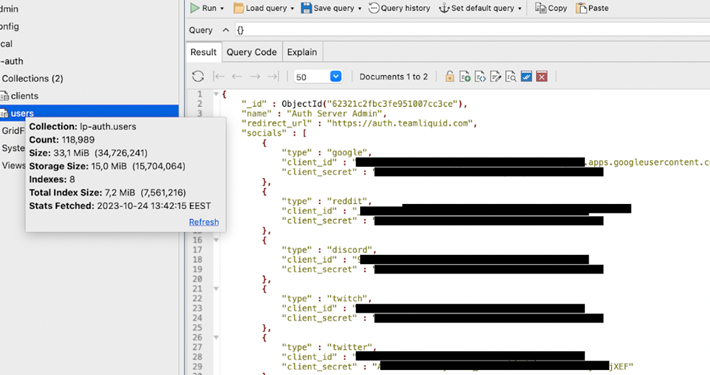
Source: securityaffairs.com – Author: Pierluigi Paganini Team Liquid’s wiki leak exposes 118K users Liquipedia, an online e-sports platform run by Team Liquid, exposed a database revealing...
The CISO’sGuide to YourFirst 100 Days
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Webinar: Solving the Bi-Directional Sync Problem with Microsoft Sentinel and D3 Smart SOAR – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shriram Sharma We’re looking forward to having you join us for our upcoming webinar on January 24th, at 10AM PST/1PM EST. It’s...
USENIX Security ’23 – Guanhong Tao, Shengwei An, Siyuan Cheng, Guangyu Shen, Xiangyu Zhang – Hard-Label Black-Box Universal Adversarial Patch Attack – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Network Security Security Bloggers Network Home » Cybersecurity » Network Security » USENIX Security ’23 – Guanhong Tao, Shengwei An, Siyuan...
Randall Munroe’s XKCD ‘Like This One’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Sift’s innovative journey: 40 patents and counting in the fight against evolving online fraud through AI, machine learning, and Workflows – Source: securityboulevard.com
Source: securityboulevard.com – Author: Neeraj Gupta The landscape of online fraud has undergone a profound transformation since the early days of the internet. Initially, simple rule-based...
5 Free Online Brand Protection Software Tools: Pros and Cons – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mitch W Online brand impersonation attacks threaten businesses large and small, but do brands really need to open their wallets to protect...
Joining My 5th Bot Mitigation Company – Why Kasada – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lucy McCue In October 2023, we welcomed Arif Husain to the team as our first Technical Director of Security Solutions. Arif has...
Before starting your 2024 security awareness program, ask these 10 questions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Seed and Soil Knowing this will allow you to have these customized groups and targeted training ready in advance, so teams don’t...
USENIX Security ’23 – Shibo Zhang, Yushi Cheng, Wenjun Zhu, Xiaoyu Ji, Wenyuan Xu – CAPatch: Physical Adversarial Patch against Image Captioning Systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Network Security Security Bloggers Network Home » Cybersecurity » Network Security » USENIX Security ’23 – Shibo Zhang, Yushi Cheng, Wenjun...
FCC Asks Carmakers, Carriers How They’re Protecting Abuse Survivors – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The Federal Communications Commission is pressing automakers and wireless service providers to say how they are protecting victims of domestic...
Ivanti VPN Zero-Day Combo Chained ‘by China’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Under active exploitation since last year—but still no patch available. A critical zero-day and another high-severity CVE are being chained together to...
CISA ROADMAP FOR ARTIFICIAL INTELLIGENCE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Catalogue of security measures GDPR
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Web ApplicationPenetration TestingTraining
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Boardroom Guide on Cybersecurity Governance and SEC info
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Amazon Appeals Privacy Fine of 746 Million Euros – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 General Data Protection Regulation (GDPR) , Standards, Regulations & Compliance E-Commerce Giant Accuses Luxembourg Regulators of Attacking the Company Akshaya Asokan...
Chinese Nation-State Hacker Is Exploiting Cisco Routers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Governance & Risk Management ‘Volt Typhoon’ Could Be Preparing for Renewed...
Live Webinar | Cybersecurity Strategies for Resource-Constrained State and Local Governments – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Jamie Tomasello Managing Director, Superbloom Jamie Tomasello (she/her and he/him) is a technology and policy leader with a strategic focus on...
US CISA Must Improve Water Sector Assistance, Says Watchdog – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security DHS Office of Inspector General Finds Lack of Coordination With EPA David Perera (@daveperera) • January 12, 2024...
Fertility Test Lab Will Pay $1.25M to Settle Breach Lawsuit – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , Industry Specific , Legislation & Litigation ReproSource Also Agrees to Beef Up Security in Wake of 2021 Ransomware Attack...
Nation-State Actors Weaponize Ivanti VPN Zero-Days, Deploying 5 Malware Families – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 12, 2024NewsroomVulnerability / Threat Intelligence As many as five different malware families were deployed by suspected nation-state actors as part...
Medusa Ransomware on the Rise: From Data Leaks to Multi-Extortion – Source:thehackernews.com
Source: thehackernews.com – Author: . The threat actors associated with the Medusa ransomware have ramped up their activities following the debut of a dedicated data leak...
Applying the Tyson Principle to Cybersecurity: Why Attack Simulation is Key to Avoiding a KO – Source:thehackernews.com
Source: thehackernews.com – Author: . Picture a cybersecurity landscape where defenses are impenetrable, and threats are nothing more than mere disturbances deflected by a strong shield....
Urgent: GitLab Releases Patch for Critical Vulnerabilities – Update ASAP – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 12, 2024NewsroomDevSecOps / Software security GitLab has released security updates to address two critical vulnerabilities, including one that could be...
Brad Arkin is New Chief Trust Officer at Salesforce – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News Veteran cybersecurity leader Brad Arkin has left Cisco and is joining Salesforce as SVP and Chief Trust Officer. The post...
Laptop Maker Framework Says Customer Data Stolen in Third-Party Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Device maker Framework is notifying users that their personal information was stolen in a data breach at its external accounting...
In Other News: WEF’s Unsurprising Cybersecurity Findings, KyberSlash Cryptography Flaw – Source: www.securityweek.com
Source: www.securityweek.com – Author: SecurityWeek News Noteworthy stories that might have slipped under the radar: WEF releases a cybersecurity report with unsurprising findings, and KyberSlash cryptography...
New Class of CI/CD Attacks Could Have Led to PyTorch Supply Chain Compromise – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Researchers detail a CI/CD attack leading to PyTorch releases compromise via GitHub Actions self-hosted runners. The post New Class of...
Russian Hackers Likely Not Involved in Attacks on Denmark’s Critical Infrastructure – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Researchers find no direct link between Russian APT Sandworm and last year’s attacks on Denmark’s critical infrastructure. The post Russian...