Source: securityaffairs.com – Author: Pierluigi Paganini BMW dealer at risk of takeover by cybercriminals Pierluigi Paganini December 20, 2023 By neglecting to set a password, a...
Why RV Connex Chose Swimlane As “The Powerhouse” Of Their SOC – Source: securityboulevard.com
Source: securityboulevard.com – Author: Katie Bykowski RV Connex is a Thailand-based company that specializes in national defense and space manufacturing. Since RV Connex has implemented security...
Attackers Finding Novel Ways to Abuse GitHub: ReversingLabs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt Threat actors are finding new ways to take advantage of GitHub in hopes of tricking developers into putting malicious code...
CodeSecure Expands Automation Capabilities for Complying with Leading Embedded Software Safety and Security Standards – Source: securityboulevard.com
Source: securityboulevard.com – Author: Alison Napolitano CodeSonar static application security testing (SAST) tool now provides integrated support for meeting MISRA C 2023 and JSF++ for C++...
USENIX Security ’23 – Claudio Anliker, Giovanni Camurati, and Srdjan Čapkun ‘Time for Change: How Clocks Break UWB Secure Ranging’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, December 20, 2023 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Exploring EMBA: Unraveling Firmware Security with Confidence – Source: securityboulevard.com
Source: securityboulevard.com – Author: Paul Asadoorian Introduction Firmware security analysis is a critical aspect of modern cybersecurity. As our devices become more interconnected and reliant on...
AppOmni Previews Generative AI Tool to Better Secure SaaS Apps – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard AppOmni this week unveiled a technology preview of a digital assistant to its platform for protecting software-as-a-service (SaaS) applications that...
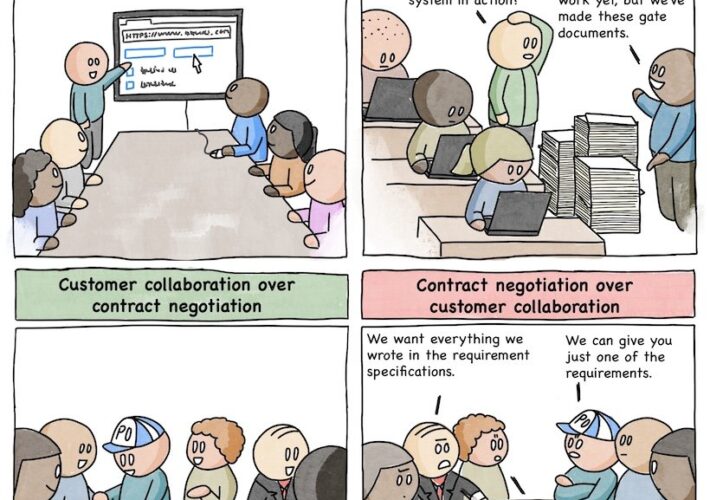
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #270 — The Agile Manifesto – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, December 20, 2023 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
Connecting the Dots: NIST SSDF, Self-Attestation, and a Complete ASPM Platform – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ronen Slavin In today’s hyper-connected world, secure software development is no longer an option, it’s a necessity. Yet achieving true security demands...
The Limitations of Google Play Integrity API (ex SafetyNet) – Source: securityboulevard.com
Source: securityboulevard.com – Author: George McGregor This overview outlines the history and use of Google Play Integrity API and highlights some limitations. We also compare and...
SSH FAIL: Terrapin Attack Smashes ‘Secure’ Shell Spec – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Lurking vuln in SSH spec means every implementation must build patches. A nasty vulnerability in a crucial bit of internet...
CISA Plans to Improve Threat Data-Sharing Approaches in 2024 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Government , Industry Specific , Next-Generation Technologies & Secure Development US Cyber Agency to Begin 2-Year Major Overhaul of Its Legacy...
NIST Seeks Public Comment on Guidance for Trustworthy AI – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Agency Calls for Information on Gen AI Risk Management, Red-Teaming...
Live Webinar | Enterprise Passkey Implementations: Key Considerations and Tradeoffs – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Live Webinar | A Master Class on IT Security: Roger Grimes Teaches Ransomware Mitigation – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware , Video Presented by KnowBe4 60 mins Cyber-criminals have become thoughtful...
