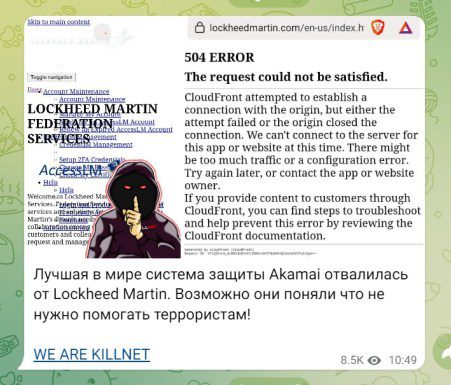
Killnet claims to have breached Lockheed MartinRussian hacker group Killnet claims to have launched a DDoS attack on the aerospace and defense giant Lockheed Martin. The...
Android Banking Trojan SOVA Comes Back With New Features Including Ransomware
Android Banking Trojan SOVA Comes Back With New Features Including RansomwareSOVA v4 features new capabilities and is reportedly targeting more than 200 mobile applicationsLeer másSOVA v4...
CISA Unveils Cybersecurity Toolkit to Shield US Elections From Hackers
CISA Unveils Cybersecurity Toolkit to Shield US Elections From HackersThe toolkit protects election infrastructure targeted by phishing, ransomware and DDoS attacksLeer másThe toolkit protects election infrastructure...
Recovery From NHS Ransomware Attack May Take a Month
Recovery From NHS Ransomware Attack May Take a MonthManaged service provider Advanced publishes update on recent cyber incidentLeer másManaged service provider Advanced publishes update on recent...
Zeppelin Ransomware Victims May Need Multiple Decryption Keys
Zeppelin Ransomware Victims May Need Multiple Decryption KeysCISA issues new alert about RaaS variantLeer másCISA issues new alert about RaaS variant
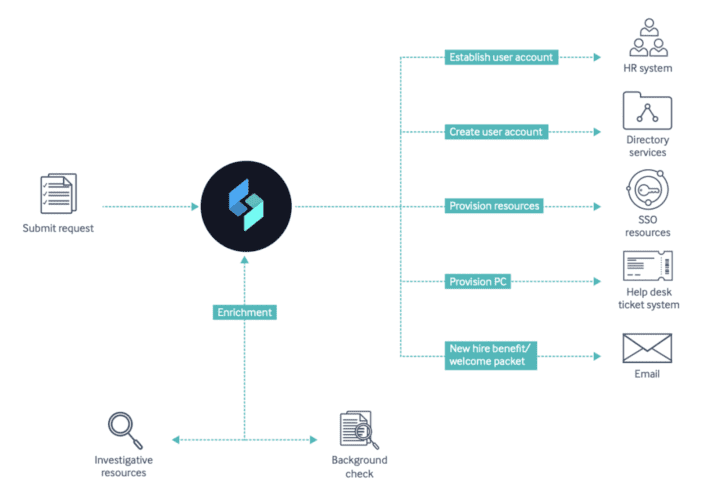
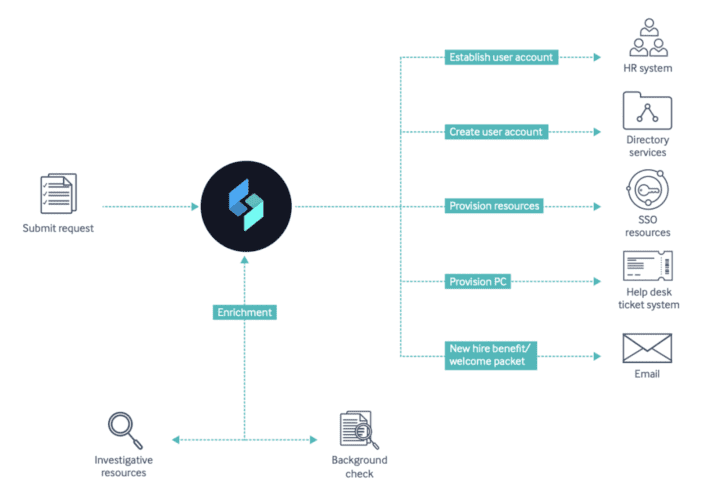
Why You Need to Automate Your Onboarding & Offboarding Process
Why You Need to Automate Your Onboarding & Offboarding ProcessThe growing threat landscape has made organizations rethink the way they handle business processes like onboarding and...
