Source: www.bleepingcomputer.com – Author: Bill Toulas The Zoom desktop and VDI clients and the Meeting SDK for Windows are vulnerable to an improper input validation flaw...
New critical Microsoft Outlook RCE bug is trivial to exploit – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Update February 14, 16:50 EST: Article and title revised after Microsoft retracted the “active exploitation” update added to the CVE-2024-21413...
Microsoft Exchange update enables Extended Protection by default – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft is automatically enabling Windows Extended Protection on Exchange servers after installing this month’s 2024 H1 Cumulative Update (aka CU14)....
German battery maker Varta halts production after cyberattack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Battery maker VARTA AG announced yesterday that it was targeted by a cyberattack that forced it to shut down IT...
Ubuntu ‘command-not-found’ tool can be abused to spread malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A logic flaw between Ubuntu’s ‘command-not-found’ package suggestion system and the snap package repository could enable attackers to promote malicious...
Trans-Northern Pipelines investigating ALPHV ransomware attack claims – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Trans-Northern Pipelines (TNPI) has confirmed its internal network was breached in November 2023 and that it’s now investigating claims of...
DuckDuckGo browser gets end-to-end encrypted sync feature – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The DuckDuckGo browser has unveiled a new end-to-end encrypted Sync & Backup feature that lets users privately and securely synchronize...
Hackers used new Windows Defender zero-day to drop DarkMe malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has patched today a Windows Defender SmartScreen zero-day exploited in the wild by a financially motivated threat group to...
Ubuntu ‘command-not-found’ Tool Could Trick Users into Installing Rogue Packages – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 14, 2024NewsroomSoftware Security / Vulnerability Cybersecurity researchers have found that it’s possible for threat actors to exploit a well-known utility...
Cybersecurity Tactics FinServ Institutions Can Bank On in 2024 – Source:thehackernews.com
Source: thehackernews.com – Author: . The landscape of cybersecurity in financial services is undergoing a rapid transformation. Cybercriminals are exploiting advanced technologies and methodologies, making traditional...
Bumblebee Malware Returns with New Tricks, Targeting U.S. Businesses – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 14, 2024NewsroomMalware / Cybercrime The infamous malware loader and initial access broker known as Bumblebee has resurfaced after a four-month...
DarkMe Malware Targets Traders Using Microsoft SmartScreen Zero-Day Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 14, 2024NewsroomZero-Day / Financial Sector Security A newly disclosed security flaw in the Microsoft Defender SmartScreen has been exploited as...
Microsoft Rolls Out Patches for 73 Flaws, Including 2 Windows Zero-Days – Source:thehackernews.com
Source: thehackernews.com – Author: . Feb 14, 2024NewsroomPatch Tuesday / Vulnerability Microsoft has released patches to address 73 security flaws spanning its software lineup as part...
Cybersecurity Career Roadmap 2024 – Cybersecurity Career Roadmap: Paving the Path to Cyber Excellence
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Sec Resilience Guide Smart Energy Operat Environment
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISA – IACS Defence-in-Depth Strategies
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CEO-Level Guide and Checklist – Cybersecurity Leadership
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
BYOD Hidden Ransomware Threat
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Advanced Cybersecurity Practices 2024
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Acceptable Use Policy Template
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2023 Adversary Infrastructure Report
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
100 Free Cyber Security Tools
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
10 Cybersecurity New years resolutions for 2024
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Upcoming Speaking Engagements – Source: www.schneier.com
Source: www.schneier.com – Author: B. Schneier About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
Improving the Cryptanalysis of Lattice-Based Public-Key Algorithms – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier The winner of the Best Paper Award at Crypto this year was a significant improvement to lattice-based cryptanalysis. This is...
U.S. Internet Leaked Years of Internal, Customer Emails – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs The Minnesota-based Internet provider U.S. Internet Corp. has a business unit called Securence, which specializes in providing filtered, secure email services...
Fat Patch Tuesday, February 2024 Edition – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Microsoft Corp. today pushed software updates to plug more than 70 security holes in its Windows operating systems and related products,...
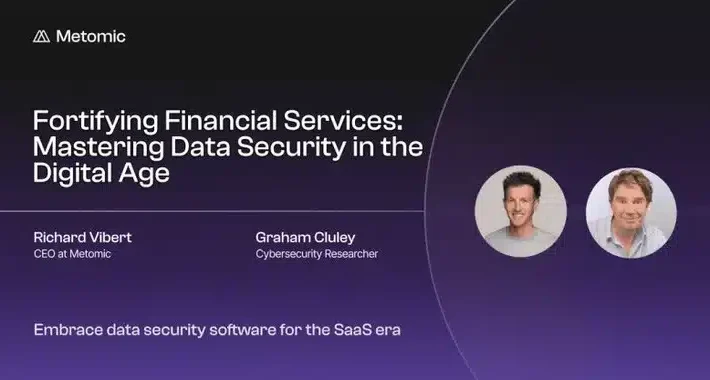
See me speak at webinar about data security for financial services – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Join me and Metomic CEO Richard Vibert for a discussion about some of the cybersecurity challenges faced by the financial...
What is a Passkey? Definition, How It Works and More – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Jonathan Kalibbala We may earn from vendors via affiliate links or sponsorships. This might affect product placement on our site, but not...
LogMeOnce Review (2024): Is It a Safe & Reliable Password Manager? – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Luis Millares LogMeOnce fast facts Our rating: 3.7 stars out of 5 Pricing: Starts at $2.50 per month Key features: Encrypted note-taking....