UK Supreme Court Says AI Can’t Patent Inventions – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Court Says Only a ‘Person’ Can Be an Inventor Akshaya...
FTC Bans Rite Aid From Using Facial Recognition Tech – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Privacy , Standards, Regulations & Compliance 5-Year Ban Comes After Retailer Failed to Mitigate Security Surveillance...
FBI Disrupts BlackCat Ransomware Threat Group Activity – The Essential Facts – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși The U.S. Justice Department (DoJ) announced on December 19th that the Federal Bureau of Investigations had disrupted the BlackCat ransomware...
New JaskaGO Malware Stealer Threatens Windows and MacOS Operating Systems – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Security researchers discovered a new JaskaGO malware stealer that can infect both Windows and macOS. JaskaGO uses various methods to...
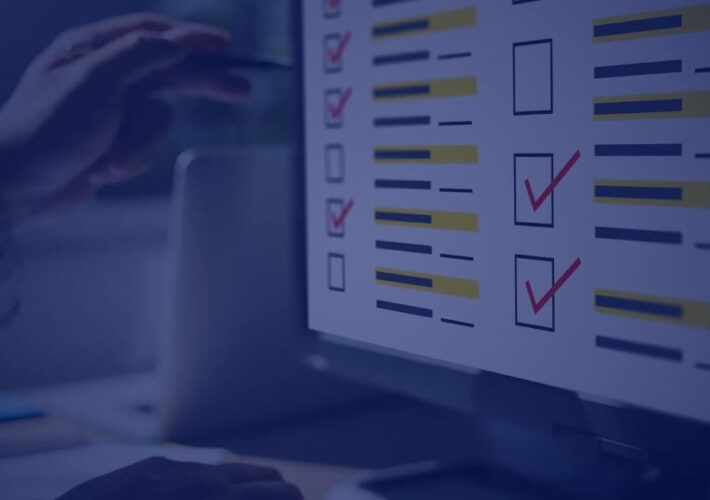
How to Complete an IT Risk Assessment (2023) – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu In a perfect world, you’d have the resources to defend yourself against every possible cybersecurity threat and vulnerability. The reality,...
What is the EPSS score? How to Use It in Vulnerability Prioritization – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși The Exploit Prediction Scoring System (EPSS) is a data-driven tool highlighting what vulnerabilities hackers will likely exploit. EPSS was created...
Ukraine’s Largest Telecommunication Provider Paralysed by a Massive Cyberattack – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu Kyivstar, Ukraine’s main provider of telecommunication services, says that it’s been the target of a ‘powerful hacker attack’. The attack...
Lazarus Hackers Exploit 2-Year-Old Log4j Vulnerability to Deploy New RAT Malware – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Researchers warn Lazarus threat actors still exploit known Log4j vulnerability to infect devices with new DLang malware strains. The new...
Remote Encryption Attacks Surge: How One Vulnerable Device Can Spell Disaster – Source:thehackernews.com
Source: thehackernews.com – Author: . Dec 20, 2023NewsroomNetwork Security / Data Breach Ransomware groups are increasingly switching to remote encryption in their attacks, marking a new...
Comcast Ties Breach Affecting 36M Customers to Citrix Bleed – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Governance & Risk Management , Patch Management Attackers Apparently Stole Authenticated Sessions to Hit Telecommunications Giant Mathew J....
BlackCat Ransomware ‘Unseizing’ a Dark Web Stunt – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Ransomware Ransomware Group Declares Nothing Off Limits Outside of CIS Countries David Perera (@daveperera) • December...
OpenAI Formulates Framework to Mitigate ‘Catastrophic Risks’ – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development A Preparedness Team Will Warn of Current, Future Dangers in...
Report Says CISA Is Failing to Identify High-Risk Exploits – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Security Operations CISA Did Not Include Critical Vulnerabilities in Known Exploit List, Report Says Chris Riotta (@chrisriotta) • December 19, 2023...
Okta to Acquire Israeli Startup Spera Security – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News Okta agreed to acquire Spera Security in a move broaden Okta’s Identity threat detection and security posture management capabilities. The...
Mozilla Patches Firefox Vulnerability Allowing Remote Code Execution, Sandbox Escape – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Firefox and Thunderbird security updates released this week address multiple memory safety bugs in both products. The post Mozilla Patches...