Why You Need to Automate Your Onboarding & Offboarding Process
Why You Need to Automate Your Onboarding & Offboarding ProcessThe growing threat landscape has made organizations rethink the way they handle business processes like onboarding and...
Aspen Security Forum 2022 – Led By Penny Pritzkerl – Virtual Fireside Chat with Secretary Gina Raimondo
Aspen Security Forum 2022 – Led By Penny Pritzkerl – Virtual Fireside Chat with Secretary Gina RaimondoLed by Penny Pritzkerl Secretary Gina Raimondo, 40th Secretary, U.S....
Aspen Security Forum 2022 – Moderator: Edward Luce – Global Economy: Recovery Or Recession Bound?
Aspen Security Forum 2022 – Moderator: Edward Luce – Global Economy: Recovery Or Recession Bound?In Collaboration with the Aspen Economic Strategy Group Zoë Baird, CEO and...
Tornado Cash Developer Arrested After U.S. Sanctions the Cryptocurrency Mixer
Tornado Cash Developer Arrested After U.S. Sanctions the Cryptocurrency MixerDutch authorities on Friday announced the arrest of a software developer in Amsterdam who is alleged to...
Chinese Hackers Backdoored MiMi Chat App to Target Windows, Linux, macOS Users
Chinese Hackers Backdoored MiMi Chat App to Target Windows, Linux, macOS UsersA pair of reports from cybersecurity firms SEKOIA and Trend Micro sheds light on a new campaign undertaken by...
Black Hat 2022 — End-to-End Fun and API Security
Black Hat 2022 — End-to-End Fun and API SecurityIt’s a wrap on Black Hat 2022! Thank you to everyone who visited the Cequence Security team at...
Daniel Stori’s ‘arduino project’
Daniel Stori’s ‘arduino project’ via the inimitable Daniel Stori, crafting superb comics at turnoff.us! The post Daniel Stori’s ‘arduino project’ appeared first on Security Boulevard. Leer...
This was H1 2022: Part 2 – Cyber War
This was H1 2022: Part 2 – Cyber WarOn February 24, 2022, news broke that Russia had initiated its special military operation against Ukraine. That date,...
Cisco Pwned by ‘Russian’ Gang — Data Leaked, Egg on Face
Cisco Pwned by ‘Russian’ Gang — Data Leaked, Egg on Face Cisco got hacked by a ransomware gang—a broker for the UNC2447 threat actor, which has...
Black Hat 2022: from cyberwarfare to the rise of RCE
Black Hat 2022: from cyberwarfare to the rise of RCEBlack Hat 2022 is coming to a close, and we’re leaving the conference with fresh industry insights,...
This Week in Malware – Fileless Linux Cryptominer, 100 Packages
This Week in Malware – Fileless Linux Cryptominer, 100 Packages This week in malware we discovered and analyzed nearly 100 packages flagged as malicious, suspicious, or...
Aspen Security Forum 2022 – Imagining The Next 9/11: What Future Scares Us Most, What Can We Do to Prevent It from Coming True?
Aspen Security Forum 2022 – Imagining The Next 9/11: What Future Scares Us Most, What Can We Do to Prevent It from Coming True?Miriam Krieger, Permanent...
SafeBreach Coverage for US-CERT Alert (AA22-223A) – Zeppelin Ransomware
SafeBreach Coverage for US-CERT Alert (AA22-223A) – Zeppelin RansomwareLearn more about these enhancements to the SafeBreach platform that validate deployed security controls, by industry, against these...
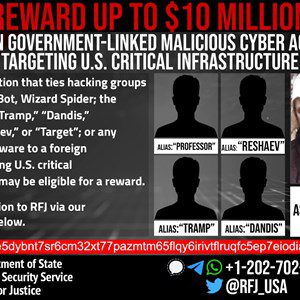
U.S. Government Offers $10 Million Reward for Information on Conti Ransomware Gang
U.S. Government Offers $10 Million Reward for Information on Conti Ransomware GangThe U.S. State Department on Thursday announced a $10 million reward for information related to five individuals...
