The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SOC Analyst Interview Questions
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Open Source Intelligence OSINT mini guide 2022 by Marcus P. Zillman
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The state of Cloud configuration security practices by Olivia Powel – CSHUB – Find out where organizations need to focus their efforts to secure their cloud applications as revealed by the results of Cyber Security Hub’s Cloud Configuration Security Practices survey.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Guide to a Secure Enterprise Network Landscape NIST SP 800-215
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
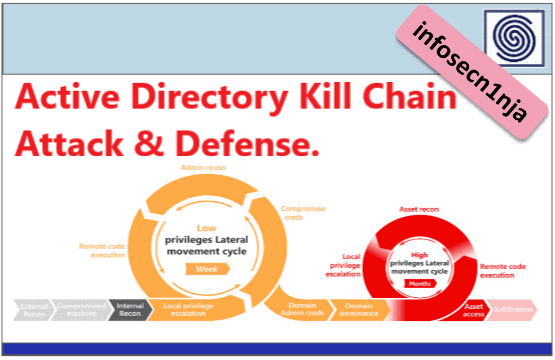
Active Directory Kill Chain – Attack and defend active directory using modern post exploitation adversary tradecraft activity
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2022 VEEAM Ransomware Trends Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Complete Guide to Implementing DevSecOps in AWS by aspire
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
API Security for Dummies Series – Data Theorem Special Edition
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
7 Best Reasons to be a CISO by Michaell Hill UK Editor CSO
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Nozomi OT IoT Security Report – Cyber War Insights, Threats and Trends, Recommendations
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Pentester Blueprint – a Guide to Becoming a Pentester
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
BTFM – Blue Team Field Manual 2022 – by Alan White and Ben Clark
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Master Cybersecurity with Eudureka – Getting Started with Cybersecurity
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
EVIL PLC ATTACK – WEAPONIZING PLCS By Team82, Claroty Research Team
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ASSESSING OPERATIONAL TECHNOLOGY (OT) CYBERSECURITY MODEL – AN ANALYSIS OF LEASED DATACENTERS UTILIZING THE CYBERSECURITY MATURITY MODEL CERTIFICATION (CMMC) BY DRAGOS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
FORENSIC INVESTIGATION OF NMAP SCAN WITH WIRESHARK BY IGNITE TECHNOLOGIES
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Open Source Tools
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Microsoft Active Directory – Security Self Assesment Guide 2022 by Huy Kha
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Complete Guide to Modernizing your Security Operations Centers (SOCs) by Microsoft and CyberProof
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Turning a Cybersecurity Strategy Into Reality – A Holistic Performance Management Framework by Boston Consulting Group & Saudi Telecomunication Company
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Enabling 5G Security with Continuos Monitoring by Booz Allen Hamilton
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The State of SIEM Detection Risk 2022 Report – Quantifying the gaps in MITRE ATT&CK coverage for productions SIEMs
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The CISOs Guide to Post-Quantum Standarization by QUANTINUUM
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Continuos Audit Metrics Catalog by Cloud Security Alliance CSA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity for Kids 2 by Joas Antonio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity for Kids 1 by Joas Antonio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
5G Cybersecurity by Dell
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Quantum Computing and Cybersecurity – Preparing for Post-Quantum Cryptography
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DOSfuscation – Exploring the Depths of Cmd.exe Obfuscation and Detection Techniques by FireEye
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...