Source: securityboulevard.com – Author: hrbrmstr Hey folks, This is likely our last shot at preserving liberal democracy in the U.S., or at least avoiding 20–40 years...
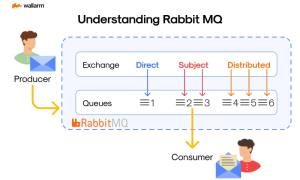
What is RabbitMQ? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ivan Novikov Grasping the Basics: What is RabbitMQ? Take a step into the realm of software development, where efficient and smooth interaction...
The Benefits of Employing AI in GRC – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michelle Ofir Geveye The narrative of technology surpassing human intelligence and altering the course of humanity is a recurring theme in science...
Insights from CISA HPH Sector Risk and Vulnerability Assessment – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rohan Timalsina In an ever-evolving digital landscape, the healthcare and public health (HPH) sector faces increasing cybersecurity challenges. The United States Cybersecurity...
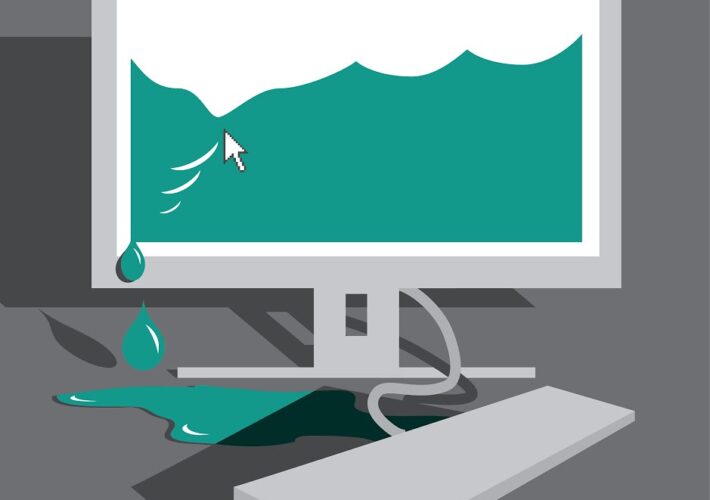
8 Essential Steps to Recover a Hacked Website – Source: securityboulevard.com
Source: securityboulevard.com – Author: TuxCare Team When you find out your website is hacked, it’s understandable that you’d begin to panic. But it’s much better to...
Happy New Year 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
MS Excel Vulnerability Exploited To Distribute Agent Tesla – Source: securityboulevard.com
Source: securityboulevard.com – Author: Wajahat Raja Threat actors with malicious intent have now been exploiting an old MS Excel vulnerability as part of their phishing campaign....
The Three Keys to Success in Cybersecurity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Tom Eston In this episode, host Tom Eston shares the three key lessons he’s learned over his 18-year career in cybersecurity: effective...
Cybersecurity Trends to Watch in 2024 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , AI-Based Attacks , API Security Expert Panelists Debate Impact of AI, Geopolitics and New Tactics in...
New Variant of DLL Search Order Hijacking Bypasses Windows 10 and 11 Protections – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 01, 2024NewsroomWindows Security / Vulnerability Security researchers have detailed a new variant of a dynamic link library (DLL) search order...
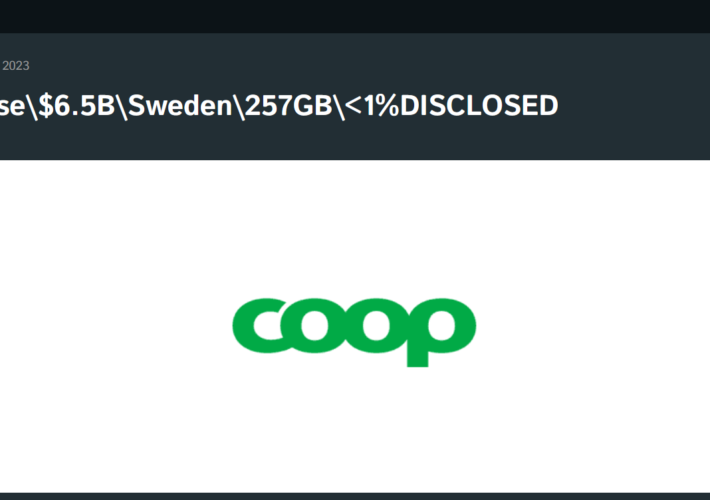
Cactus RANSOMWARE gang hit the Swedish retail and grocery provider Coop – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cactus RANSOMWARE gang hit the Swedish retail and grocery provider Coop The Cactus ransomware group claims to have hacked Coop,...
