The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Powershell Tips & Tricks for r/b/p teamers
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Position-independent code
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CHEATSHEET PORT FORWARD & TUNNELLING
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Planning Considerations for Cyber Incidents
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Pipeline Security Guidelines
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Phishing Email Analysis
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Howto Improve Your Personal Cybersecurity
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Personnel Security Maturity Model
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Securing the code: navigating code and GitHub secrets scanning – Source: securityboulevard.com
Source: securityboulevard.com – Author: Itzik Alvas. Co-founder & CEO, Entro Welcome to the high-stakes world of GitHub, where your code isn’t just a collection of functions...
DEF CON 31 – Ceri Coburn’s ‘A Broken Marriage Abusing Mixed Vendor Kerberos Stacks’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/12/def-con-31-ceri-coburns-a-broken-marriage-abusing-mixed-vendor-kerberos-stacks/ Category & Tags: Security Bloggers Network,Cybersecurity,cybersecurity education,DEF...
MongoDB investigates a cyberattack, customer data exposed – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini MongoDB investigates a cyberattack, customer data exposed Pierluigi Paganini December 17, 2023 MongoDB on Saturday announced it is investigating a...
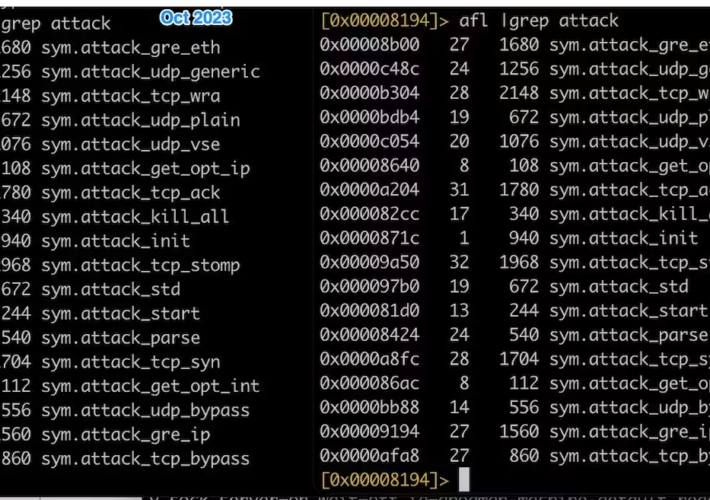
InfectedSlurs botnet targets QNAP VioStor NVR vulnerability – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini InfectedSlurs botnet targets QNAP VioStor NVR vulnerability Pierluigi Paganini December 17, 2023 The Mirai-based botnet InfectedSlurs was spotted targeting QNAP...
Security Affairs newsletter Round 450 by Pierluigi Paganini – INTERNATIONAL EDITION – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini MongoDB investigates a cyberattack, customer data exposed | InfectedSlurs botnet targets QNAP VioStor NVR vulnerability | Security Affairs newsletter Round...
MongoDB Confirms Hack, Says Customer Data Stolen – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine MongoDB CISO Lena Smart said the company was not aware of any exposure to the data that customers store in...
EXPLAINING PENETRATION TESTING
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Pentration Testing, Beginners To Expert!
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Conoce los nuevos requisitos obligatorios PCI DSS V.4
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Payment Card Industry Data Security Standard (PCI DSS) v4.0 on AWS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Process for Attack Simulation & Threat Analysis
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Passkeys: The End of Passwords?
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OWASP Top 10 Mobile Risks
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OSCP Cheat Sheet
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
OPERATION BLOCKBUSTER: Unraveling the Long Thread of the Sony Attack
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
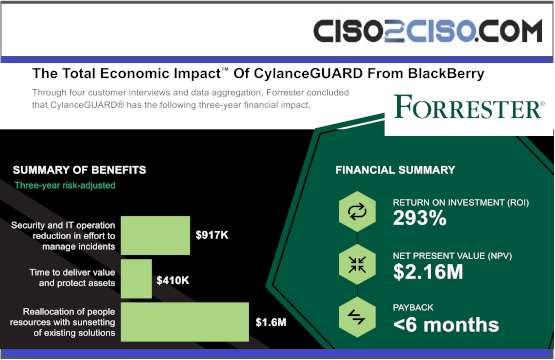
The Total Economic Impact™ Of Cylance GUARD From BlackBerry
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NIST PHISH SCALE USER GUIDE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Data Classification Concepts and Considerations for Improving Data Protection
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
NIS 2A Quick Reference Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Annual Review 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Enabling NATO’s Collective Defense: Critical Infrastructure Security and Resiliency
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...