The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Top 10 TED Talks to Learn about Cyber Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OWASP Top 10 2021 (DRAFT FOR PEER REVIEW) What´s New!!
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ITU – Mortal Fatality! – Latin America bombed in the Global Cybersecurity Index
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
FOR DUMMIES SERIES – INTRUSION PREVENTION SYSTEMS – download here !!
Learn to: Understand common networkthreats Select the right intrusionprevention system for yourcompany Figure out how an intrusionprevention system can fit intoyour organization’s network Views: 8
How CISOs and CIOs should share cybersecurity ownership
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
GIR – The Guide to Cyber Investigations.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISO2CISO VIDEO SERIES – ¿What is Your Password ?
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
“CISO Mind Map”, an interesting approach to talk about cyber & CISOs responsibilities in our organizations.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
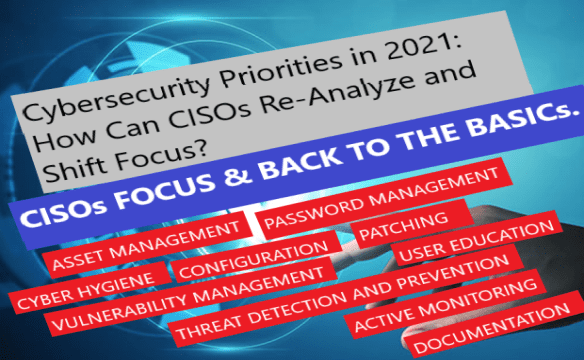
Cybersecurity CISOs priorities in 2021: focus and return to the basics
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
cisomag – Hardening Cyber Insurance Market Makes Cybersecurity More than a Tech Problem
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
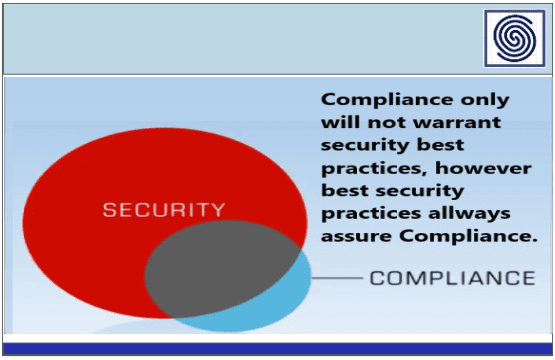
Compliance does not equal security !!
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ciso2ciso notepad series – new Released: new MITRE ATT&CK v10
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Guide to DevSecOps Tools and Continuous Security For an Enterprise by Navdeep Sing gill
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ciso2ciso notepad – checkpoint blog – Deepfakes, Cryptocurrency and Mobile Wallets: Cybercriminals Find New Opportunities in 2022
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A SANS 2021 survey – Security operations center
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity Basics Tips For Smalls Business
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Good practices for security OIT by enisa
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
90 DAYS A CISO´s Journey to Impact define your role !!
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Red Team Guide by Peerlyst – A practical guide for Red Teams and Offensive Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Applying Cyber Kill Chain® Methodology to Network Defense by Lockheed Martin
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Verizon 2022 DBIR Data Breach Investigations Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
IBM Security – Cost of a Data Breach Report 2021
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
RSA Conference 2022 Compendium: 150+ Interviews and More by SMG
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Sleeping with the enemy – A best practice guide for attacker engagement by Nick Klein.
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The State of API Security Q1 2022 Report from Salt Labs
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
100 Security Operation Tools for SOCs by Joas Antonio
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
21 OSINT Research Tools for Threat Intelligence
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Checklist for Effective Threat Hunting by SecurityHQ
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...