
- Register to apply for a free CISO2CISO Membership
- CISO2CISO Network
- CISO2CISO Services
- Sitemap
- Submit News