Source: www.infosecurity-magazine.com – Author: 1 The EU’s Cyber Resilience Act (CRA) could be misused by governments for intelligence or surveillance purposes, a group of industry experts...
Predator Spyware Linked to Madagascar’s Government Ahead of Presidential Election – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Madagascar government likely used the Cytrox-developed Predator spyware to conduct political domestic surveillance ahead of the country’s presidential election, according...
Upstream Supply Chain Attacks Triple in a Year – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security experts have warned of surging cyber risk in open source ecosystems, having detected three times more malicious packages in 2023...
Half of Cybersecurity Professionals Report Increase in Cyber-Attacks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Over half (52%) of cybersecurity professionals are experiencing an increase in cyber-attacks compared to a year ago, according to new research...
CyberEPQ Course Triples Student Intake for the Coming Year – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Chartered Institute of Information Security (CIISec) has said it hopes to enrol at least 400 students on its CyberEPQ course,...
Fifth of Brits Suspect They’ve Been Monitored by Employers – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Nearly one in five (19%) adults polled in a new survey from the UK’s privacy regulator think they’ve been monitored by...
San Francisco’s transport agency Metropolitan Transportation Commission (MTC) exposes drivers’ plate numbers and addresses – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini San Francisco’s transport agency Metropolitan Transportation Commission (MTC) exposes drivers’ plate numbers and addresses A misconfiguration in the Metropolitan Transportation...
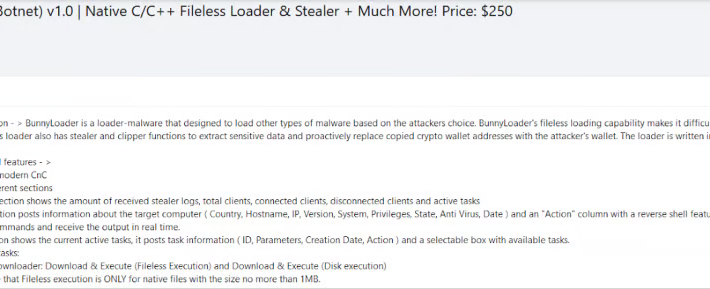
BunnyLoader, a new Malware-as-a-Service advertised in cybercrime forums – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini BunnyLoader, a new Malware-as-a-Service advertised in cybercrime forums Cybersecurity researchers spotted a new malware-as-a-service (MaaS) called BunnyLoader that’s appeared in the threat...
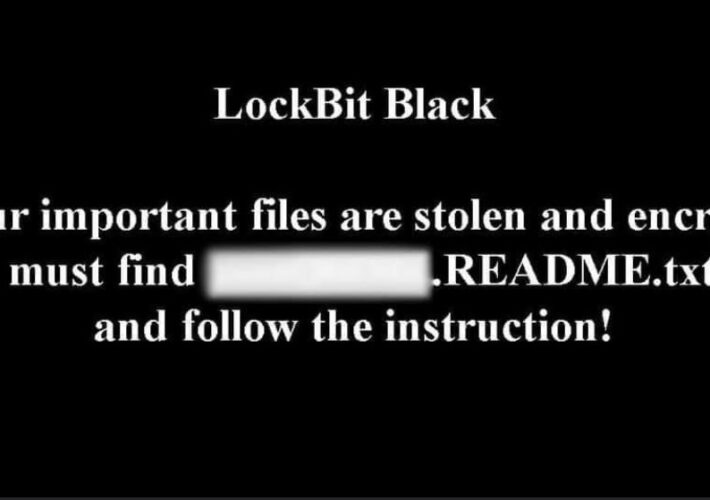
Exclusive: Lighting the Exfiltration Infrastructure of a LockBit Affiliate (and more) – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Exclusive: Lighting the Exfiltration Infrastructure of a LockBit Affiliate (and more) Researchers have identified the exfiltration infrastructure of a LockBit...
Two hacker groups are back in the news, LockBit 3.0 Black and BlackCat/AlphV – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Two hacker groups are back in the news, LockBit 3.0 Black and BlackCat/AlphV Researchers from cybersecurity firm TG Soft are warning Italian...
