Source: thehackernews.com – Author: . Jan 11, 2024NewsroomCybersecurity / Software Security The ubiquity of GitHub in information technology (IT) environments has made it a lucrative choice...
New PoC Exploit for Apache OfBiz Vulnerability Poses Risk to ERP Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 11, 2024NewsroomVulnerability / Cyber Attack Cybersecurity researchers have developed a proof-of-concept (PoC) code that exploits a recently disclosed critical flaw...
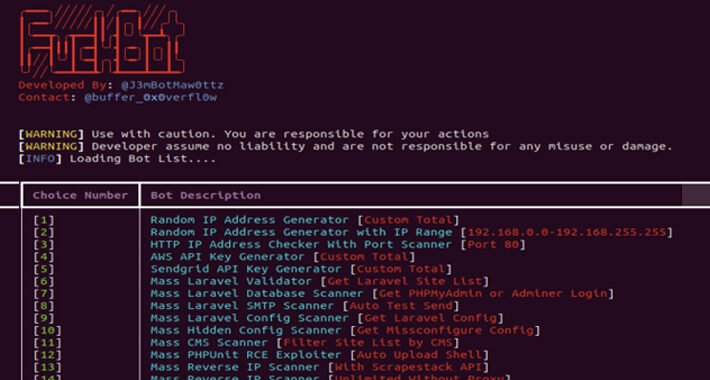
New Python-based FBot Hacking Toolkit Aims at Cloud and SaaS Platforms – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 11, 2024NewsroomCloud Security / Cyber Attacks A new Python-based hacking tool called FBot has been uncovered targeting web servers, cloud...
There is a Ransomware Armageddon Coming for Us All – Source:thehackernews.com
Source: thehackernews.com – Author: . Generative AI will enable anyone to launch sophisticated phishing attacks that only Next-generation MFA devices can stop The least surprising headline...
Atomic Stealer Gets an Upgrade – Targeting Mac Users with Encrypted Payload – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 11, 2024NewsroomMalvertising / Cyber Attacks Cybersecurity researchers have identified an updated version of a macOS information stealer called Atomic (or...
RCE تا XSS از (RCE from to XSS)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Framework discloses data breach after accountant gets phished – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Framework Computer disclosed a data breach exposing the personal information of an undisclosed number of customers after Keating Consulting Group,...
Over 150k WordPress sites at takeover risk via vulnerable plugin – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Two vulnerabilities impacting the POST SMTP Mailer WordPress plugin, an email delivery tool used by 300,000 websites, could help attackers take...
Halara probes breach after hacker leaks data for 950,000 people – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Popular athleisure clothing brand Halara is investigating a data breach after the alleged data of almost 950,000 customers was leaked...
Microsoft testing Windows 11 USB 80Gbps support, Copilot on login – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft is now testing support for the USB4 Version 2.0 specification in Windows 11, enabling transfer speeds of up to...
Bitwarden adds passkey support to log into web password vaults – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The open-source Bitwarden password manager has announced that all users can now log into their web vaults using a passkey...
Microsoft shares script to update Windows 10 WinRE with BitLocker fixes – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has released a PowerShell script to automate updating the Windows Recovery Environment (WinRE) partition in order to fix CVE-2024-20666,...
New Balada Injector campaign infects 6,700 WordPress sites – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A little over 6,700 WordPress websites using a vulnerable version of the Popup Builder plugin have been infected with the...
Finland warns of Akira ransomware wiping NAS and tape backup devices – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Finish National Cybersecurity Center (NCSC-FI) is informing of increased Akira ransomware activity in December, targeting companies in the country and wiping backups....
Researchers Flag FBot Hacking Tool Hijacking Cloud, Payment Services – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine The tool, called FBot, is capable of credential harvesting for spamming attacks, and AWS, PayPal and SaaS account hijacking. The...
Microsoft Lets Cloud Users Keep Personal Data Within Europe to Ease Privacy Fears – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Microsoft said that it is upgrading its cloud computing service to let customers store all personal data within the European...
Coming Soon to a Network Near You: More Shadow IoT – Source: www.securityweek.com
Source: www.securityweek.com – Author: Danelle Au Consumer IoT devices will increase the threat to commercial, government, healthcare, educational, and other organizations. The post Coming Soon to...
China-Linked Volt Typhoon Hackers Possibly Targeting Australian, UK Governments – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Chinese APT Volt Typhoon appears engaged in new attacks against government entities in the US, UK, and Australia. The post...
AI-Powered Misinformation is the World’s Biggest Short-Term Threat, Davos Report Says – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press False and misleading information supercharged with cutting-edge AI that threatens to erode democracy and polarize society, the World Economic Forum...
Intel, AMD, Zoom, Splunk Release Patch Tuesday Security Advisories – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Intel, AMD, Zoom and Splunk released security advisories on Patch Tuesday to inform customers about vulnerabilities found in their products....
CISA Urges Patching of Exploited SharePoint Server Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire CISA has added a critical Microsoft SharePoint Server flaw (CVE-2023-29357) to its Known Exploited Vulnerabilities catalog. The post CISA Urges...
Cisco Patches Critical Vulnerability in Unity Connection Product – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Cisco Unity Connection flaw could allow remote, unauthenticated attackers to upload arbitrary files and execute commands on the system. The...
Mandiant Details How Its X Account Was Hacked – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Mandiant’s X account was hacked as a result of a brute force attack as part of a cryptocurrency scheme that...
Secure Coding Practices
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SECURE CODING GUIDELINES
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Standards White Paper for Sino-German Industrie 4.0/Intelligent Manufacturing
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cybersecurity & Data Privacy Risk Management Model (C|P-RMM) Overview
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
SECURE CONTROLS FRAMEWORK (SCF) OVERVIEW & INSTRUCTIONS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
RISK FRAMEWORK FOR BODY-RELATED DATA IN IMMERSIVE TECHNOLOGIES
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
RedTeam scenarios
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...