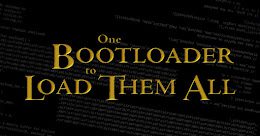
Researchers Uncover UEFI Secure Boot Bypass in 3 Microsoft Signed Boot Loaders
Researchers Uncover UEFI Secure Boot Bypass in 3 Microsoft Signed Boot LoadersA security feature bypass vulnerability has been uncovered in three signed third-party Unified Extensible Firmware Interface...
A Modern Database Meets a Modern DevOps Data Platform
A Modern Database Meets a Modern DevOps Data PlatformA Modern Database Meets a Modern DevOps Data Platform jasonaxelrod Fri, 08/12/2022 - 12:50 Delphix and Cockroach Labs...
S3 Ep95: Slack leak, Github onslaught, and post-quantum crypto [Audio + Text]
S3 Ep95: Slack leak, Github onslaught, and post-quantum crypto [Audio + Text]Latest episode - listen now! (Or read the transcript if you prefer.)Leer másNaked SecurityLatest episode...
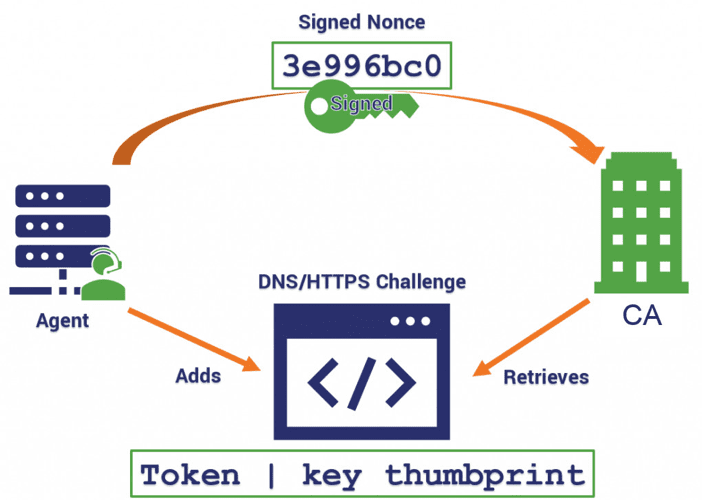
What is the Automated Certificate Management Environment (ACME) Protocol?
What is the Automated Certificate Management Environment (ACME) Protocol?What is the Automated Certificate Management Environment (ACME) Protocol? kdobieski Fri, 08/12/2022 - 17:00 4104 views How does...
US Unmasks Suspected Conti Ransomware Actor
US Unmasks Suspected Conti Ransomware ActorState Department offers $10m reward for info on notorious groupLeer másState Department offers $10m reward for info on notorious group
New exploits can bypass Secure Boot and modern UEFI security protections
New exploits can bypass Secure Boot and modern UEFI security protectionsTwo teams of researchers have revealed vulnerabilities this week in Unified Extensible Firmware Interface (UEFI) implementations...
#BHUSA: What has Changed in the Post-Stuxnet Era?
#BHUSA: What has Changed in the Post-Stuxnet Era?Investigative journalist Kim Zetter explains that Stuxnet continues to serves as a precedent for attacks happening nowLeer másInvestigative journalist...
#BHUSA: Bug Bounty Botox – Why You Need a Security Process First
#BHUSA: Bug Bounty Botox – Why You Need a Security Process FirstKatie Moussouris explains why simply having a bug bounty program isn't enough to fix security...
Facebook’s In-app Browser on iOS Tracks ‘Anything You Do on Any Website’
Facebook’s In-app Browser on iOS Tracks ‘Anything You Do on Any Website’Researcher shows how Instagram and Facebook’s use of an in-app browser within both its iOS...
Safety first: how to tweak the settings on your dating apps
Safety first: how to tweak the settings on your dating appsTinder, Bumble or Grindr - popular dating apps depend heavily on your location, personal data, and...