Google agreed to settle a $5 billion privacy lawsuit – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Google agreed to settle a $5 billion privacy lawsuit Pierluigi Paganini December 31, 2023 Google has agreed to settle a...
Android game dev’s Google Drive misconfig highlights cloud security risks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Japanese game developer Ateam has proven that a simple Google Drive configuration mistake can result in the potential but unlikely...
New Terrapin Flaw Could Let Attackers Downgrade SSH Protocol Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 01, 2024NewsroomEncryption / Network Security Security researchers from Ruhr University Bochum have discovered a vulnerability in the Secure Shell (SSH)...
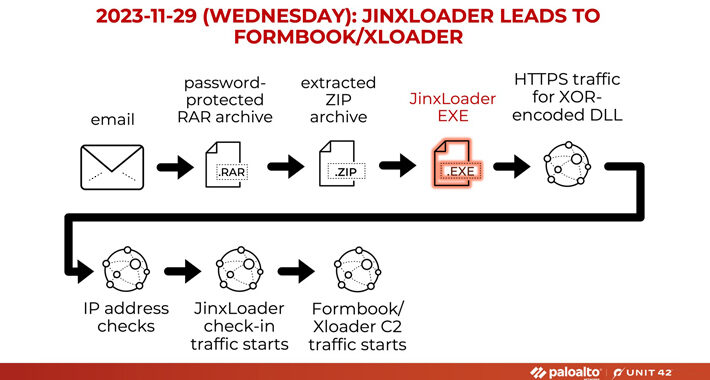
New JinxLoader Targeting Users with Formbook and XLoader Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 01, 2024NewsroomMalware / Dark Web A new Go-based malware loader called JinxLoader is being used by threat actors to deliver...
USENIX Security ’23 – Alexander Bienstock, Sarvar Patel, Joon Young Seo, Kevin Yeo ‘Near-Optimal Oblivious Key-Value Stores For Efficient PSI, PSU And Volume-Hiding Multi-Maps’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
Tech Security Year in Review – Source: securityboulevard.com
Source: securityboulevard.com – Author: Emma Kelly As we say goodbye to 2023, let’s look back on a year that has become a battleground in cybersecurity. The...
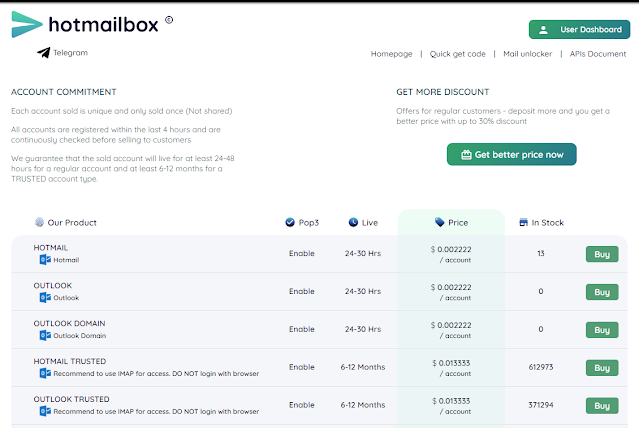
Vietnam’s Massive CAPTCHA crackers vs. Microsoft DCU – Source: securityboulevard.com
Source: securityboulevard.com – Author: Gary Warner Earlier this month, Microsoft’s Digital Crimes Unit was featured in a WIRED article by Lily Hay Newman – Microsoft’s Digital Crime...
Security Affairs newsletter Round 452 by Pierluigi Paganini – INTERNATIONAL EDITION – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Security Affairs newsletter Round 452 by Pierluigi Paganini – INTERNATIONAL EDITION | INC RANSOM ransomware gang claims to have breached...