European Telecommunications Standards Institute (ETSI) suffered a data breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini European Telecommunications Standards Institute (ETSI) suffered a data breach The European Telecommunications Standards Institute (ETSI) disclosed a data breach, threat...
Browse Safer and Faster Around the World with JellyVPN — Now Just $34.99 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy on October 3, 2023, 6:02 AM EDT Browse Safer and Faster Around the World with JellyVPN — Now Just $34.99...
GDPR Data Breach Notification Letter – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: In the current business environment, it is almost inevitable that an organization will experience a security breach that exposes collected personal data...
Security Awareness and Training Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: A security policy is only as valuable as the knowledge and efforts of those who adhere to it, whether IT staff or...
Qualcomm Releases Patch for 3 new Zero-Days Under Active Exploitation – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 03, 2023THNZero Day / Vulnerability Chipmaker Qualcomm has released security updates to address 17 vulnerabilities in various components, while warning...
Warning: PyTorch Models Vulnerable to Remote Code Execution via ShellTorch – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 03, 2023THNArtificial Intelligence / Cyber Threat Cybersecurity researchers have disclosed multiple critical security flaws in the TorchServe tool for serving...
Over 3 Dozen Data-Stealing Malicious npm Packages Found Targeting Developers – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 03, 2023THNSoftware Security / Hacking Nearly three dozen counterfeit packages have been discovered in the npm package repository that are...
API Security Trends 2023 – Have Organizations Improved their Security Posture? – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 03, 2023The Hacker NewsAPI Security / Data Security APIs, also known as application programming interfaces, serve as the backbone of...
Protecting your IT infrastructure with Security Configuration Assessment (SCA) – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 03, 2023The Hacker NewsNetwork Security / XDR / SIEM Security Configuration Assessment (SCA) is critical to an organization’s cybersecurity strategy....
Hacking Gas Pumps via Bluetooth – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Hacking Gas Pumps via Bluetooth Turns out pumps at gas stations are controlled via Bluetooth, and that the connections...
New Malware-as-a-Service Gains Traction Among Cybercriminals – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici Security experts have discovered BunnyLoader, a malware-as-a-service (MaaS) that is rapidly evolving and gaining popularity on different hacker platforms due...
How to DDoS Like an Ethical Hacker – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Before I tell you how to DDoS someone, I want to make a few issues clear. Launching a Distributed Denial...
Nexusflow Slots AI into SOC Automation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer While ChatGPT and other large language model (LLM) applications are either praised as the next “sliced bread” or...
Secure Yeti Appoints Jayson E. Street as Chief Adversarial Officer to Spearhead Cybersecurity Empowerment – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 TULSA, Okla., Sept. 28, 2023 /PRNewswire/ — Secure Yeti, a leading global cybersecurity firm, proudly announces the appointment of renowned hacker Jayson E. Street as its first...
Visa Program Combats Friendly Fraud Losses For Small Businesses Globally – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SAN FRANCISCO — (BUSINESS WIRE) — Today, Visa Inc. (NYSE:V), a world leader in digital payments, spotlighted the evolution of its...
In Search of Rust Developers, Companies Turn to In-House Training – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading As the benefits of using memory-safe languages such as Rust become clearer, many organizations are shifting...
North Korea Poses as Meta to Deploy Complex Backdoor at Aerospace Org – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading North Korea’s state-sponsored Lazarus Group appears to have added a complex and still evolving new backdoor...
KillNet Claims DDoS Attack Against Royal Family Website – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading The official website of the UK royal family was subject to a distributed denial-of-service (DDoS) attack...
FBI: Crippling ‘Dual Ransomware Attacks’ on the Rise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The FBI has issued a warning about a rising ransomware trend in which separate attacks are conducted just...
Norway Urges Europe-Wide Ban on Meta’s Targeted Ad Data Collection – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A ban on mass Meta user data collection for advertising is set to expire next month in Norway,...