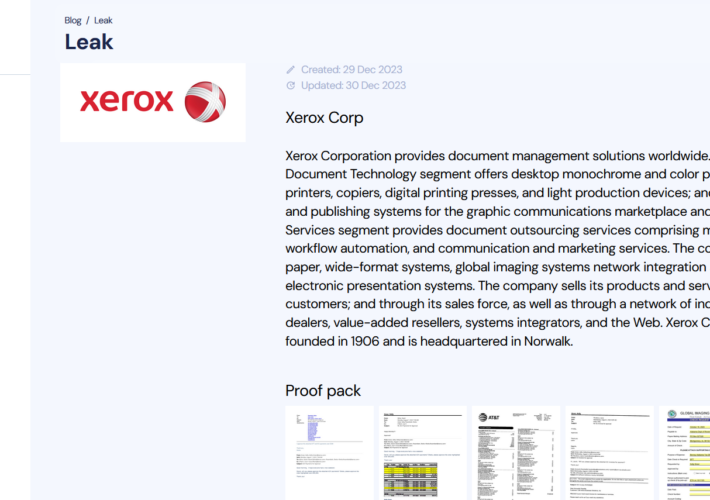
INC RANSOM ransomware gang claims to have breached Xerox Corp – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini INC RANSOM ransomware gang claims to have breached Xerox Corp Pierluigi Paganini December 30, 2023 The INC RANSOM ransomware group...
Google Settles $5 Billion Privacy Lawsuit Over Tracking People Using ‘Incognito Mode’ – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Google agreed to settle a $5 billion privacy lawsuit claiming that it continued spying on people who used the “incognito”...
Weekly Update 380 – Source: www.troyhunt.com
Source: www.troyhunt.com – Author: Troy Hunt We’re in Paris! And feeling proper relaxed after several days of wine and cheese too, I might add. This was...
USENIX Security ’23 – Mingli Wu, Tsz Hon Yuen ‘Efficient Unbalanced Private Set Intersection Cardinality And User-Friendly Privacy-Preserving Contact Tracing’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
2023 Year in Review: Hyperview Features and Enhancements – Source: securityboulevard.com
Source: securityboulevard.com – Author: Rajan Sodhi As we wrap up 2023, let’s take a moment to look back on the amazing journey we’ve had together this...
MFA For Small Businesses: How to Leverage Multi-Factor Authentication – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback Understanding MFA: A Security Necessity for Small Businesses In an age where cyber threats loom larger than ever, Multi-Factor Authentication...
How Honeytokens Can Detect and Stop Black Hat Computer Hackers – Source: securityboulevard.com
Source: securityboulevard.com – Author: Guest Expert Daniel Kelley Sponsorships Available Daniel Kelley is a security researcher with over 10 years of experience in threat intelligence, bug...
New Black Basta decryptor exploits ransomware flaw to recover files – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Researchers have created a decryptor that exploits a flaw in Black Basta ransomware, allowing victims to recover their files for...
Spotify music converter TuneFab puts users at risk – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Spotify music converter TuneFab puts users at risk Pierluigi Paganini December 30, 2023 TuneFab converter, used to convert copyrighted music...
Cyber attacks hit the Assembly of the Republic of Albania and telecom company One Albania – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cyber attacks hit the Assembly of the Republic of Albania and telecom company One Albania Pierluigi Paganini December 29, 2023...
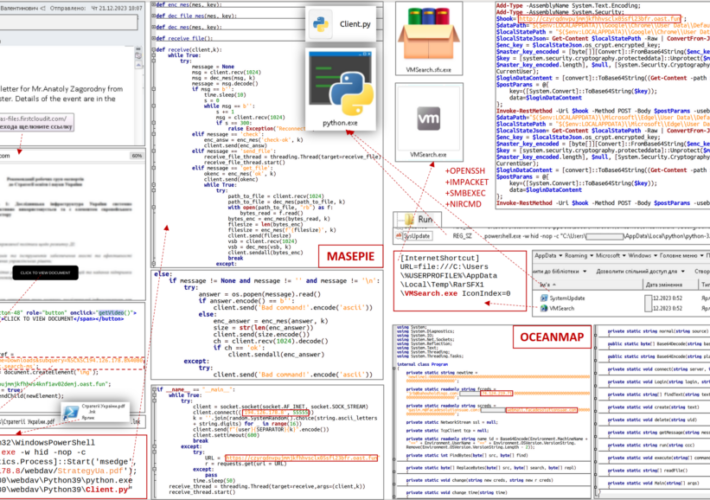
Russia-linked APT28 used new malware in a recent phishing campaign – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Russia-linked APT28 used new malware in a recent phishing campaign Pierluigi Paganini December 29, 2023 Ukraine’s CERT (CERT-UA) warned of...